CIS CTI’s “Top 10 Malware Q2 2025” report lists the quarter’s top malware families and 62 associated IoCs (53 domains, 9 IPs) and expands that set to 62 IPs and thousands of related artifacts through WHOIS/DNS and threat-intel queries. Analysis found 72,921 unique client IPs querying IoC domains, multiple IoCs appearing on threat feeds before reporting, and additional weaponized IPs tied to the IoCs. #SocGholish #AgentTesla
Keypoints
- CIS CTI identified the top 10 malware for Q2 2025 and documented 62 IoCs: 53 domains and 9 IP addresses.
- The nine malware with IoCs include SocGholish, ZPH, AgentTesla, VenomRAT, CoinMiner, NanoCore, Arechclient, ClearFake, and LandUpdate; Mirai had no domain/IP IoCs.
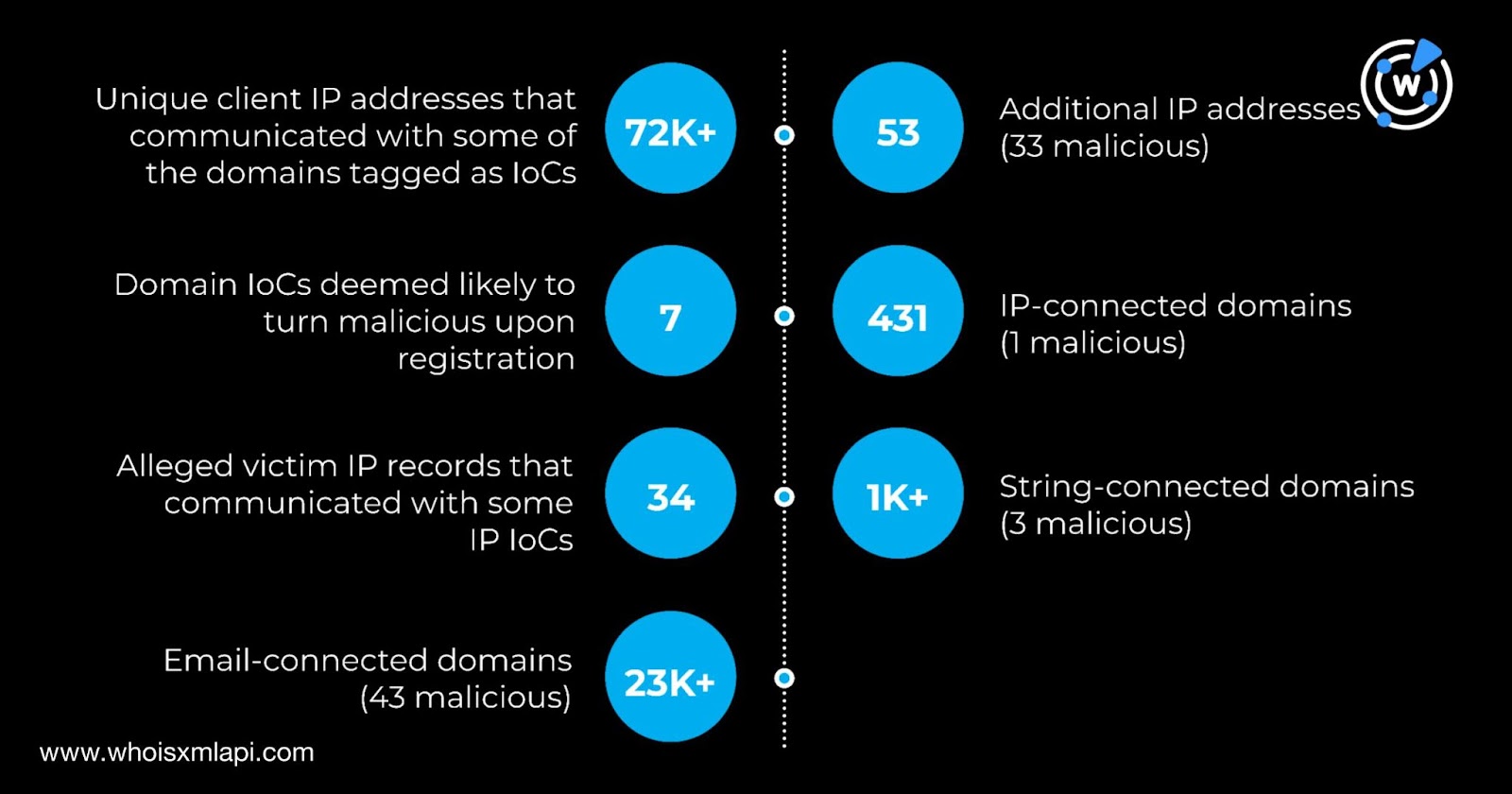
- WHOIS/DNS and DNS traffic analysis revealed 72,921 unique client IPs querying the 53 domain IoCs across 1,048,540 DNS requests in a sampled period.
- Seven domain IoCs appeared on First Watch malicious feeds 31–233 days prior to being reported as attack IoCs, indicating early feed detections.
- Hunting expanded artifacts to 25,633 web properties and discovered 53 additional IPs resolving from the 53 domain IoCs; 33 of those additional IPs were flagged as weaponized.
- Combining original and additional IPs (62 total) showed 18 possibly dedicated hosts which resolved to 431 IP-connected domains after filtering.
- Geolocation and ISP analysis showed overlaps between IoC origins and additional IPs (notably India, Russia, the U.S., and DigitalOcean as an ISP/administrator).
MITRE Techniques
- [T1204] User Execution – Social engineering via fake browser updates used to deliver downloaders (e.g., “Downloader disguised as fake browser updates”).
- [T1190] Exploit Public-Facing Application – Distribution of malware through malicious domains and weaponized IPs serving malicious payloads (“53 domains and nine IP addresses” used as IoCs).
- [T1071] Application Layer Protocol – Malware communication and C2 activity observed on malicious IPs labeled as C&C (“216[.]144[.]210[.]189 C&C”).
- [T1566] Phishing – Use of malicious spam to distribute RATs and loaders (e.g., “RAT distributed via malicious spam”, “Cryptocurrency miner … distributed via malicious spam”).
- [T1105] Ingress Tool Transfer – Dropping of secondary payloads such as coin miners by other malware (“Cryptocurrency miner either dropped by other malware or distributed via malicious spam”).
- [T1588] Obtain Capabilities – Threat intelligence shows domains appearing on feeds prior to reporting, indicating adversary infrastructure registration and capability acquisition (“seven appeared on First Watch Malicious Domains Data Feed upon registration”).
Indicators of Compromise
- [Domain ] IoC domains tied to malware – emeraldpinesolutions[.]com (SocGholish), sixfiguredigital[.]group (AgentTesla), and candyxpdf[.]com (Arechclient).
- [IP ] IoC and additional weaponized IPs – examples include 104[.]18[.]21[.]135 (generic threat) and 216[.]144[.]210[.]189 (C&C); and 33 more additional IPs flagged as weaponized.
- [Counts ] aggregate IoC counts and context – 53 domain IoCs and 9 IP IoCs originally identified; hunting expanded to 53 additional IPs and 25,633 web properties.
- [ASN/Client IP ] DNS traffic context – 72,921 unique client IPs tied to 2,720 unique ASNs querying IoC domains during sampled DNS traffic.
- [Feed dates ] First Watch detections prior to report – emeraldpinesolutions[.]com added 17 June 2025 (31 days prior), sixfiguredigital[.]group added 27 Nov 2024 (233 days prior), candyxpdf[.]com added 26 Feb 2025 (142 days prior).
Read more: https://circleid.com/posts/top-10-malware-of-q2-2025-a-deep-dive-into-the-iocs