This content explains how security teams can design and implement secure, compliant malware analysis environments within AWS. It highlights the architectural best practices, policies, and monitoring strategies needed to contain malicious code safely in the cloud. #AWSMalwareAnalysis #IsolatedSandbox
Keypoints
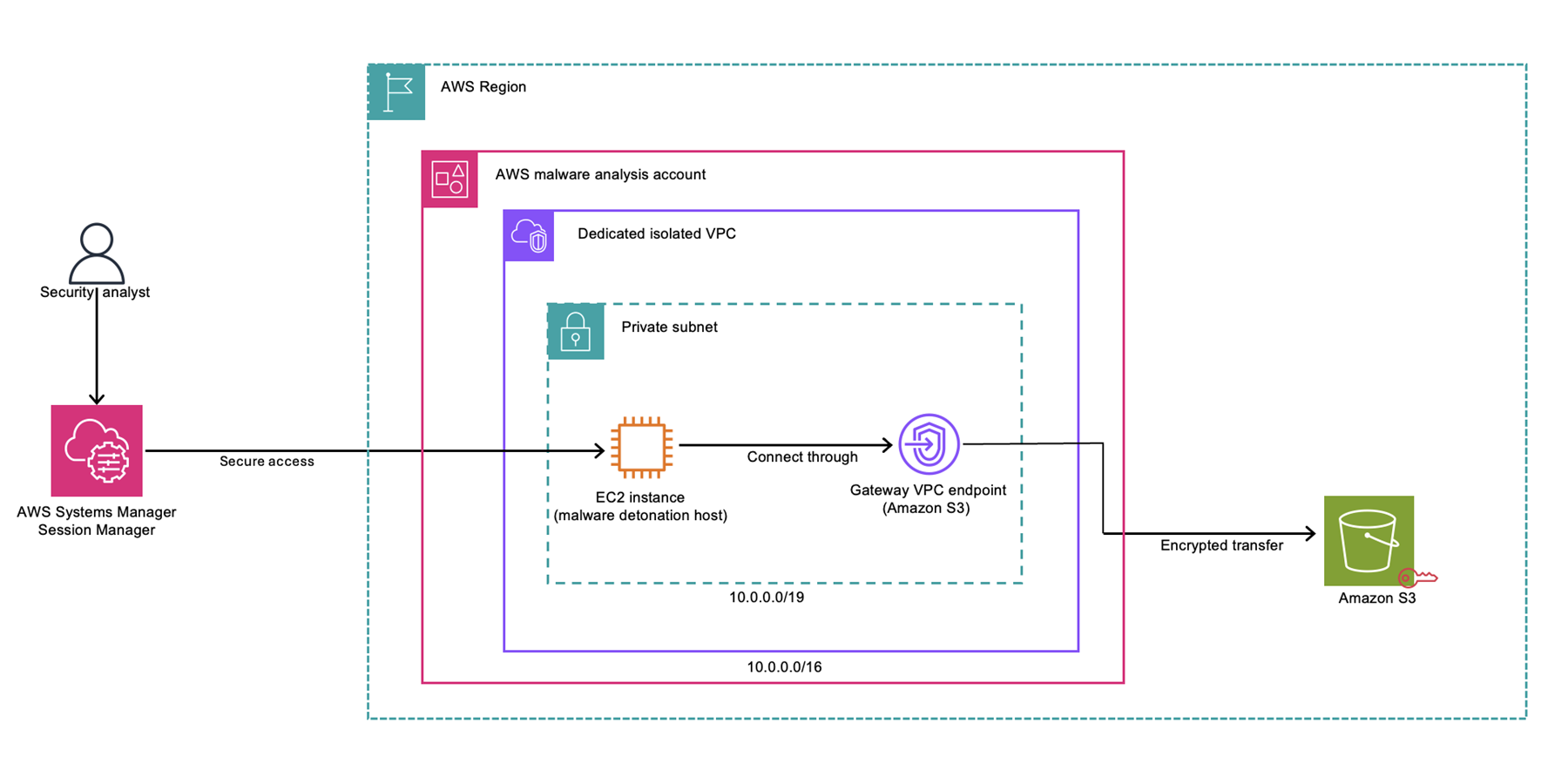
- Malware analysis in AWS requires dedicated, isolated VPCs with no public access or internet connectivity.
- IAM policies and permission boundaries are critical for enforcing least privilege and preventing privilege escalation.
- Mounting security measures include hardened AMIs, encrypted storage, and strict egress controls.
- Continuous monitoring with services like GuardDuty, CloudTrail, and Config helps detect and prevent malicious activity.
- Implementing AWS Organizations with SCPs enhances security boundaries and policy enforcement for malware sandbox accounts.
Read More: https://aws.amazon.com/blogs/security/malware-analysis-on-aws-setting-up-a-secure-environment/