ESET identified a previously unknown, China-aligned threat actor named GhostRedirector that compromised at least 65 Windows servers and deployed custom tools Rungan (a C++ backdoor) and Gamshen (a malicious native IIS module for SEO fraud). The campaign used public exploits (EfsPotato, BadPotato), multiple custom utilities, and staging domains such as 868id[.]com to manipulate Google search results and promote third-party gambling sites. #GhostRedirector #Rungan #Gamshen #868id
Keypoints
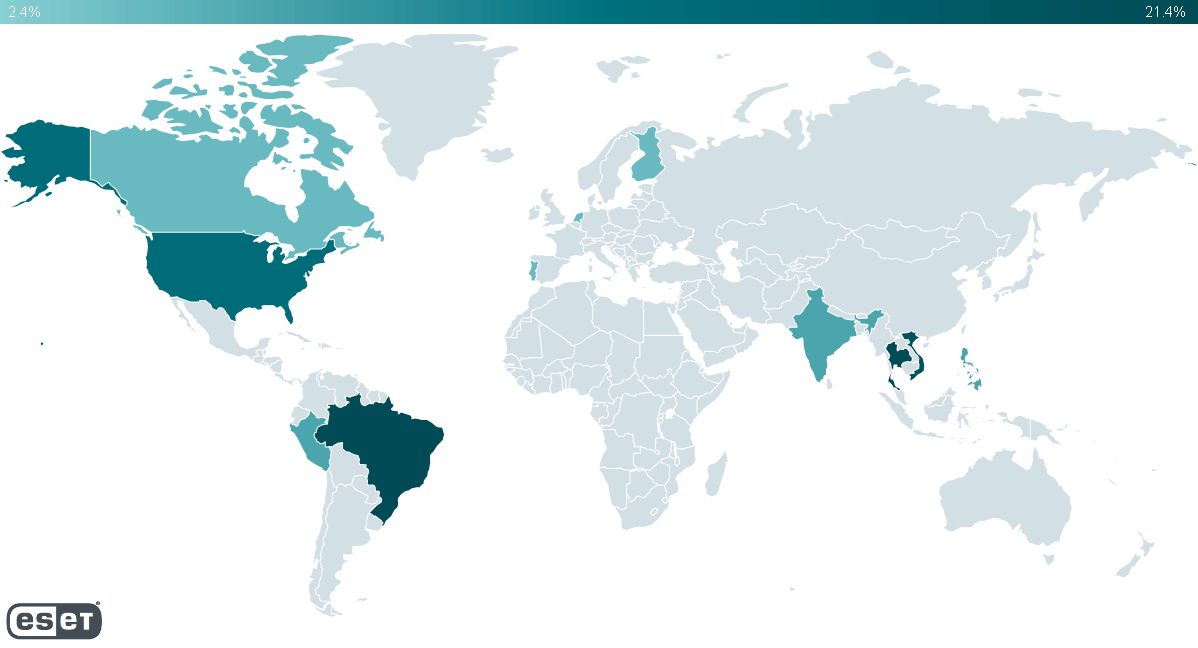
- At least 65 Windows servers were compromised between December 2024 and June 2025, primarily in Brazil, Thailand, Vietnam, Peru, and the USA.
- GhostRedirector developed two undocumented custom tools: Rungan (passive C++ backdoor) and Gamshen (malicious native IIS module performing SEO fraud).
- Initial access likely via SQL injection followed by PowerShell or certutil to download payloads from the staging domain 868id[.]com.
- Privilege escalation relied on public exploits (EfsPotato, BadPotato) and custom LPE tools to create privileged user accounts for persistence.
- Gamshen selectively alters responses for Googlebot requests using C&C servers brproxy.868id[.]com and gobr.868id[.]com to manipulate search rankings and promote gambling sites.
- Additional tools include Zunput (site enumerator and webshell dropper), Comdai (multipurpose C# library), and the benign GoToHTTP for remote access.
- Attribution: medium confidence that the actor is China-aligned based on hardcoded Chinese strings, a China-issued code-signing certificate, and other operational artifacts.
MITRE Techniques
- [T1588.002 ] Obtain Capabilities: Tool – GhostRedirector uses .NET Reactor to obfuscate its tools and leverages public exploits EfsPotato and BadPotato to develop privilege escalation tools. “GhostRedirector uses .NET Reactor to obfuscate its tools, and used EfsPotato and BadPotato to develop custom privilege escalation tools.”
- [T1587.001 ] Develop Capabilities: Malware – The actor develops custom malware such as Rungan and Gamshen. “GhostRedirector develops its own malware”
- [T1608.006 ] Stage Capabilities: SEO Poisoning – Gamshen is used to manipulate search results and drive traffic to third-party websites through SEO poisoning. “GhostRedirector uses SEO poisoning to manipulate search results and drive traffic to a third-party website.”
- [T1583.001 ] Acquire Infrastructure: Domains – The group registers and uses domains (e.g., 868id[.]com) to host payloads and C2. “GhostRedirector uses malicious domains for hosting payloads and for its C&C servers.”
- [T1583.004 ] Acquire Infrastructure: Server – The actor leverages Cloudflare-hosted infrastructure for staging and C2. “GhostRedirector leverages Cloudflare on its infrastructure.”
- [T1608.001 ] Stage Capabilities: Upload Malware – Rungan and Gamshen were staged on attacker-controlled servers for deployment. “GhostRedirector has staged Rungan and Gamshen on attacker-controlled servers.”
- [T1608.002 ] Stage Capabilities: Upload Tool – Various malicious and legitimate tools (e.g., GoToHTTP, privilege escalation binaries) were staged on attacker-controlled servers. “GhostRedirector has staged various malicious and legitimate tools on attacker-controlled servers.”
- [T1588.003 ] Obtain Capabilities: Code Signing Certificates – The actor used a code-signing certificate issued to a Chinese company to sign some tools. “GhostRedirector obtained a certificate for signing its tools, like those for privilege escalation.”
- [T1190 ] Exploit Public-Facing Application – Initial access is attributed to exploitation of a likely SQL injection vulnerability. “GhostRedirector exploits an unknown SQL injection vulnerability on the victim’s server.”
- [T1106 ] Native API – Rungan may register URLs by calling HTTP Server API functions such as HttpInitialize/HttpAddUrl to bypass IIS. “GhostRedirector may use APIs such as HttpInitialize and HttpAddUrl for registering a URL.”
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell is used to download payloads from staging servers. “GhostRedirector uses PowerShell interpreter to download malware.”
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – cmd.exe is used to execute commands that download and write payloads. “GhostRedirector can execute cmd.exe commands to download malware.”
- [T1559 ] Inter-Process Communication – Comdai uses named pipes (salamander_pipe) to communicate between components and trigger user creation. “Comdai can create a pipe to communicate and receive information from another process.”
- [T1546 ] Event Triggered Execution – Gamshen is loaded by the IIS worker process (w3wp.exe) when inbound HTTP requests trigger the server pipeline. “Gamshen is loaded by the IIS Worker Process (w3wp.exe) when the IIS server receives an inbound HTTP request.”
- [T1134 ] Access Token Manipulation – The actor manipulates tokens and performs LPE techniques (Pernicious Potatoes) for privilege escalation. “GhostRedirector can manipulate tokens to perform a local privilege escalation.”
- [T1112 ] Modify Registry – RID hijacking and registry modifications are used to elevate privileges for existing accounts. “GhostRedirector can modify a Windows registry key to perform RID hijacking.”
- [T1027 ] Obfuscated Files or Information – Tools are obfuscated using .NET Reactor to evade detection. “GhostRedirector obfuscates its local privilege escalation tools using .NET Reactor.”
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – Webshells are embedded in binaries (Zunput) and dropped on target sites. “GhostRedirector embedded webshells into its payloads like Zunput to be dropped on compromised server.”
- [T1140 ] Deobfuscate/Decode Files or Information – Rungan uses AES-CBC to decrypt embedded strings. “GhostRedirector uses AES in CBC mode to decrypt strings in the backdoor Rungan.”
- [T1083 ] File and Directory Discovery – Zunput enumerates IIS sites and directory contents to identify dynamic-content sites for webshell deployment. “GhostRedirector can use Zunput to list directory content on a victim’s server.”
- [T1105 ] Ingress Tool Transfer – The actor abuses certutil.exe or similar LOLBins to download additional tools. “GhostRedirector can abuse the tool certutil.exe to download malware.”
- [T1219 ] Remote Access Software – GoToHTTP is used to provide remote access to compromised servers via a browser. “GhostRedirector may use the GoToHTTP tool for connecting remotely to victims.”
- [T1071.001 ] Application Layer Protocol: Web Protocols – HTTP is used for backdoor communication (Rungan listens for HTTP requests). “GhostRedirector relies on HTTP to communicate with the backdoor Rungan.”
- [T1008 ] Fallback Channels – The actor creates admin users or deploys GoToHTTP to maintain alternative access if primary backdoors are removed. “GhostRedirector can deploy the tool GoToHTTP or create malicious users on the compromised server to maintain access.”
- [T1565 ] Data Manipulation – Gamshen modifies HTTP responses targeted at Googlebot to manipulate search results (SEO fraud). “GhostRedirector can modify the response of a compromised server intended for the Google crawler, in attempts to influence search results order.”
Indicators of Compromise
- [File hashes ] GhostRedirector binaries and tools – miniscreen.dll (Rungan) SHA-1: 28140A5A29EBA098BC6215DDAC8E56EACBB29B69, ManagedEngine64_v2.dll (Gamshen) SHA-1: 871A4DF66A8BAC3E640B2D1C0AFC075BB3761954
- [File names ] Deployed binaries and utilities – SitePut.exe (Zunput), link.exe (GoToHTTP), and auto_sign.exe (privilege escalation tool)
- [Domains ] Staging and C2 infrastructure – xzs.868id[.]com, brproxy.868id[.]com, gobr.868id[.]com (used to host payloads and provide Gamshen C2)
- [IP addresses ] Hosting/staging servers – 104.233.192[.]1 (xz.868id[.]com), 104.233.210[.]229 (q.822th[.]com / www.881vn[.]com), and 43.228.126[.]4 (www.cs01[.]shop) used for Comdai C2
- [Usernames ] Malicious accounts created – MysqlServiceEx, MysqlServiceEx2, Admin (used when creating administrator users on compromised servers)