Proofpoint linked RomCom to TA829 and TransferLoader to UNK_GreenSec but noted campaign similarities; WhoisXML API expanded the analysis of 109 IoC domains, uncovering typosquatting groups and numerous connected artifacts. The investigation found four TransferLoader domain IoCs in five typosquatting groups, multiple shared infrastructure signals (registrars, NS providers, IPs), and thousands of connected domains and IPs with dozens marked malicious. #RomCom #TransferLoader
Keypoints
- Proofpoint attributed RomCom mainly to TA829 and TransferLoader to UNK_GreenSec but observed operational similarities between their campaigns.
- WhoisXML API analyzed 109 IoC domains (20 RomCom, 89 TransferLoader) and searched for typosquatting and connected infrastructure artifacts.
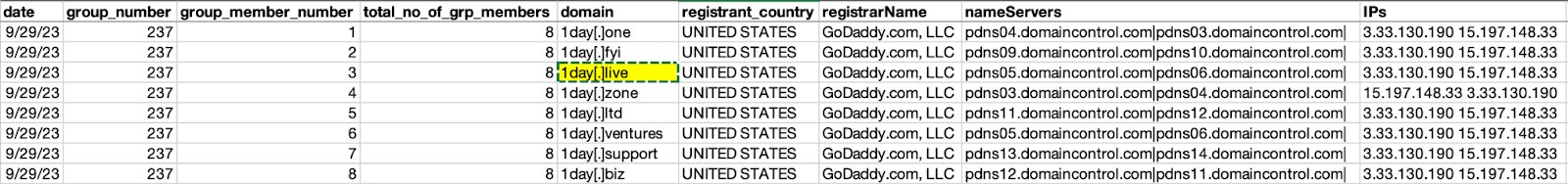
- Four TransferLoader domain IoCs appeared across five typosquatting groups; each group contained 3–8 domains with one IoC.
- Typosquatting groups showed shared attributes—registrant country, registrar, NS provider—and shared IP addresses in some groups (e.g., 3[.]33[.]130[.]190 and 15[.]197[.]148[.]33).
- WHOIS timeline analysis showed typosquatting domains were spotted between 650 days before and one day after their current WHOIS creation dates.
- Connected-artifact discovery returned 3,051 email-connected domains (28 malicious), 28 IPs (27 malicious), 17 IP-connected domains, and 1,682 string-connected domains (24 malicious).
- RomCom IoCs were all newly registered in 2025; TransferLoader IoCs were registered between Oct 2024 and Apr 2025, with heavy use of Tucows as registrar.
MITRE Techniques
- [T1583 ] Acquire Infrastructure – Domains and hosting infrastructure were provisioned and bulk-registered for attacks, evidenced by “four domains tagged as IoCs … were part of five typosquatting groups” and shared registrars/NS providers.
- [T1566 ] Phishing – Typosquatting domains were created to impersonate legitimate names and likely facilitate credential or malware delivery, shown by look-alike domains surrounding IoCs such as “1day[.]live” and seven look-alike domains.
- [T1598 ] Phishing: Spearphishing via Service – Use of email-connected domains (3,051 email-connected domains, 28 malicious) to enable targeted phishing or delivery infrastructure.
- [T1590 ] Gather Victim Identity Information – Typosquatting and string-connected domains (1,682 string-connected domains) indicate efforts to harvest or imitate target identifiers and branding to support targeting.
- [T1588 ] Obtain Capabilities – Use of multiple registrars, NS providers, and IP sharing among domains indicates procurement and reuse of hosting and delivery capabilities (e.g., shared IPs 3[.]33[.]130[.]190 and 15[.]197[.]148[.]33).
Indicators of Compromise
- [Domain ] typosquatting and IoCs – 1day[.]live, 1drive[.]expert (and 2 more IoC domains)
- [Domain ] RomCom/TransferLoader IoCs – samples: dr365[.]live, livestorage[.]click (and 105 more domains)
- [IP address ] shared hosting context – 3[.]33[.]130[.]190, 15[.]197[.]148[.]33 (shared by a typosquatting group for ~13 months)
- [IP address ] historical sharing – 52[.]72[.]49[.]79 (shared by look-alike domains for ~5 months)
- [Email-connected domain ] infrastructure for phishing – 3,051 email-connected domains discovered, 28 marked malicious (examples available in full dataset)
- [WHOIS dates ] registration timing context – IoCs appeared on feeds 77–271 days before reporting; some typosquatting entries appeared 650 days before current WHOIS creation dates
Read more: https://circleid.com/posts/romcom-and-transferloader-iocs-in-the-spotlight