A multi-stage Java-based botnet loader targeting Turkish Windows users employs heavy obfuscation, sandbox evasion, TOR-based C2, advanced persistence, and a wide range of remote-control capabilities that impacted banks, ISPs, and mid-level organizations. The sample bypassed all public sandboxes and antivirus products except Threat.Zone and evaded EDR/XDR in real incidents, underscoring the need for on-premises sandboxes and dynamic analysis. #TEKLIFALINACAKURUNLER.jar #Adwind
Keypoints
- The campaign targeted Windows systems in Türkiye and Turkish-language users via phishing delivering a 3-stage Java loader (example filename: TEKLIFALINACAKURUNLER.jar).
- The Java sample uses heavy obfuscation, custom ClassLoaders, AES and RC4 decryption steps, and matryoshka-like staged loading to hide stage2 and stage3 payloads.
- The final payload includes TOR components, configuration for .onion C2 addresses, scheduled-task persistence, registry startup, and anti-AV checks to delay or prevent detection.
- Command-and-control is established over TOR with hardcoded ports, password, and many remote-control signals (screenshot, DDOS, file manager, command execution, spreader, uninstall, etc.).
- The loader copies itself to shared network folders to spread (network worm/spreader) and contains commands to disable Defender and add exclusions via PowerShell or registry edits.
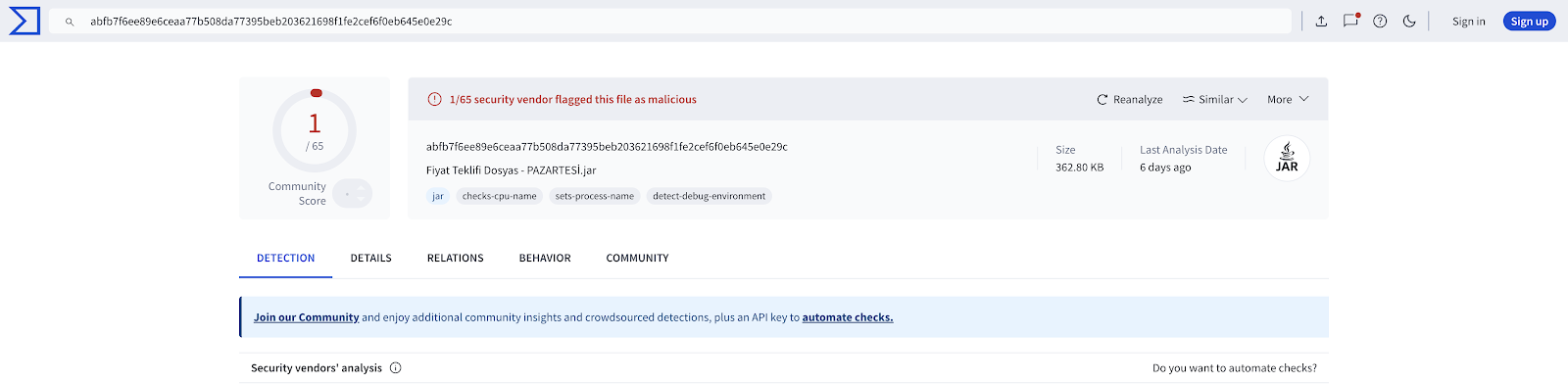
- The sample was tested through Threat.Zone using a Turkish proxy; it successfully evaded all public sandboxes and AVs except Threat.Zone in the researchers’ evaluation.
- IOCs include a SHA256 hash for the initial JAR and two .onion C2 domains; further analysis and a Part 2 will detail honeypot validation and dynamic behavior.
MITRE Techniques
- [T1204] User Execution – Delivered via phishing emails that trick targets into running a Java JAR (“these emails distribute an advanced botnet that comes with a 3-stage loader under files such as ‘TEKLIFALINACAKURUNLER.jar’”).
- [T1218] Signed Binary Proxy Execution (Java) – Uses the Java runtime and custom ClassLoader to load and execute embedded classes at runtime (“Custom ClassLoader…defineClass…loads the resource named stub into memory and defines this file loaded into memory as a Java class at runtime”).
- [T1027] Obfuscated Files or Information – Heavy obfuscation and string encryption applied; researchers ran java-deobfuscator to decrypt strings and remove junk operations (“string decryption and peephole optimization…most of the operations at the main point were junk codes”).
- [T1176] Browser Bookmarking/Session Hijacking (via TOR) – Establishes C2 over TOR to anonymize communications using downloaded Tor Browser/proxy checks (“downloads TOR…sends a request to [check.torproject.org] via the proxy address 127.0.0.1:9050 and checks whether the connection is provided by TOR”).
- [T1543] Create or Modify System Process (Scheduled Task, Registry Run Keys) – Adds itself to scheduled tasks and sets registry startup type for persistence (“adds itself to scheduled tasks…STARTUP_TYPE = ‘REGEDIT’”).
- [T1036] Masquerading – Copies randomly named instances of itself to shared network folders to spread across the local network (“copies randomly named files (malware itself) to shared folders accessed from IP addresses on the local network”).
- [T1497] Virtualization/Sandbox Evasion – Evasion of public sandboxes and AVs observed; researchers used on-premises/testing via Threat.Zone and Turkish proxy to validate (“bypassed every public sandbox and AV aside from Threat.Zone…evaded EDR/XDR in real-world incidents”).
- [T1105] Ingress Tool Transfer – Downloads TOR from dist.torproject.org and other components as needed to enable C2 (“goes to https://dist.torproject.org/torbrowser/ to start the download process and creates the download link using regex”).
- [T1005] Data from Local System – Implements commands for screenshots and exfiltration (“Signal that takes a screenshot and sends it to the server”).
- [T1569] System Services – Executes commands and power-user actions including disabling Defender and running PowerShell as admin (“killdefender: Disable defender or Malware Run as Admin with some Powershell commands”).
Indicators of Compromise
- [File Hash] Initial JAR payload – SHA256: d286acf63f5846e775ba23599e2b5be88d0564d24f29e0646f6cff207249c130 (seen as TEKLIFALINACAKURUNLER.jar and FIYATTEKLIFI.JAR).
- [Domain/.onion] TOR C2 addresses – 4ufbghkgmeb7nevhki3vf5rfwmmrb4bb52xcw2qwbh3qo4x773ttnhqd[.]onion, 42dtw6kxl5zxfpo25yknm2hmqndafoqynk3m6j2luvhi4epeex6arvyd[.]onion.
- [File/Resource] Embedded resource names – resource file ‘d6RuwzOkGZM12DXi’ (stage2 encrypted blob), resource ‘stub’ (RC4-encrypted stage3), and Tor download from dist.torproject.org used in provisioning.