A transient smishing campaign impersonating UK government and local authority services used hundreds of short-lived, lookalike domains (many on Cloudflare and Dominet registrar) to host parking fine and winter fuel payment lures that only serve content at specific paths like /pay, /bills, or /index.html. Investigators pivoted on a distinctive HTTP header-hash (e4d0cf4f3dc9a95493a2) and observed AJAX /api token issuance and websocket (/ws) exfiltration behavior across multiple domains. #govpcnsvt #e4d0cf4f3dc9a95493a2
Keypoints
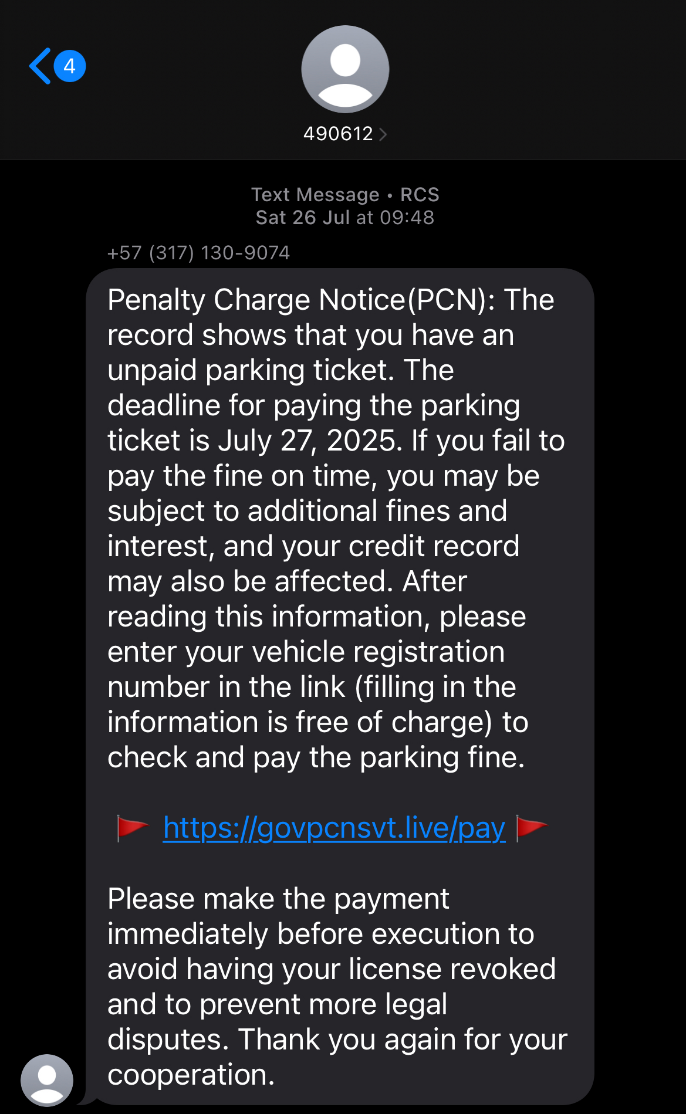
- The initial smishing texts impersonated Penalty Charge Notices and linked to domains such as govpcnsvt.live that resolved for less than 36 hours and were hosted behind Cloudflare.
- Validin analysis identified a reusable host header hash (e4d0cf4f3dc9a95493a2) used across thousands of short-lived domains, enabling high-confidence pivoting and detection.
- Many lookalike domains used algorithmic naming patterns and TLDs like .live, .top, .icu, and shared registrar metadata (Dominet HK).
- Content was generally served only when visiting specific paths (/pay, /bills, /index.html); default visits returned 404 responses, complicating naive scanning approaches.
- Phishing pages used client-side JavaScript to request a token from /api, then established a websocket (/ws) using that token to transmit form-field data (often on each field completion) to the actor-controlled backend.
- Campaign reused the same toolkit for different lures (parking PCN and GOV.UK winter fuel payment), showing consistent AJAX/websocket patterns and Chinese-language console strings for websocket heartbeat handling.
- Research enumerated hundreds of related domains (recent list provided) and recommended hunting rules searching for the header hash and probing the known lure paths with real browser user agents.
MITRE Techniques
- [T1598 ] Phishing – Lures impersonated government/local authority services (PCN and Winter Fuel Payment) delivered via SMS links to credential-/payment-collection pages (“text message containing a phishing message and link to https[:]//govpcnsvt[.]live/pay”).
- [T1588.001 ] Domain Generation – Use of many algorithmically-similar, short-lived domains and lookalike TLDs (e.g., .live, .top, .icu) to host phishing pages (“many similar, undetected domain names…top-level domains such as ‘.date’, ‘.top’, ‘.vip’ and ‘.live’”).
- [T1566.001 ] Spearphishing via Service (SMS/Smishing) – Initial access vector was SMS messages with plausible, region-specific lures (Penalty Charge Notice texts from short codes and phone numbers) (“received two SMS messages…recognized this as a ‘Penalty Charge Notice’ (PCN) scam”).
- [T1071.001 ] Web Protocols – Use of HTTPS-hosted pages and websockets to communicate collected data to actor infrastructure (“there is an AJAX API call to a path on the same host, /api that returned a ‘Token’…there is a websocket connection to another path on the same host, /ws, that passes the token returned from the AJAX API call”).
- [T1530 ] Data from Local System – Form capture of PII and payment details, with websocket messages sent after each field completion to capture partial entries (“observed messages sent via the websocket after every field was completed…attempts to capture as much information as possible in case the user aborts the form”).
- [T1583.001 ] Acquire Domain Names – Actors repeatedly registered many deceptive domains (Dominet HK registrar usage noted) to maintain ephemeral infrastructure (“the use of Dominet HK registrar…these matches all have additional similarities”).
- [T1592 ] Gather Victim Identity Information – Collection of postcode, vehicle registration, PII, and payment card data through multi-step forms (“the first page stated to pay a parking fine where the user would enter their postcode…inputting PII…payment details section…requested additional cards”).
Indicators of Compromise
- [Domain ] Example phishing domains tied to the campaign – govpcnsvt.live, govpcnsnz.live (and hundreds more such as fine.pcnwq.date and gov.engdwpjj.top).
- [Header hash ] Distinctive HTTP header fingerprint used for pivoting – e4d0cf4f3dc9a95493a2 (seen across >5000 responses and many related domains).
- [Paths ] Lure-serving paths used by the sites – /pay, /bills, /index.html (content served only at these paths; root often returns 404).
- [Provider/Hosting ] Cloudflare-hosted ephemeral infrastructure – multiple domains resolving to Cloudflare IPs and name servers before turning NX within 36–48 hours.
- [Platform detections ] VirusTotal classification noted as malicious/DGA for the original domain – govpcnsvt.live tagged as DGA (provider: Alibaba) as of 10 August 2025.
Read more: https://www.validin.com/blog/uk_gov_phishing_investigation_with_validin/