ANY.RUN analysts tracked August campaigns including a 7-stage Tycoon2FA phishing chain, Rhadamanthys delivered via ClickFix with PNG steganography, and a new Salty2FA PhaaS linked to Storm-1575, exposing execution chains, decrypted traffic, and behaviors missed by static tools. The investigations produced IOCs and behavioral indicators SOC teams can use to build detection rules and reduce investigation time. #Tycoon2FA #Rhadamanthys #Salty2FA #Storm-1575
Keypoints
- ANY.RUN analysts uncovered a multi-stage Tycoon2FA phishing campaign that uses seven sequential checks (voicemail-themed email, PDF redirect, Cloudflare Turnstile CAPTCHA, “press & hold”, email validation) to defeat automated defenses and target high-value accounts.
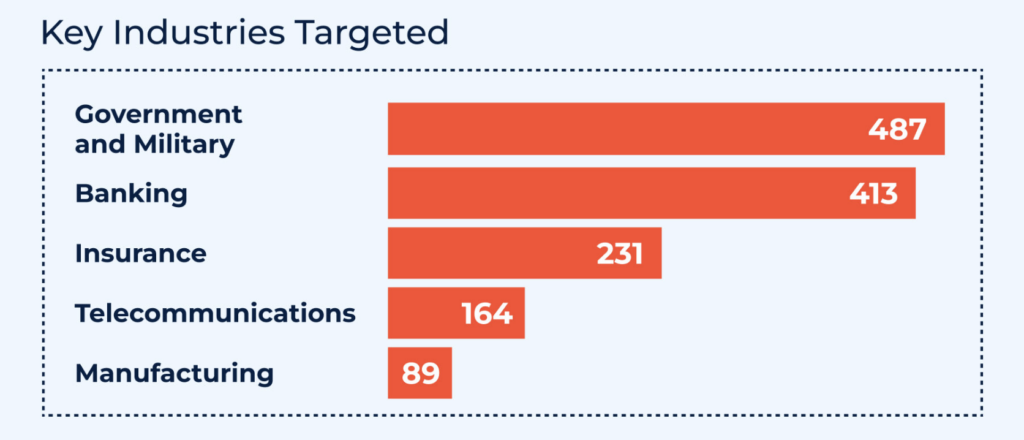
- Tycoon2FA activity focused on government, military, and financial sectors across the US, UK, Canada, and Europe, with 26% of analyzed cases involving the banking sector.
- Rhadamanthys stealer was delivered via ClickFix social-engineering flows, using MSI execution in memory, anti-VM checks, TLS connections to IPs with self-signed mismatched certificates, and PNG steganography to hide additional payloads.
- Salty2FA, a newly observed Phishing-as-a-Service framework linked to Storm-1575, employs source-code “salting,” compound subdomain patterns, chained servers, and adversary-in-the-middle interception of 2FA (push, OTP, SMS, calls) to bypass authentication protections.
- Analyses inside ANY.RUN’s Interactive Sandbox revealed full execution chains, decrypted traffic, and behavioral indicators that static tools missed, enabling SOC teams to convert findings into detection rules and SOAR playbooks.
- IOCs collected across the cases include multiple domains, IP addresses, and obfuscated URLs useful for tracking campaigns via Threat Intelligence Lookup and enriching SIEM/XDR detection logic.
- Stopping these threats requires behavioral visibility (to detect ClickFix flows, steganography, and chained interactions) combined with live TI and sandbox-driven replication of user actions to reduce MTTR.
MITRE Techniques
- [T1566] Phishing – Tycoon2FA and Salty2FA begin with phishing emails/links: “Phishing email link → The attack begins with a voicemail-themed phishing email containing a malicious link to lure the victim.”
- [T1113] Drive-by Compromise (via embedded link in PDF) – Tycoon2FA uses a fake PDF containing an embedded hyperlink that redirects the victim deeper into the chain: “PDF attachment → Clicking the link triggers a fake PDF download, masking the next redirection step.”
- [T1530] Use of Web Services (Cloudflare Turnstile) – Tycoon2FA uses Cloudflare Turnstile CAPTCHA to filter automated scanners: “Cloudflare Turnstile CAPTCHA → A CAPTCHA challenge filters out automated scanners by requiring human interaction.”
- [T1583] Acquire Infrastructure – Salty2FA infrastructure uses recurring compound subdomain patterns and .ru domains to support chained servers: “Infrastructure relies on a recurring pattern: compound .??.com subdomains paired with .ru domains (T1583), supported by chained servers and resilient C2 communication (T1071.001).”
- [T1071.001] Application Layer Protocol: Web Protocols – Salty2FA and Rhadamanthys use web protocols and chained servers for C2: “chained servers and resilient C2 communication (T1071.001).”
- [T1557] Adversary-in-the-Middle – Salty2FA implements MITM to intercept push notifications, OTPs, SMS, and calls: “Salty2FA also implements adversary-in-the-middle techniques (T1557), enabling it to intercept phone app push notifications, OTP codes, SMS messages, and even two-way voice calls.”
- [T1218.007] Signed Binary Proxy Execution: Msiexec – Rhadamanthys chain executes an MSI silently in memory using msiexec: “ClickFix ➡️ msiexec ➡️ EXE file ➡️ compromised system file ➡️ PNG-stego payload” and “The MSI is executed silently in memory (T1218.007).”
- [T1497.001] Virtualization/Sandbox Evasion: System Checks – Rhadamanthys performs anti-VM checks to evade analysis: “Anti-VM checks (T1497.001) are performed to evade analysis.”
- [T1027.003] Obfuscated Files or Information: Steganography – Rhadamanthys delivery uses PNG steganography to hide additional payloads: “Additional payloads are delivered via an obfuscated PNG using steganography (T1027.003).”
Indicators of Compromise
- [Domain ] Tycoon2FA phishing infrastructure – filecloudonline[.]com, vnositel-bg[.]com
- [Domain ] Additional Tycoon2FA domains – culturabva[.]es, spaijo[.]es (and 2 more domains)
- [IP Address ] Rhadamanthys/ClickFix C2 or infrastructure – 84.200[.]80.8, 179.43[.]141.35
- [Domain ] Rhadamanthys/ClickFix campaign domains – flaxergaurds[.]com, temopix[.]com (and zerontwoposh[.]live)
- [Domain ] Salty2FA domains and hosts – innovationsteams[.]com, marketplace24ei[.]ru
- [URL ] Salty2FA phishing paths – hxxps[://]telephony[.]nexttradeitaly[.]com/SSSuWBTmYwu/, hxxps[://]parochially[.]frankfurtwebs[.]com[.]de/ps6VzZb/
- [IP Address ] Salty2FA infrastructure – 153[.]127[.]234[.]4, 51[.]89[.]33[.]171 (and 191[.]96[.]207[.]129, 153[.]127[.]234[.]5)
- [Email ] Affiliate/contact for Salty2FA investigation – izumi [at] yurikamome[.]com
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/cyber-attacks-august-2025/