Seqrite Lab uncovered “Operation HanKook Phantom,” a spear-phishing campaign by APT37 using legitimate-looking PDF decoys and malicious LNK files that execute multi-stage, fileless PowerShell loaders to deploy ROKRAT and exfiltrate data via cloud services and a hardcoded HTTP C2. The campaign targets South Korean government, academic, and research organizations and employs XOR-encrypted payloads, in-memory execution, and cloud-based C2 channels like Dropbox, pCloud, and Yandex; #APT-37 #ROKRAT
Keypoints
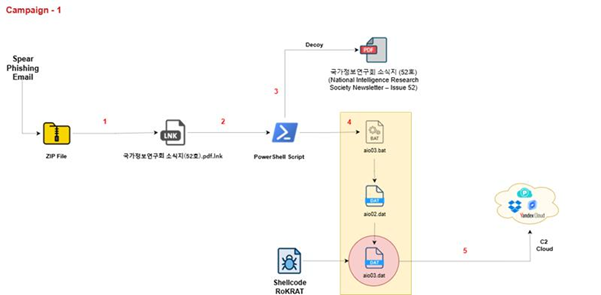
- Attackers used legitimate-looking decoy documents (e.g., “국가정보연구회 소식지 (52호)”) bundled with malicious .LNK files to initiate infections via embedded PowerShell loaders.
- Execution chain extracts multiple embedded payloads from specific binary offsets inside .LNK files, drops stage files to %TEMP% (e.g., aio01.dat, aio02.dat, aio03.bat), and performs fileless in-memory execution.
- Final payloads exhibit ROKRAT functionality: host fingerprinting, anti-VM checks, screenshot capture, extensive command set (file exfiltration, remote command execution, downloading and executing additional PEs), and cloud-based C2 usage.
- Campaign uses XOR single-byte decryption (keys ‘5’ and ‘7’), reflective DLL injection and Windows API memory allocation (GlobalAlloc, VirtualProtect, CreateThread) to execute payloads without writing them as persistent disk files.
- Data exfiltration is covert: staged files are uploaded via HTTP POST disguised as PDF uploads to hxxp://daily.alltop.asia/blog/article/up2.php and downloadable payloads are retrieved from /d2.php and cleaned via /del2.php.
- Targets are primarily South Korean institutions and individuals (intelligence associations, universities, government ministries), with broader regional targeting including Japan, Vietnam, and parts of Asia and the Middle East.
- Seqrite detects the campaign as Trojan.49901.GC and trojan.49897.GC and maps multiple ATT&CK techniques used across initial access, execution, persistence, evasion, discovery, collection, C2, and exfiltration.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – LNK files disguised as legitimate PDFs are sent to targets to trigger payload execution (“LNK file named 국가정보연구회 소식지(52호).pdf.lnk” used as delivery).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Embedded PowerShell scripts inside LNKs decode and execute payloads in memory (“PowerShell reads and decodes a UTF-8 encoded script from aio02.dat and runs it in memory using Invoke-Command”).
- [T1204.001 ] User Execution: Malicious Link – Execution requires user opening the .LNK which launches the embedded script (“Once the LNK file is executed, it triggers a payload download or command execution”).
- [T1204.002 ] User Execution: Malicious File – Decoy documents dropped and opened by users are used to mask malicious activity (“extracts a decoy PDF and three embedded payloads … saved in %TEMP%”).
- [T1574.001 ] Hijack Execution Flow: DLL – Malware uses DLL injection techniques to persist or run code (“Persistence: Hijack Execution Flow: DLL” listed in mapping and dynamic-link library injection observed).
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Malware demonstrates autostart behaviors consistent with registry or startup persistence (mapped in report’s persistence techniques).
- [T1055.001 ] Process Injection: Dynamic-link Library Injection – ROKRAT performs DLL-based injection to execute retrieved shellcode (“The shellcode is retrieved from the C2 server and executed via CreateThread”).
- [T1055.009 ] Process Injection: Proc Memory – In-memory execution with reflective injection and API calls is used to run payloads without disk (“uses GlobalAlloc, VirtualProtect, CreateThread … inject the decoded binary, and execute it”).
- [T1053.005 ] Scheduled Task/Job : Scheduled Task – Use of scheduled tasks/jobs is included in the actor’s privilege escalation/persistence mapping (listed among observed techniques).
- [T1140 ] Deobfuscate/Decode Files or Information – Scripts decode Base64 and XOR-encrypted payloads before execution (“tony32.dat contains Base64-encoded PowerShell payload … XOR-encrypted binary tony31.dat decrypted in memory”).
- [T1070.004 ] Indicator Removal: File Deletion – Malware and loaders delete staging files and LNKs to evade detection (“the LNK file deletes itself … deletes abs.tmp after execution”).
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – Multiple payloads are embedded at offsets within LNK files and extracted at runtime (“reads embedded payload data from them, extracts multiple file contents … Offset 0x0007EDC1: payload #1 (dat)”).
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – Payloads use single-byte XOR and Base64 double-decoding to obfuscate binaries (“XOR-encrypted with key 0x35 … Base64 encoded string in tony32.dat decoded twice”).
- [T1056.002 ] Input Capture: Keylogging: GUI Input Capture – Keylogging and GUI input capture capabilities are mapped in credential access techniques for the malware.
- [T1087.001 ] Account Discovery: Local Account – Malware gathers local account information as part of discovery (“System information discovery, account discovery listed in techniques”).
- [T1217 ] Browser Extensions Discovery – Browser information discovery routines are used to collect browser-related data (“Browser Information Discovery” listed among discovery techniques).
- [T1083 ] File and Directory Discovery – Malware scans Temp directories and enumerates files for collection (“scans a specific Temp directory … identifying all non-directory files”).
- [T1082 ] System Information Discovery – Host fingerprinting collects system and BIOS/manufacturer information (“building a host fingerprint string set, containing … BIOS / Manufacturer info”).
- [T1123 ] Audio Capture – Audio capture capability is included in the collection mapping (audio capture listed among collection techniques).
- [T1005 ] Data from Local System – Files from the local system are collected for exfiltration (“searches for files … located files are then uploaded to the C&C server”).
- [T1113 ] Screen Capture – Screenshot capture function observed in malware (“function sub_40E40B appears to capture a screenshot, process the image in memory”).
- [T1102.002 ] Web Service: Bidirectional Communication – Cloud services (Dropbox, pCloud, Yandex) are used as C2 channels for uploading/downloading commands and payloads (listed provider API endpoints and obfuscated URLs).
- [T1041 ] Exfiltration Over C2 Channel – Data is exfiltrated via HTTP POST and cloud APIs to attacker-controlled endpoints (“files uploaded … to hxxp://daily.alltop.asia/blog/article/up2.php” and cloud provider upload APIs).
- [T1529 ] System Shutdown/Reboot – Impact technique included in mapping, indicating capability to reboot or shut down systems remotely.
Indicators of Compromise
- [MD5 ] malware sample hashes – aio02.dat (1aec7b1227060a987d5cb6f17782e76e), aio01.dat (d035135e190fb6121faa7630e4a45eed)
- [MD5 ] batch/loader files – aio03.bat (591b2aaf1732c8a656b5c602875cbdd9), tony33.bat (051517b5b685116c2f4f1e6b535eb4cb)
- [MD5 ] staged dat files – tony31.dat (2dc20d55d248e8a99afbe5edaae5d2fc), tony32.dat (f34fa3d0329642615c17061e252c6afe)
- [MD5 ] LNK and archive samples – *.LNK (da05d6ab72290ca064916324cbc86bab), *.Zip (cc1522fb2121cf4ae57278921a5965da)
- [File name ] decoy LNK examples – 북한이탈주민의 성공적인 남한정착을 위한 아카데미 운영.lnk (443a00feeb3beaea02b2fbcd4302a3c9), 국가정보와 방첩 원고.lnk (f6d72abf9ca654a20bbaf23ea1c10a55)
- [Domain/URL ] C2 and exfiltration endpoints – hxxp://daily.alltop.asia/blog/article/up2.php (exfiltration), hxxp://daily.alltop.asia/blog/article/d2.php and /del2.php (payload download and cleanup)
Read more: https://www.seqrite.com/blog/operation-hankook-phantom-north-korean-apt37-targeting-south-korea/