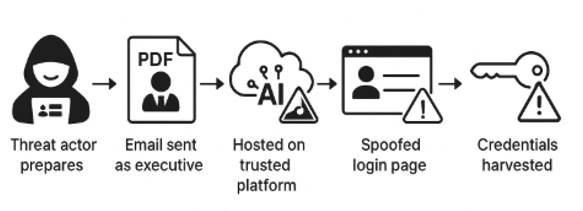
Threat actors hosted a phishing page on the legitimate Simplified AI platform and used a password-protected PDF that redirected victims to a spoofed Microsoft 365 login to harvest credentials. The campaign targeted US organizations, was detected and contained by Cato MDR in July 2025, and leveraged app.simplified.com to bypass defenses. #SimplifiedAI #Microsoft365
Keypoints
- Threat actors used a password-protected PDF to bypass email security and included the password in the email body to ensure user access.
- The PDF impersonated an executive from a global pharmaceutical distributor, using real branding and names verified via LinkedIn.
- Clicking the PDF link redirected victims to app.simplified.com (a legitimate Simplified AI domain) which hosted the phishing webpage.
- The Simplified-hosted page redirected victims to a spoofed Microsoft 365 login portal designed to harvest enterprise credentials.
- The campaign targeted US-based organizations in July 2025; one US investment organization was targeted but the attack was detected and contained before further compromise.
- Attackers abused the reputation of a trusted AI platform to evade traditional defenses and avoid using suspicious domains or servers.
- Cato MDR and SASE Cloud provided AI-aware visibility, detection, and response to identify and mitigate the phishing campaign.
MITRE Techniques
- [T1193] Spearphishing Attachment – Used a password-protected PDF attachment to deliver the lure and evade automated email scanners. Quote: ‘the phishing email arrived with a password-protected PDF attachment… the password itself was conveniently included in the email body.’
- [T1598] Compromise Infrastructure – Abuse of legitimate third-party service (Simplified AI) to host phishing content and redirect victims. Quote: ‘Clicking the link led the victim to app.simplified.com… hosted on Simplified AI’s platform.’
- [T1189] Drive-by Compromise / Phishing for Credentials (Credential Harvesting) – Redirected users to a spoofed Microsoft 365 login portal to capture usernames and passwords. Quote: ‘the victim was redirected once more, this time to a spoofed Microsoft 365 login portal… Any usernames and passwords entered would have been transmitted directly to the threat actors.’
- [T1592] Trusted Relationship – Exploited implicit trust and whitelisting of widely used AI platforms to bypass defenses. Quote: ‘For most organizations, such domains are already whitelisted or implicitly trusted, making this redirection highly effective at avoiding detection.’
Indicators of Compromise
- [URL] Simplified AI redirect – http[:]//app.simplified.com/preview/911e411b-6f9b-41d0-845f-0cc291d07c7e
- [URL] Final credential-harvest page – https[:]//pub-6ea00088375b43ef869e692a8b2770d2.r2[.]dev/assets/php/endpoints/account.php
- [IP Address] Associated infrastructure – 104.18.50.34