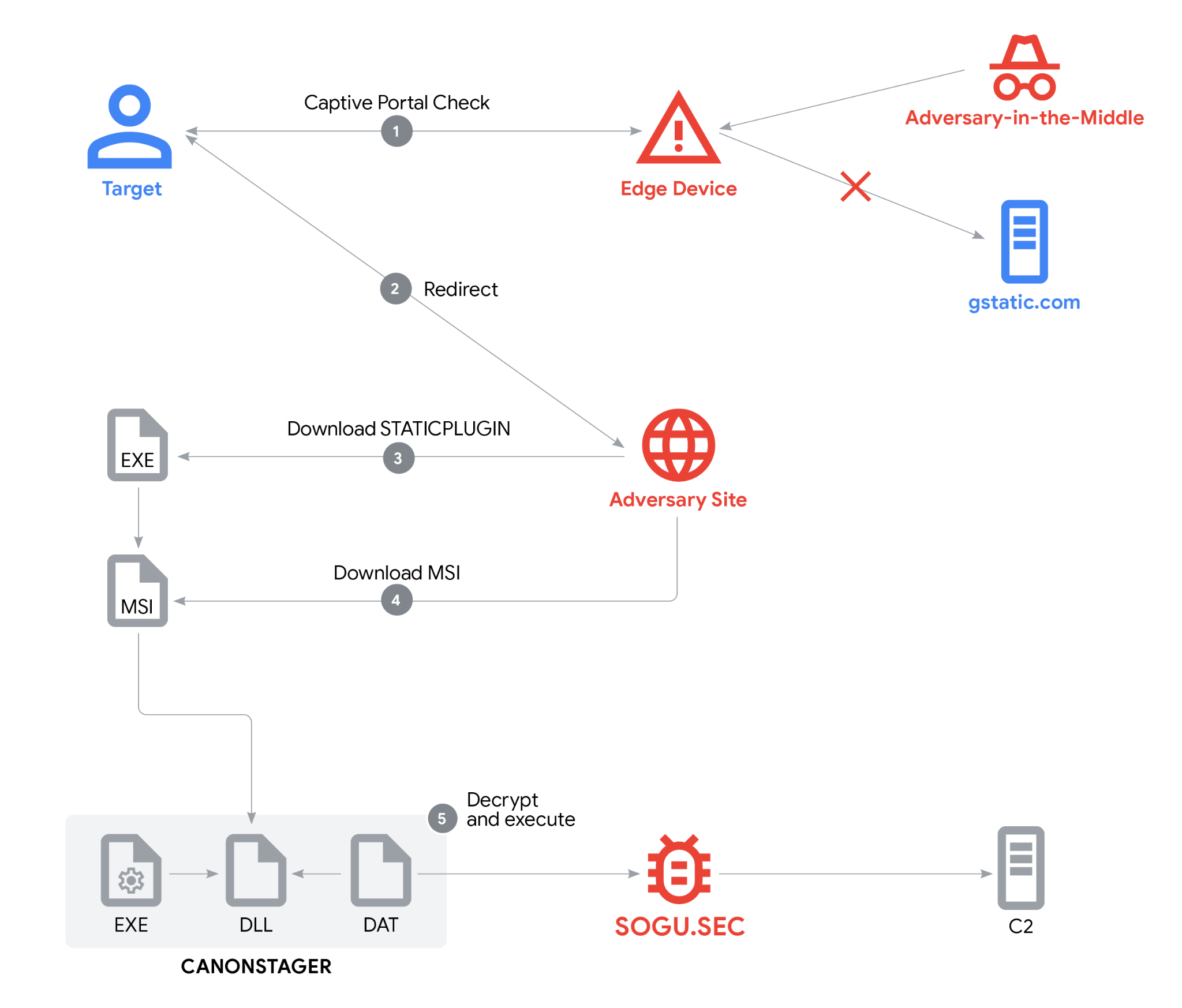
Google Threat Intelligence Group (GTIG) discovered a multifaceted espionage campaign by PRC-nexus actor UNC6384 that hijacked captive-portal browser redirects to deliver a digitally signed downloader (STATICPLUGIN) which ultimately side-loaded CANONSTAGER to deploy the in-memory SOGU.SEC backdoor. The campaign targeted diplomats in Southeast Asia and used valid TLS and code-signing certificates, AitM on edge devices, and layered social engineering to evade detection. #UNC6384 #STATICPLUGIN #CANONSTAGER #SOGU.SEC
Keypoints
- GTIG attributes a March 2025 espionage campaign to PRC-nexus actor UNC6384 targeting diplomats in Southeast Asia and other global entities.
- Attack chain begins with a captive-portal/AitM redirect from a legitimate gstatic URL to a malicious landing page that triggers a download disguised as an Adobe plugin update.
- First-stage downloader STATICPLUGIN is digitally signed (Chengdu Nuoxin Times Technology Co., Ltd.) and retrieves an MSI (“20250509.bmp”) that contains files including CANONSTAGER and an RC4-encrypted SOGU.SEC payload.
- CANONSTAGER uses unconventional techniques (API hashing, Thread Local Storage, control-flow obfuscation, window procedures and message queues) to decrypt and execute SOGU.SEC in-memory via EnumSystemGeoID callback.
- SOGU.SEC (PlugX variant) provides typical backdoor capabilities (system info collection, file upload/download, remote shell) and communicated with C2 at 166.88.2[.]90 using HTTPS.
- Threat actors leveraged valid TLS (Let’s Encrypt for mediareleaseupdates[.]com) and valid code signing to increase social engineering credibility and bypass defenses; numerous signed samples by the same Subscriber were tracked by GTIG.
- GTIG notified impacted Gmail/Workspace users, added IOCs to Safe Browsing, and recommended Enhanced Safe Browsing, device updates, and 2-Step Verification while sharing YARA rules and IOCs for defender hunting.
MITRE Techniques
- [T1078 ] Valid Accounts – Use of valid code signing and TLS certificates to appear legitimate and bypass defenses: “the malware payload is disguised as legitimate software and is digitally signed with a certificate issued by a Certificate Authority.”
- [T1204.002 ] User Execution: Malicious File – Social engineering via fake plugin/update landing page that prompts user to download and run AdobePlugins.exe: “Install Missing Plugins…” and window button triggers download of AdobePlugins.exe.
- [T1557.001 ] Adversary-in-the-Middle: Network Device Compromise – AitM redirect from gstatic captive portal to actor-controlled site, likely via compromised edge devices: “redirect chains from this domain leading to the threat actor’s landing webpage…indicating an AitM attack.”
- [T1105 ] Ingress Tool Transfer – Downloader retrieves an MSI package (20250509.bmp) and additional components from mediareleaseupdates[.]com: “STATICPLUGIN then retrieves an MSI package from the same website.”
- [T1036.005 ] Masquerading: Masquerade as Legitimate Software – STATICPLUGIN and landing page mimic legitimate Adobe/VC++ installer and plugin updates: “masquerade as a legitimate Microsoft Visual C++ 2013 Redistributables installer.”
- [T1574.001 ] DLL Search Order Hijacking/Side-loading – CANONSTAGER is deployed via DLL side-loading to execute the backdoor: “CANONSTAGER is DLL side-loaded and deploys the SOGU.SEC backdoor.”
- [T1055.001 ] Process Injection: Dynamic-link Library Injection – CANONSTAGER decrypts and executes SOGU.SEC in-memory, avoiding file-based detection: “Executes SOGU.SEC in-memory with an EnumSystemGeoID callback.”
- [T1027.002 ] Obfuscated Files or Information: Software Packing – Use of custom API hashing, TLS storage and control flow obfuscation to hide function calls and control flow: “API Hashing and Thread Local Storage…The API hashing hides which Windows APIs are being used.”
- [T1190 ] Exploit Public-Facing Application – Abuse of captive portal/browser behavior (hardcoded generate_204 request) and redirect behavior to deliver payload through web-facing mechanisms: “The Chrome browser performs an HTTP request to a hardcoded URL…to enable this redirect mechanism.”
Indicators of Compromise
- [File Hash ] Malware and payload hashes – AdobePlugins.exe: 65c42a7ea18162a92ee982eded91653a5358a7129c7672715ce8ddb6027ec124; 20250509.bmp (MSI): 3299866538aff40ca85276f87dd0cefe4eafe167bd64732d67b06af4f3349916.
- [File Hash ] Additional payloads – cnmpaui.dll (CANONSTAGER): e787f64af048b9cb8a153a0759555785c8fd3ee1e8efbca312a29f2acb1e4011; cnmplog.dat (RC4 encrypted SOGU.SEC): cc4db3d8049043fa62326d0b3341960f9a0cf9b54c2fbbdffdbd8761d99add79.
- [Domain ] Hosting and landing pages – mediareleaseupdates[.]com used for landing page, script and downloads – https[:]//mediareleaseupdates[.]com/AdobePlugins.html, https[:]//mediareleaseupdates[.]com/style3.js, https[:]//mediareleaseupdates[.]com/AdobePlugins.exe.
- [Network IP ] Infrastructure – Hosting IP: 103.79.120[.]72 (hosting actor-controlled site); C2 IP: 166.88.2[.]90 (SOGU.SEC communication over HTTPS).
- [Certificate ] TLS / Code-signing fingerprints – mediareleaseupdates[.]com SHA-1: c8744b10180ed59bf96cf79d7559249e9dcf0f90; AdobePlugins.exe signing SHA-1: eca96bd74fb6b22848751e254b6dc9b8e2721f96.
- [Host Artifact ] Local indicators and artifacts – Mutex: KNbgxngdS; RC4 key: mqHKVbHWWAJwrLXD; Persistence registry example: HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunCanonPrinter=”%APPDATA%cnmpaui.exe”.
Read more: https://cloud.google.com/blog/topics/threat-intelligence/prc-nexus-espionage-targets-diplomats/