A new HTTP request smuggling technique exploits parsing discrepancies between front-end proxies and back-end servers, bypassing security controls. Implementing patches and migrating to HTTP/2 significantly enhances protection against this type of attack. #HTTPRequestSmuggling #HTTP2Migration
Keypoints
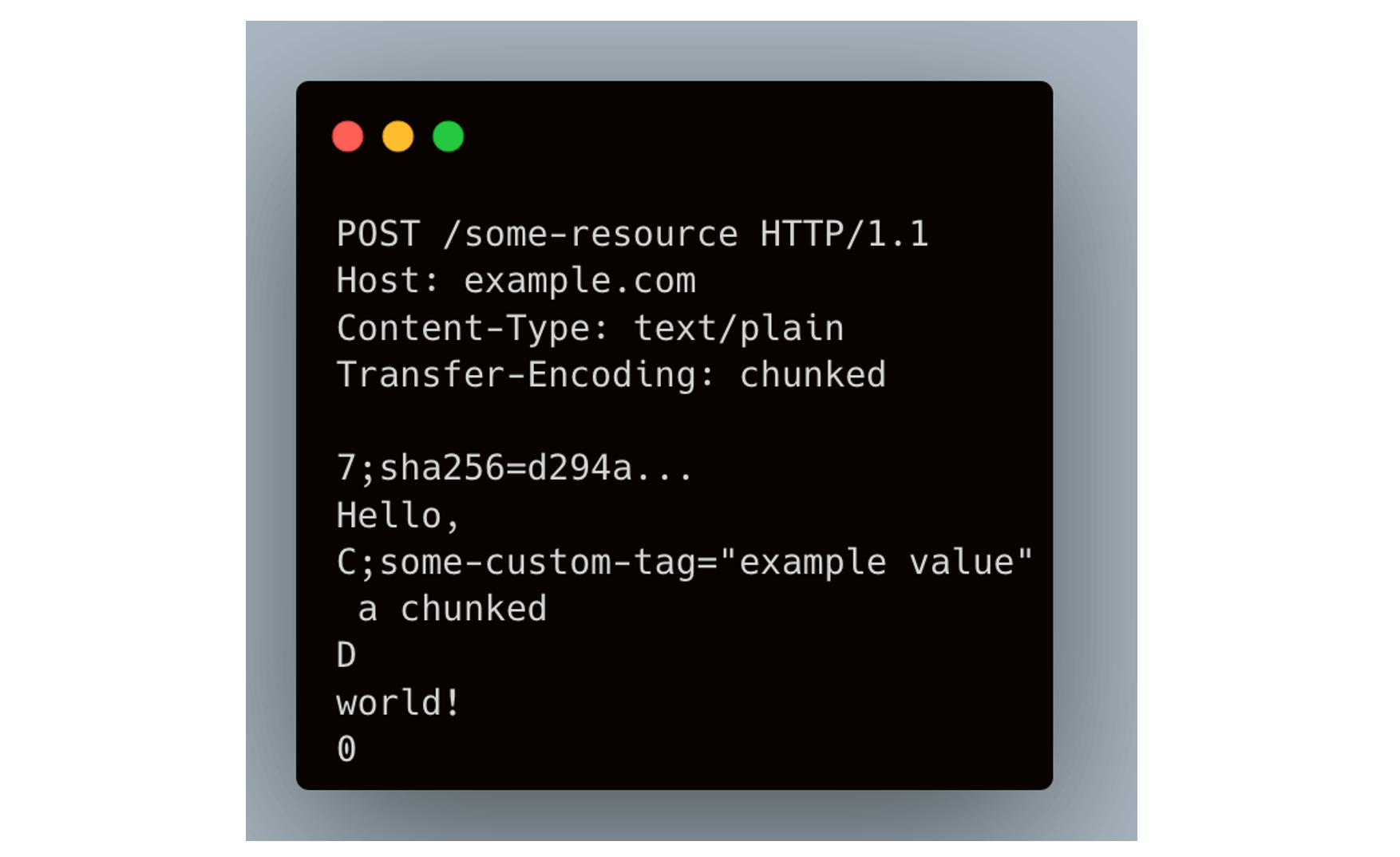
- The attack leverages inconsistent parsing behaviors caused by malformed chunk extensions in HTTP/1.1.
- Front-end and back-end systems interpret request boundaries differently, enabling request smuggling.
- Applying security patches across systems mitigates current vulnerabilities effectively.
- Moving from HTTP/1.1 to HTTP/2 provides a more secure, binary-framed protocol that prevents such exploits.
- Organizations should prioritize protocol upgrades and rigorous validation to defend against emerging threats.
Read More: https://www.imperva.com/blog/smuggling-requests-with-chunked-extensions-a-new-http-desync-trick/