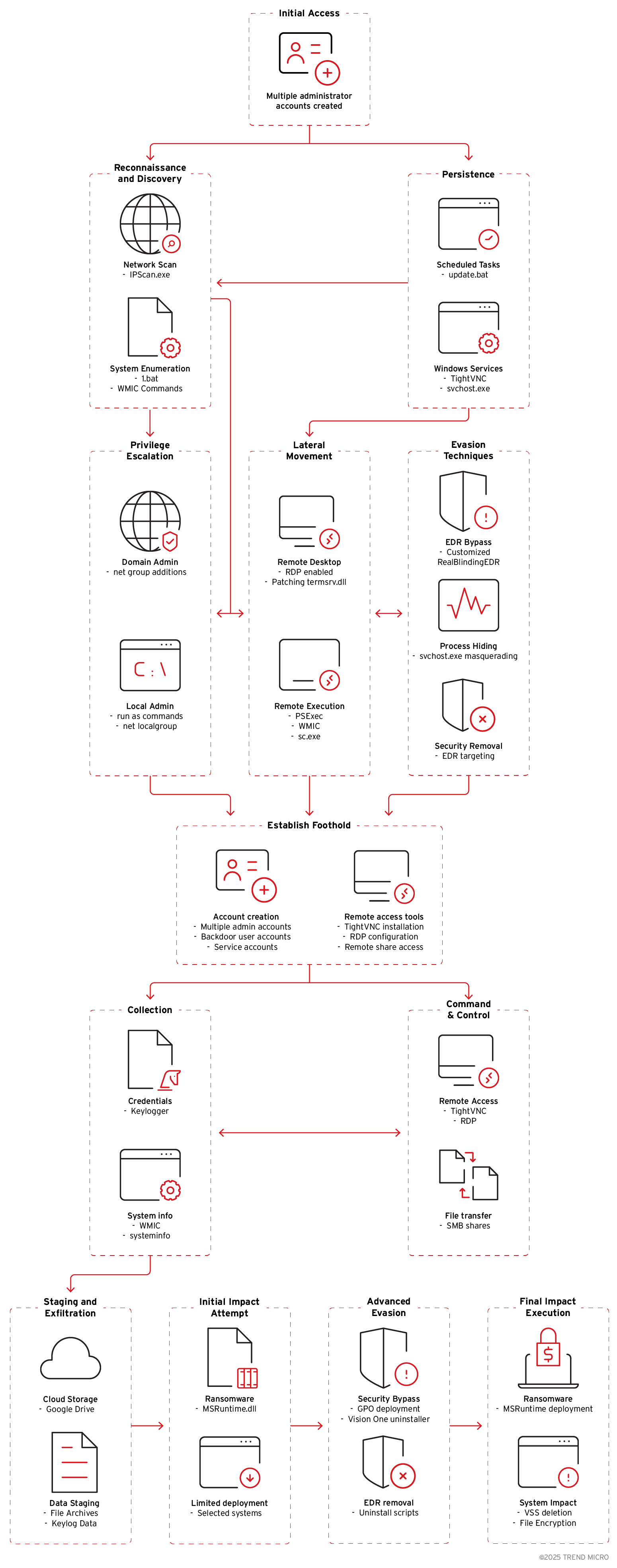
Crypto24 conducts coordinated, multi-stage ransomware attacks combining legitimate administrative tools (PsExec, AnyDesk, gpscript.exe) with custom malware (keyloggers, MSRuntime.dll, RealBlindingEDR variant) to gain persistence, move laterally, and evade EDR. The group targets large enterprises across Asia, Europe, and the USA, exfiltrates data via Google Drive, and disables security agents using tools like XBCUninstaller.exe. #RealBlindingEDR #XBCUninstaller.exe
Keypoints
- Operators blend living-off-the-land tools (PsExec, gpscript.exe, net.exe, sc.exe, runas.exe) with custom malware to minimize detection and enable lateral movement.
- Persistence is achieved via privileged account creation, scheduled tasks in %ProgramData%Update, and malicious Windows services (WinMainSvc, MSRuntime).
- Defense evasion includes a customized RealBlindingEDR-like tool that targets security product drivers and the use of Trend Vision One uninstaller (XBCUninstaller.exe) executed via gpscript.exe.
- Credential theft and surveillance use a keylogger (WinMainSvc.dll) that logs keystrokes and uploads data to Google Drive using the Drive API via WinINet.
- Privilege escalation and lateral movement leverage PsExec, patched termsrv.dll for concurrent RDP sessions, firewall rule changes, and remote administration tools (TightVNC, AnyDesk).
- Attackers conduct reconnaissance with WMIC and custom scripts (1.bat) to collect system, partition, and account information for targeting high-value hosts.
- Targets include financial services, manufacturing, entertainment, and technology organizations in Asia, Europe, and the USA; Trend Vision One provides detections and hunting queries for these IOCs.
MITRE Techniques
- [T1078] Valid Accounts – Re-enabled default admin accounts and created multiple new users with net.exe to maintain privileged access (“net user”, “net localgroup”).
- [T1053] Scheduled Task/Job – Scheduled tasks and scripts in %ProgramData%Update% (update.vbs, vm.bat) used for persistence and timed payload execution.
- [T1543] Create or Modify System Process – Created malicious services via sc.exe (WinMainSvc, MSRuntime) to run keylogger and ransomware as services.
- [T1190] Exploit Public-Facing Application – Abused gpscript.exe (Group Policy utility) to remotely execute Trend Vision One uninstaller (XBCUninstaller.exe) from a network share (“cmd /c “…VisionOne_removal_v2.bat” XBCUninstaller.exe”).
- [T1105] Ingress Tool Transfer – Downloaded and executed tools (psexec64.exe, ipscan installer, TightVNC) and custom binaries onto hosts for lateral movement and remote access.
- [T1021] Remote Services – Used PsExec and PSEXESVC.exe, enabled RDP and added firewall rules to allow remote connections (“advfirewall firewall add rule … localport=3389”).
- [T1547] Boot or Logon Autostart Execution – Ensured persistence by creating services and scheduled tasks that run at startup or regular intervals (svchost.exe -k WinMainSvc).
- [T1069] Permission Groups Discovery – Queried local groups and accounts using WMIC and net.exe to discover privileged accounts and membership for lateral movement (“wmic …”, “net localgroup administrators”).
- [T1056] Input Capture – Deployed WinMainSvc.dll keylogger to capture keystrokes and active window titles, logging input and uploading via Google Drive API (“creation of WinMainSvc.dll” and scheduled task).
- [T1531] Account Discovery – Used scripts (1.bat) and WMIC commands to gather system and account information for profiling compromised hosts (“wmic partition get name,size,type”).
- [T1403] Disable or Modify Security Tools – Used a RealBlindingEDR-like tool to remove callbacks from security drivers and uninstall EDR agents, targeting a list of security vendors (“removes callbacks only from products identified as belonging to these companies”).
- [T1036] Masquerading – Named services and binaries to resemble legitimate system components (displayname “Microsoft Runtime Manager”, “Microsoft Help Manager”) to blend with normal processes.
- [T1071] Application Layer Protocol – Exfiltrated data to Google Drive using the Google Drive API over WinINet to upload test files and captured keystrokes (“creates Test.txt and uploads to Google Drive”).
Indicators of Compromise
- [File Name] Persistence and payloads – WinMainSvc.dll (keylogger), MSRuntime.dll (ransomware), AVB.exe/AVMon.exe/avb.exe (RealBlindingEDR-like tools).
- [File Path] Malicious scripts and installers – %ProgramData%Updateupdate.vbs, %ProgramData%Updatevm.bat, %PROGRAMDATA%updateavb.exe, C:tempvo_remove2XBCUninstaller.exe.
- [Command/Utility] Tools and commands observed – psexec64.exe (remote execution), gpscript.exe executing VisionOne_removal_v2.bat/XBCUninstaller.exe, sc.exe creating services, net.exe account changes.
- [Scheduled Task/Service] Persistence artifacts – Scheduled tasks in %ProgramData%Update, services named WinMainSvc and MSRuntime (svchost.exe -k WinMainSvc) used for keylogging and ransomware.
- [Network/Cloud] Data exfiltration destination – Google Drive uploads (Test.txt and keystroke logs) via Google Drive API and WinINet usage.
Read more: https://www.trendmicro.com/en_us/research/25/h/crypto24-ransomware-stealth-attacks.html