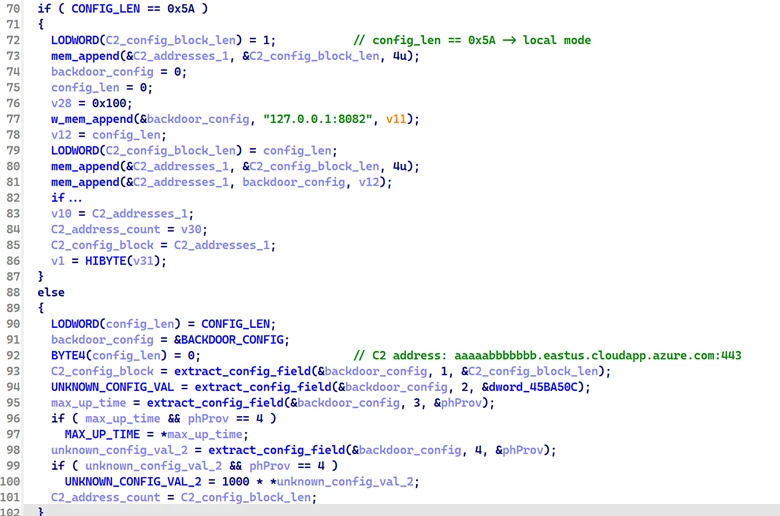
Microsoft observed a modular backdoor named PipeMagic, attributed to financially motivated threat actor Storm-2460, masquerading as a trojanized ChatGPT Desktop Application and used in attack chains exploiting CVE-2025-29824 to deploy ransomware. The malware uses named-pipe encrypted IPC, in-memory modules (network, execute, payload, unknown linked lists), and a TCP-based C2 hosted at aaaaabbbbbbb.eastus.cloudapp.azure[.]com to manage and execute payloads. #PipeMagic #Storm-2460 #CVE-2025-29824
Keypoints
- PipeMagic is a modular in-memory backdoor delivered via a trojanized open-source ChatGPT Desktop Application and an MSBuild-based dropper that uses certutil to fetch the malicious payload.
- The backdoor delegates C2 communication to a separate network module loaded into a network linked list, which initiates TCP/WebSocket-style HTTP GET requests to aaaaabbbbbbb.eastus.cloudapp.azure[.]com.
- PipeMagic maintains multiple doubly linked lists (network, payload, execute, unknown) to stage, update, and execute modules, enabling self-updating and granular remote control.
- The malware collects comprehensive host telemetry (bot ID, OS, computer name, process info, domain/groups, IP, working directory, linked-list node data) and transmits it to C2 as part of the handshake.
- Backdoor inner commands enable module management (insert, write, read, delete, replace), module execution, named-pipe communication, RC4/aPLib handling, and data exfiltration, providing extensive operational flexibility.
- Storm-2460 leveraged PipeMagic alongside the CLFS elevation-of-privilege vulnerability CVE-2025-29824 in targeted campaigns across IT, financial, and real estate sectors globally to deploy ransomware.
- Microsoft provides mitigation guidance including enabling tamper protection, network protection, EDR in block mode, cloud-delivered protections, and specific Defender detections and reports for investigation and response.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used CVE-2025-29824 (Windows CLFS elevation of privilege) as part of the attack chain to escalate privileges before ransomware deployment. Quote: ‘exploitation of CVE-2025-29824, an elevation of privilege vulnerability in Windows Common Log File System (CLFS)’.
- [T1105 ] Ingress Tool Transfer – Threat actor used certutil to download a malicious MSBuild file from a compromised legitimate website to deliver the in-memory dropper. Quote: ‘using the certutil utility to download a file from a legitimate website that was previously compromised to host the threat actor’s malware.’
- [T1055 ] Process Injection – PipeMagic drops and executes malicious payloads in memory (in-memory dropper and in-memory unpacking of modules). Quote: ‘The downloaded payload is a malicious MSBuild file that ultimately drops and executes PipeMagic in memory.’
- [T1574 ] Hijack Execution Flow – Uses trojanized open-source application (ChatGPT Desktop) to run embedded malicious code that decrypts and launches the payload. Quote: ‘malicious in-memory dropper disguised as the open-source ChatGPT Desktop Application project… decrypt and launch an embedded payload in memory.’
- [T1102 ] Web Service – Network module communicates with C2 over TCP using an HTTP GET upgrade to WebSocket-like communication to aaaaabbbbbbb.eastus.cloudapp.azure[.]com. Quote: ‘GET / … Upgrade: websocket … Host: aaaaabbbbbbb.eastus.cloudapp.azure[.]com’.
- [T1027 ] Obfuscated Files or Information – Network module data is XOR-decrypted with a hardcoded 32-byte key then decompressed using aPLib before loading. Quote: ‘This data is first XOR-decrypted using the following hardcoded 32-byte key, then decompressed using the aPLib compression algorithm.’
- [T1041 ] Exfiltration Over C2 Channel – Backdoor sends detailed system information and module results to C2 and receives commands and modules in response. Quote: ‘the backdoor collects a comprehensive set of system and internal state information to send back to the C2 server’ and ‘Backdoor results are delivered to C2 over TCP.’
- [T1106 ] Native API – Uses Windows named pipes and linked-list memory structures for inter-process communication and module staging. Quote: ‘encrypted inter-process communication via named pipes’ and ‘receives payload modules through a named pipe and its C2 server.’
Indicators of Compromise
- [Domain ] PipeMagic C2 domain – aaaaabbbbbbb.eastus.cloudapp.azure[.]com:443 (HTTP GET/Upgrade to websocket behavior)
- [File SHA-256 ] In-memory dropper (trojanized ChatGPT desktop application) – 4843429e2e8871847bc1e97a0f12fa1f4166baa4735dff585cb3b4736e3fe49e
- [File SHA-256 ] PipeMagic backdoor (unpacked in memory) – dc54117b965674bad3d7cd203ecf5e7fc822423a3f692895cf5e96e83fb88f6a
- [File SHA-256 ] PipeMagic network module (unpacked in memory) – 297ea881aa2b39461997baf75d83b390f2c36a9a0a4815c81b5cf8be42840fd1