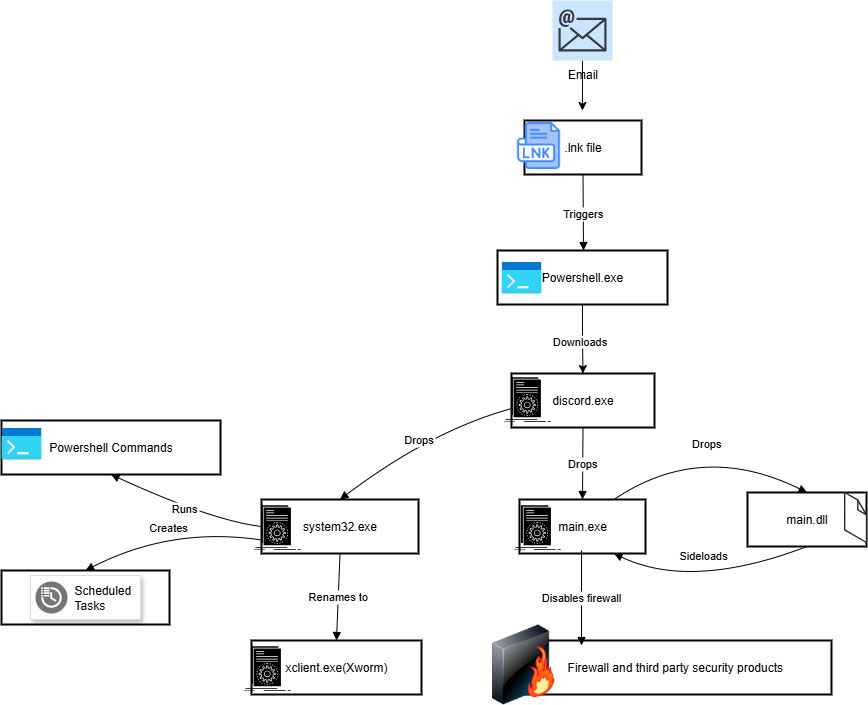
Trellix ARC identifies an evolved XWorm campaign using deceptive multi-stage delivery—malicious .lnk files drop a fake discord.exe which installs main.exe and system32.exe (the XWorm payload), employing packing, registry persistence, scheduled tasks, PowerShell exclusions, and Rijndael+Base64 cryptography. Key artifacts include filenames and MD5 hashes for components and a C2 at 85[.]203[.]4[.]232 used to deliver Discord.exe; Trellix products provide detections for these components. #XWorm #Discord.exe
Keypoints
- .lnk shortcut phishing is used to run a Base64-encoded PowerShell command that drops payload.txt and downloads discord.exe from hxxp://85[.]203[.]4[.]232:5000/Discord.exe.
- discord.exe (packed .NET) drops main.exe and system32.exe, then launches them; system32.exe is the XWorm backdoor and uses Xclient.exe for persistence.
- main.exe is heavily packed, drops .pyd modules and main.dll (single export run_code, with TLS callbacks), disables Windows Firewall via a registry policy key, and executes early via TLS callbacks.
- XWorm performs sandbox/virtualization checks and self-terminates in virtual environments, creates a mutex (1JJyHGXN8Jb9yEZG), and gathers host reconnaissance information.
- Persistence is achieved through a scheduled task “XClient” running every minute and a Run registry entry at HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunXClient.
- Malware uses Base64 decoding combined with Rijndael (AES) decryption to protect and reveal C2 addresses, configuration and commands used by the backdoor.
- Backdoor capabilities include system shutdown/restart, file download, opening URLs, launching DDoS, and remote command execution; Trellix products claim detections across endpoint, network, email, and EDR layers.
MITRE Techniques
- [T1204.002 ] User Execution: Malicious File – The campaign uses malicious shortcut (.lnk) files delivered via phishing to execute PowerShell and start the infection chain. Quote: ‘Executing the .lnk file initiates a malicious PowerShell script… connects to (hxxp://85[.]203[.]4[.]232:5000/Discord.exe)’.
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell is invoked with Base64-encoded commands and ExecutionPolicy Bypass to download and run discord.exe and add MpPreference exclusions. Quote: ‘ExecutionPolicy Bypass Add-MpPreference -ExclusionPath’ and ‘Executed Obfuscated PowerShell Base64String command’.
- [T1027 ] Obfuscated Files or Information – Multiple layers of Base64 encoding and Rijndael decryption are used to conceal C2 and configuration strings. Quote: ‘Base64-encoded strings are fed into the Rijndael decryptor for final decryption.’
- [T1562.001 ] Impair Defenses: Disable or Modify Security Tools – main.exe creates a registry entry at HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsFirewallDisableFirewall to disable Windows Firewall. Quote: ‘The malware achieves firewall disablement by creating a specific registry entry… DisableFirewall’.
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – The malware adds a Run key at HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunXClient for persistence. Quote: ‘The entry is located at HKEY_CURRENT_USERSOFTWAREMicrosoftWindowsCurrentVersionRunXClient’.
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – XWorm creates a scheduled task “XClient” using schtasks.exe to run every minute for persistence. Quote: ‘”C:WindowsSystem32schtasks.exe” /create /f /RL HIGHEST /sc minute /mo 1 /tn “XClient” /tr’.
- [T1497.001 ] Virtualization/Sandbox Evasion: System Checks – The .NET executable checks for virtual environments and self-terminates using failfast if detected to evade analysis. Quote: ‘It then checks for virtual environments… the executable self-terminates using a “.failfast” mechanism’.
- [T1040 ] Network Sniffing / Command and Control – The malware decodes and uses C2 data (IP addresses, domains, ports) discovered via decryption to communicate with operators. Quote: ‘This includes crucial Command and Control (C2) data—such as IP addresses, domain names, and server port numbers’.
- [T1059 ] Command and Scripting Interpreter (general) – Use of PowerShell to manipulate execution policy and exclusion lists to avoid detection. Quote: ‘ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess’.
- [T1136 ] Create Account / Mutex (process exclusion) – The malware creates a mutex ‘1JJyHGXN8Jb9yEZG’ to ensure a single instance runs and avoid duplication. Quote: ‘The malware creates a mutex named “1JJyHGXN8Jb9yEZG”.’
Indicators of Compromise
- [MD5 ] sample file hashes – c2f66498298c1af28da64eb5392a4a6e (lnk file), 4e98e45377fbf1390676ca36dbef0b85 (Discord.exe)
- [MD5 ] additional file hashes – cb3241ff094bb1292dc7841148a7431e (main.exe), 7c1129af104acf9cc4c0793077e9c5df (main.dll), and 72eb8c4ffd6d5f721ed3ee121264b53f (System32.exe)
- [File names ] malware and dropped files – .lnk file (initial), Discord.exe (downloader/loader), main.exe and system32.exe (XWorm payload), main.dll (run_code export)
- [Domain/IP ] C2 and download source – 85[.]203[.]4[.]232 (C2 / host serving Discord.exe via hxxp://85[.]203[.]4[.]232:5000/Discord.exe)
- [Registry keys ] persistence and defense manipulation – HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindowsFirewallDisableFirewall (disable firewall), HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunXClient (autostart)