TA-NATALSTATUS is a long-running cryptojacking threat actor that exploits unauthenticated Redis instances to gain root via legitimate Redis commands, then deploys a modular infection chain that hides, persists, and propagates across thousands of exposed servers globally. Their toolkit includes rootkit-style process hijacking, command obfuscation, immutable file locks, and kill lists to remove rival miners, with confirmed IOCs like SSH key comment uc1, Monero wallet 84nw3…, and domains such as natalstatus.org. #TA-NATALSTATUS #natalstatus.org
Keypoints
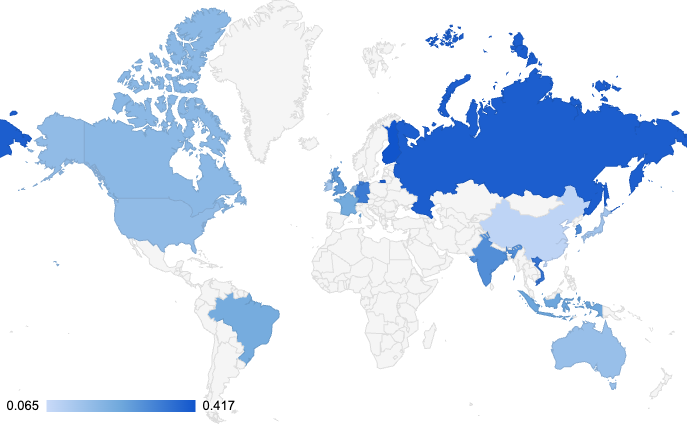
- TA-NATALSTATUS targets unauthenticated Redis servers worldwide, using CONFIG SET and SAVE to write root cron jobs and achieve “root by inheritance.”
- The group operates a four-stage lifecycle: implantation (ndt.sh), preparation (is.sh), propagation (rs.sh), and persistent reinfection (nnt.sh + chattr).
- Stealth techniques include replacing system binaries (ps, top) with wrappers to hide processes, renaming curl/wget to bypass detection, and timestomping to obscure file timelines.
- Persistence is enforced via hourly update scripts and chattr +i immutable flags, plus an SSH backdoor keyed with comment “uc1”.
- Propagation uses distributed scanning (masscan –shard) and compiled scanning tools when package installs fail, enabling large-scale, low-noise coverage of IPv4 space.
- TA-NATALSTATUS enforces resource monopoly with a “kill list” that terminates competing miners (Kinsing, DDG, Watchbog, TeamTNT, etc.).
- Defensive guidance stresses isolating and re-imaging infected hosts, restoring original binaries, removing immutable attributes, and securing Redis (bind 127.0.0.1, strong password).
MITRE Techniques
- [T1592] Gather Victim Network Information – The actor scans the Internet for exposed Redis instances using tools like masscan (“the attacker uses tools like masscan to scan the internet for publicly exposed, unauthenticated Redis servers on port 6379”).
- [T1190] Exploit Public-Facing Application – Abuse of Redis CONFIG SET and SAVE to write to /var/spool/cron/ (“CONFIG SET dir /var/spool/cron/: … CONFIG SET dbfilename root: … SAVE: Forces Redis to write … /var/spool/cron/root”).
- [T1053] Scheduled Task/Job – Use of cron to achieve execution as root (“Injects a malicious cron job (running every 2 minutes) that downloads and executes the malware. The system’s cron daemon reads the new /var/spool/cron/root file and executes the inserted cron job as the root user”).
- [T1543] Create or Modify System Process – Replacing system binaries with malicious wrappers to hide processes (“renaming system binaries like ps and top to ps.original and replacing them with malicious wrappers … filter their own malware … out of the output”).
- [T1036] Masquerading – Renaming or replacing common utilities to evade detection (“They rename curl and wget to cd1 and wd1 … bypass security products that monitor for malicious downloads specifically initiated by these common tool names”).
- [T1070] Indicator Removal on Host – Timestomping to alter file timestamps (“the actor uses touch commands or other methods to alter the timestamps of their files, making them appear to be old system files”).
- [T1490] Inhibit System Recovery – Use of immutable file attributes to prevent deletion (“the script uses ‘chattr +i’ to make its core files and the SSH backdoor key immutable … prevents the files from being deleted or modified, even by the root user”).
- [T1105] Ingress Tool Transfer – Downloading and compiling scanning tools and payloads from C2 when package installs fail (“if tools like ‘masscan’ or ‘pnscan’ cannot be installed via the package manager, the script downloads their source code directly from the C2 server and compiles them from scratch”).
- [T1499] Endpoint Denial of Service – Resource hijacking and terminating rival processes to monopolize CPU (“the script executes its massive ‘kill list’ … terminating dozens of processes associated with competing cryptojacking campaigns … to ensure 100% of the host’s CPU resources are dedicated to their miner”).
Indicators of Compromise
- [SSH Key Comment] persistent backdoor identifier – uc1 (SSH authorized_keys comment used for persistent access)
- [Wallet] Monero payout address – 84nw3MQdDJzRghGBEPWNAtLG8MA1ek1itN42Yup4dPK38wnWGY7zxSR28j2n4vyLspVPoDCFeijap2NTQJfegCTeANTrzotM
- [Domains] C2 / infrastructure – natalstatus.org, a.natalstatus.org, and 2 more domains (avspbx.com, Pyats.topen2an.top)
- [IP Addresses] Confirmed malicious C2 / pools – 103.79.77.161, 85.19.33.145, and other addresses (194.110.247.97, 45.89.52.41, 79.137.195.151, 80.211.206.105)
- [File Hashes] Malicious script binaries – rs.sh (SHA256 04ae5583…266b8), ndt.sh (SHA256 254d0672…5924a), nnt.sh (SHA256 f0ff790b…40771)
- [Paths / Filenames] Common malware locations – /ep9TS2/ (malware directory), /tmp/kinsing, /var/tmp/kinsing, and other common paths (/tmp/java, /tmp/ddg)