Check Point Research uncovered a Silver Fox APT campaign abusing a previously unknown Microsoft-signed vulnerable driver (amsdk.sys WatchDog Antimalware v1.0.600) to terminate protected processes and disable endpoint protections, enabling deployment of the ValleyRAT backdoor. Attackers used dual-driver loaders, flipped a single byte in the patched driver’s unauthenticated timestamp to preserve signature while changing the hash, and hosted ValleyRAT infrastructure in China. #amsdk.sys #ValleyRAT
Keypoints
- Check Point Research attributed an ongoing in-the-wild campaign to Silver Fox APT that abuses a previously unknown vulnerable Microsoft-signed driver, WatchDog Antimalware (amsdk.sys v1.0.600), to terminate PP/PPL processes and bypass EDR/AV on Windows 10/11.
- Attackers used an all-in-one loader embedding two Zemana-based drivers (legacy ZAM.exe for older Windows and amsdk.sys for modern Windows), anti-analysis layers, and a ValleyRAT downloader to ensure cross-version compatibility and stealth.
- The vendor released a patched driver (wamsdk.sys v1.1.100) that fixed LPE via DACL/FILE_DEVICE_SECURE_OPEN but did not block arbitrary termination of protected processes; attackers rapidly adapted by modifying the patched binary’s unauthenticated timestamp byte to retain Microsoft signature while changing the file hash.
- The final payload across observed samples was ValleyRAT (aka Winos), a modular RAT with C2 infrastructure hosted in China and XOR-encrypted C2 communications; loaders inject the downloader into processes like svchost.exe for reflective in-memory execution.
- The exploited driver exposes IOCTLs enabling registration, obtaining full process handles, arbitrary process termination, and unrestricted raw disk read/write, facilitating EDR/AV disabling and potential LPE.
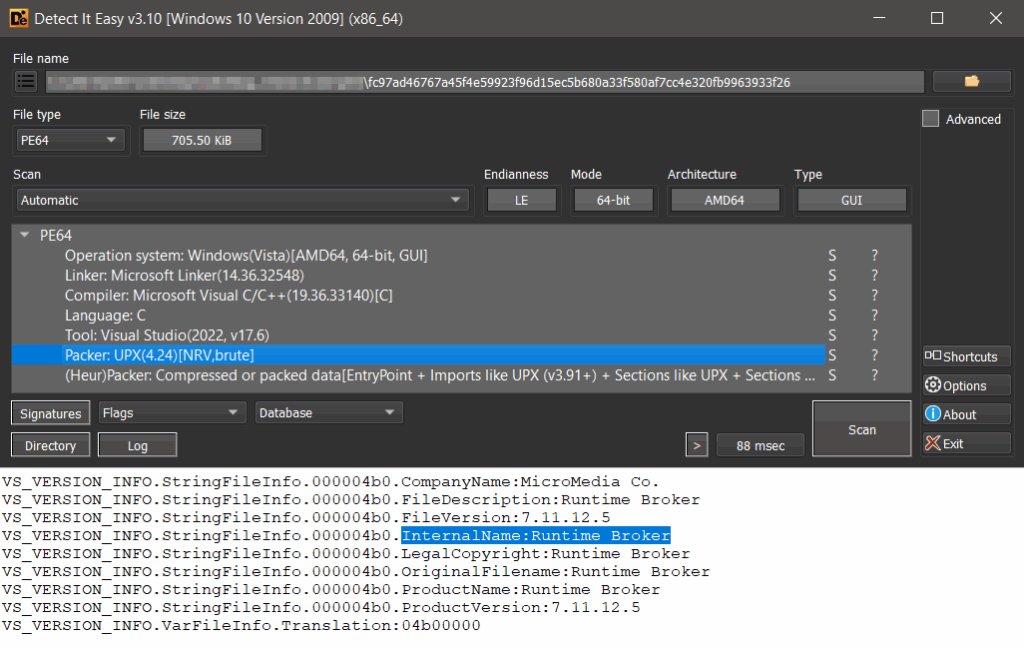
- Persistence is achieved by dropping RuntimeBroker.exe and Amsdk_Service.sys into C:Program FilesRunTime, creating services (Termaintor and Amsdk_Service) and loading the chosen driver via NtLoadDriver/registry entries.
- CPR published YARA rules, IOCs (sample hashes, driver hashes, and C2 IPs/ports), and recommended applying the Microsoft Vulnerable Driver Blocklist and behavior-based detections to mitigate BYOVD attacks.
MITRE Techniques
- [T1218 ] Signed Binary Proxy Execution – Abuse of a Microsoft-signed WatchDog/amsdk.sys driver to perform privileged actions and load kernel functionality that terminates protected processes, enabling trusted driver usage for malicious ends (“the driver, although … was signed by Microsoft … enabling it to be loaded even on fully updated Windows 10/11 systems”).
- [T1215 ] Kernel Modules and Extensions – Loading and communicating with a vulnerable kernel driver (amsdk.sys/wamsdk.sys/ZAM.exe) to invoke IOCTLs for process termination and raw disk I/O (“DeviceIoControl … 0x80002048 (IOCTL_TERMINATE_PROCESS) … arbitrary process termination”).
- [T1543 ] Create or Modify System Process – Creation of services (Termaintor and Amsdk_Service) and registry keys to persist the loader and install the vulnerable driver via NtLoadDriver/RegCreateKeyW/RegSetValueExW (“The service named Termaintor … The second created service, Amsdk_Service … registry key required to load the dropped vulnerable driver”).
- [T1055 ] Process Injection – Reflective in-memory loading of the ValleyRAT downloader DLL converted to shellcode and injection into running processes (typically svchost.exe) (“64-bit, UPX-packed DLL that is converted into shellcode … injected into an already running process, typically an instance of svchost.exe”).
- [T1105 ] Ingress Tool Transfer – Downloading the final ValleyRAT payload from C2 servers defined in embedded configuration after XOR decryption (“The C2 servers are defined in the embedded configuration … communication … encrypted using a simple XOR cipher … the downloaded content includes the final payload: the ValleyRAT backdoor”).
- [T1497 ] Virtualization/Sandbox Evasion – Anti-VM, anti-sandbox, hypervisor detection, IP-based environment checks and window title checks to delay or abort execution when analysis tools or specific environments are detected (“Anti-VM … Anti-Sandbox … hypervisor detection … uses ip-api.com/json to check ISP/ORG and aborts if matched; ValleyRAT EnumWindows checks window titles associated with analysis tools”).
- [T1204 ] User Execution – Distribution via .rar archives containing executables or DLLs that are side-loaded by legitimate applications to initiate infection (“the malware is delivered via .rar archives containing either a single executable (.exe) or a dynamic-link library (.dll) that is side-loaded through a legitimate application”).
Indicators of Compromise
- [File Hash ] All-in-one loader samples delivering ValleyRAT – example SHA-256: 24fffc34e45c168ea4498f51a7d9f7f074d469c8d4317e8e2205c33a99b5364, fc97ad46767a45f4e59923f96d15ec5b680a33f580af7cc4e320fb9963933f26 (and multiple other hashes listed in Appendix B).
- [File Hash ] ValleyRAT final-stage/backdoor examples – 09587073acbfec909eea69aa49774b3fdaa681db9cec7cb20a4143050897c393, 2f0e34860194ccd232f7c8c27fefe44c96b63468e8581f93c38767725255f945 (and other ValleyRAT hashes listed).
- [Driver Hash ] Vulnerable driver hashes (Zemana-derived) – amsdk.sys (WatchDog) hash example: 12b3d8bc5cc1ea6e2acd741d8a80f56cf2a0a7ebfa0998e3f0743fcf83fabb9e, patched wamsdk.sys hash example: 0be8483c2ea42f1ce4c90e84ac474a4e7017bc6d682e06f96dc1e31922a07b10 (and one more driver hash listed).
- [IP Address ] C2 servers hosting ValleyRAT – 156[.]234[.]58[.]194:52110,52111 (Yancy Limited, HK), 47[.]239[.]197[.]97:52116,52117 (Alibaba Cloud, HK), 8[.]217[.]38[.]238:8888 (Alibaba Cloud, HK), and others listed (156[.]241[.]144[.]66:52139,52160; 1[.]13[.]249[.]217:9527,9528).
- [File Name ] Dropped persistence/file names – RuntimeBroker.exe (loader) and Amsdk_Service.sys (driver) located in C:Program FilesRunTime; service names Termaintor and Amsdk_Service used for persistence.
- [Process Names ] Targeted security processes to be terminated – examples: MsMpEng.exe, MpCmdRun.exe, 360Safe.exe, QQPCRTP.exe (and 188+ other process names targeting China/Asia security products listed in Appendix A).
Read more: https://research.checkpoint.com/2025/silver-fox-apt-vulnerable-drivers