The leaked “Kim” dataset reveals a credential-first APT campaign attributed to a North Korean–aligned operator (Kimsuky/“Kim”) that used OCR, AiTM phishing, and manual malware development to target South Korean GPKI systems and Taiwanese developer/cloud infrastructure. Artifacts include compiled NASM shellcode, Linux kernel rootkit modules (vmmisc.ko/VMmisc.ko) with syscall hooking, phishing domains like nid-security[.]com, and IPs linked to reconnaissance and brute-force activity. #Kimsuky #vmmisc.ko
Keypoints
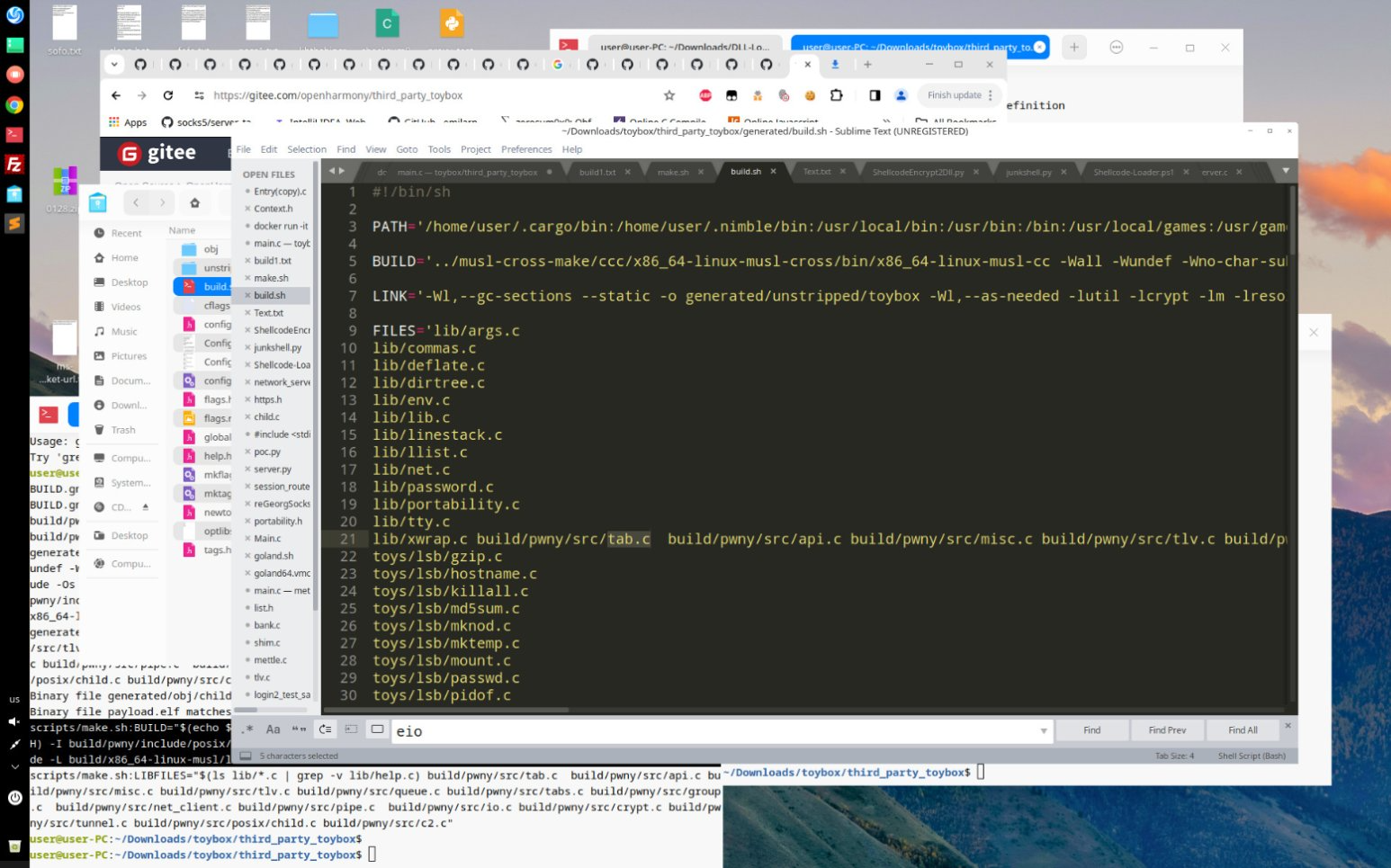
- Leak contains operational artifacts (bash histories, compiled stagers, OCR runs, PAM logs) showing hands‑on malware development and testing with NASM and make/rm workflows.
- Credential theft and GPKI compromise are central: leaked .key files (e.g., 136백운규001_env.key) and plaintext passwords indicate exfiltrated South Korean government certificates.
- Extensive phishing/AiTM infrastructure mimicked Korean government portals (nid-security[.]com, webcloud-notice[.]com) and used TLS-proxy interception and burner emails (e.g., jeder97271[@]wuzak[.]com).
- Rootkit implant (vmmisc.ko/VMmisc.ko) provides kernel-level stealth (syscall hooking), SOCKS5 proxying, PTY backdoor shells, encrypted session activation, and client↔kernel command set for persistence and covert C2.
- Reconnaissance extended to Taiwan: crawling .git/ endpoints and accessing domains like caa.org[.]tw/.git/ and tw.systexcloud[.]com to harvest developer secrets and target cloud login portals.
- Infrastructure and logs show mixed DPRK and PRC signals (Korean-language targeting, simplified Chinese browsing, use of gitee/baidu), supporting a hybrid attribution model—a DPRK operator embedded in or using Chinese infrastructure.
- Recommended defenses: protect PKI keys (HSM/2FA), block IoC domains/IPs, monitor OCR/toolchain usage (nasm, ocrmypdf), watch .git access, and audit admin accounts (oracle, svradmin, app_adm01).
MITRE Techniques
- [T1566.002] Adversary-in-the-Middle (AiTM) Phishing – Used AiTM phishing infrastructure and TLS proxies to capture credentials in real time (“phishing kits leveraged TLS proxies for AiTM credential capture”).
- [T1059.005] Native API Shellcode – Manual shellcode compiled with NASM for Win32 targets to execute native API calls (“Manual shellcode compilation via nasm -f win32 source/asm/x86/start.asm”).
- [T1059.003] Bash/Shell Scripts – Use of shell commands and scripted build/cleanup workflows evident in .bash_history (e.g., make, rm) to automate builds and sanitization (“make and rm were used to automate and sanitize builds”).
- [T1555] Credential Store Dumping – Exfiltration of .key/.crt files and plaintext passwords from GPKI material (e.g., 136백운규001_env.key) showing compromised certificate stores (“Leaked .key files (e.g., 136백운규001_env.key) with plaintext passwords confirm access to GPKI systems”).
- [T1557.003] Session Hijacking – Use of AiTM and proxy interception to capture and reuse session credentials (phishing domains and TLS proxying to intercept logins noted above).
- [T1176] Rootkit – Deployment of kernel-mode implant vmmisc.ko using syscall hooking (khook) to hide files/processes and provide covert networking (“Linux rootkit code using syscall hooking and covert channel deployment”).
- [T1562.001] Disable Security Tools – Rootkit designed to bypass detection tools like chkrootkit and rkhunter by hiding network ports, processes, and files (“Tools like chkrootkit, rkhunter… are bypassed through technical evasion and hiding”).
- [T1552] Unsecured Credential Files – Presence of plaintext password‑protected .key files and credentials stored in accessible files (“Leaked .key files… with plaintext passwords”).
- [T1592] Technical Information Discovery – OCR of Korean PKI and VPN PDFs to extract technical specifications for spoofing and tool emulation (“ocrmypdf -l kor+eng ‘file.pdf’ to parse PKI and VPN documents”).
- [T1590] Network Service Scanning – Reconnaissance of .git directories and cloud login portals in Taiwan to enumerate developer secrets and services (“attempts to crawl .git repositories” and access to tw.systexcloud[.]com, mlogin.mdfapps[.]com).
- [T1041] Exfiltration Over C2 Channel – Use of covert channels and rootkit SOCKS5 proxying for remote networking and potential exfiltration (“SOCKS5 Proxy: Integrated remote networking capability using dynamic port forwarding”).
- [T1567.002] Exfiltration via Cloud Services – Use of public paste/pastebin and GitHub/Gitee hosting for tooling/payload staging and possible exfiltration (“GitHub tools in use: TitanLdr, minbeacon… Pastebin raw links: Used for payload staging and malware delivery”).
Indicators of Compromise
- [Domain] phishing/spoof infrastructure – nid-security[.]com, webcloud-notice[.]com (domains mimicking Korean government/document services; used for AiTM credential capture).
- [Domain] spoofed government portals – dcc.mil[.]kr, spo.go[.]kr (mimicked to harvest credentials and lure targets).
- [File name] compromised PKI material – 136백운규001_env.key (stolen South Korean GPKI .key file with plaintext password), additional .crt/.sig files referenced.
- [Filename / Binary] rootkit modules and client – vmmisc.ko / VMmisc.ko, client (kernel implant and associated controller used for persistence and covert C2).
- [IP address] brute-force / staging nodes – 23.95.213[.]210, 218.92.0[.]210 (VPS/China Unicom used for credential-stuffing and scanning); and 122.114.233[.]77 (Henan Mobile) recorded during SSH attempts.
- [IP address] Taiwanese targets – 163.29.3[.]119, 118.163.30[.]45 (Taiwan government/institution subnets), 59.125.159[.]81 (Chunghwa Telecom) observed during targeted reconnaissance.
- [Internal IPs] operator environment – 192.168.0[.]39, 192.168.130[.]117 (internal/private hosts used for local staging and testing seen in deployment logs).