Check Point Research detailed a spearphishing campaign by Iranian threat actor Educated Manticore that used fake Gmail and Google Meet pages to steal credentials and 2FA codes from Israeli journalists, cybersecurity experts, and academics. Researchers identified 141 IoCs (129 domains, 12 IPs) and additional related artifacts, with many domains registered in 2025 via Namecheap and numerous historical DNS/IP resolutions. #EducatedManticore #alpha-man.info
Keypoints
- Educated Manticore conducted spearphishing targeting Israeli journalists, high-profile cybersecurity experts, and computer science professors using fake Gmail login and Google Meet pages.
- Check Point Research reported 141 IoCs comprising 129 domains and 12 IP addresses; researchers expanded analysis to uncover additional related artifacts.
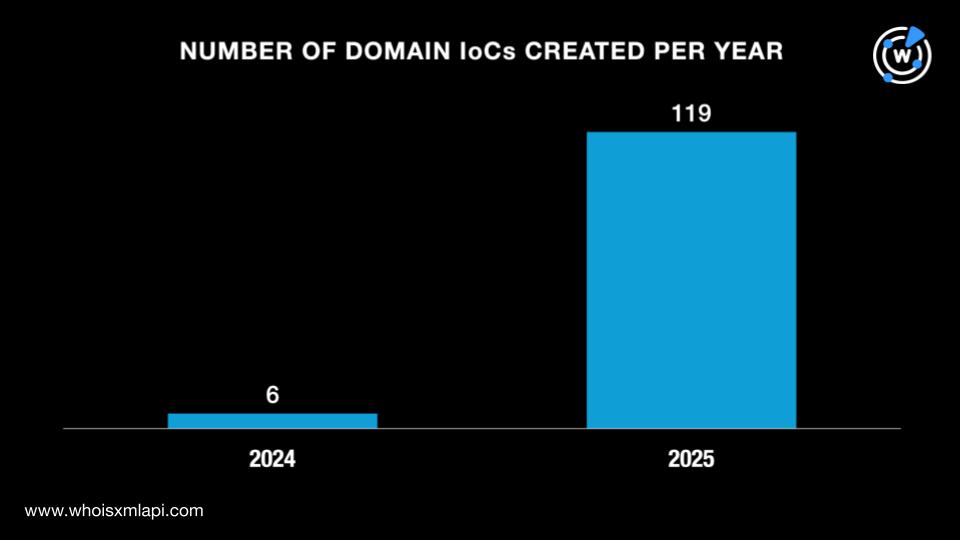
- Bulk WHOIS analysis showed 125 of 129 domains had WHOIS records; 119 domains were created in 2025, and Namecheap registered 111 of them.
- DNS Chronicle data recorded 2,630 historical domain-to-IP resolutions for 123 domains; sample DNS traffic linked 1,753 unique client IPs to queries of 10 domains (14–24 June 2025).
- First Watch feeds showed 72 domains appeared on threat feeds 5–454 days before the public report, indicating earlier detections.
- Of 12 IP IoCs, addresses were geolocated across five countries (Netherlands, UK, France, Ukraine, US) with 6,860 historical IP-to-domain resolutions recorded.
- Expanded analysis found 217 email-connected domains (one malicious), one additional malicious IP (198.54.117.242), and indicators tied to malware distribution and C2 activity.
MITRE Techniques
- [T1566] Phishing – Use of fake Gmail login pages and Google Meet invitations to harvest credentials and 2FA codes (“directed victims who engaged with them to fake Gmail login pages or Google Meet invitations”).
- [T1588] Obtain Capabilities – Registration of大量 (many) domains and infrastructure (129 domains, 12 IPs) to support the campaign (“identified 141 indicators of compromise (IoCs) comprising 129 domains and 12 IP addresses”).
- [T1608] Stage Capabilities – Use of domain and IP provisioning through registrars/hosting (Namecheap, NameSilo, Dynadot; ISPs like BlueVPS, Hostkey) to host phishing infrastructure (“Namecheap, which accounted for 111 domains… BlueVPS, which accounted for three IP addresses”).
- [T1598] Phishing: Spearphishing Attachment/Link – Directing targets to malicious pages via links in communications (fake Google Meet invites and links to Gmail login pages) (“directed victims… to fake Gmail login pages or Google Meet invitations”).
- [T1040] Network Sniffing/Intercept – Capturing credentials and 2FA codes submitted to phishing pages, enabling interception and account takeover (“credentials the victims entered on phishing pages were sent to the attackers, enabling them to intercept passwords and two-factor authentication (2FA) codes”).
Indicators of Compromise
- [Domains] Reported phishing domains and related domains – alpha-man.info, conn-ectionor.cfd, and 126 more (129 total domains, sample: world-shop.online, spring-club.info).
- [IP Addresses] IP IoCs used by infrastructure – 185.130.226.71 (observed communicating with a source IP), 195.66.213.132 (oldest IP-to-domain resolution), and 10 more IPs (12 total).
- [Email-connected domains] Domains tied via historical WHOIS emails – top-game.online (identified in malware distribution) and 216 more linked domains (217 total email-connected domains).
- [Registrant/Registrar Data] Registrar and registrant country artifacts – Namecheap-registered domains (111 domains), registrant country examples: Iceland (57 domains), United States (13 domains).
- [Additional Malicious IP] Newly discovered malicious IP – 198.54.117.242 (linked to malware distribution, phishing, suspicious activity, and C2).
Read more: https://circleid.com/posts/a-dns-exploration-of-the-latest-educated-manticore-attack