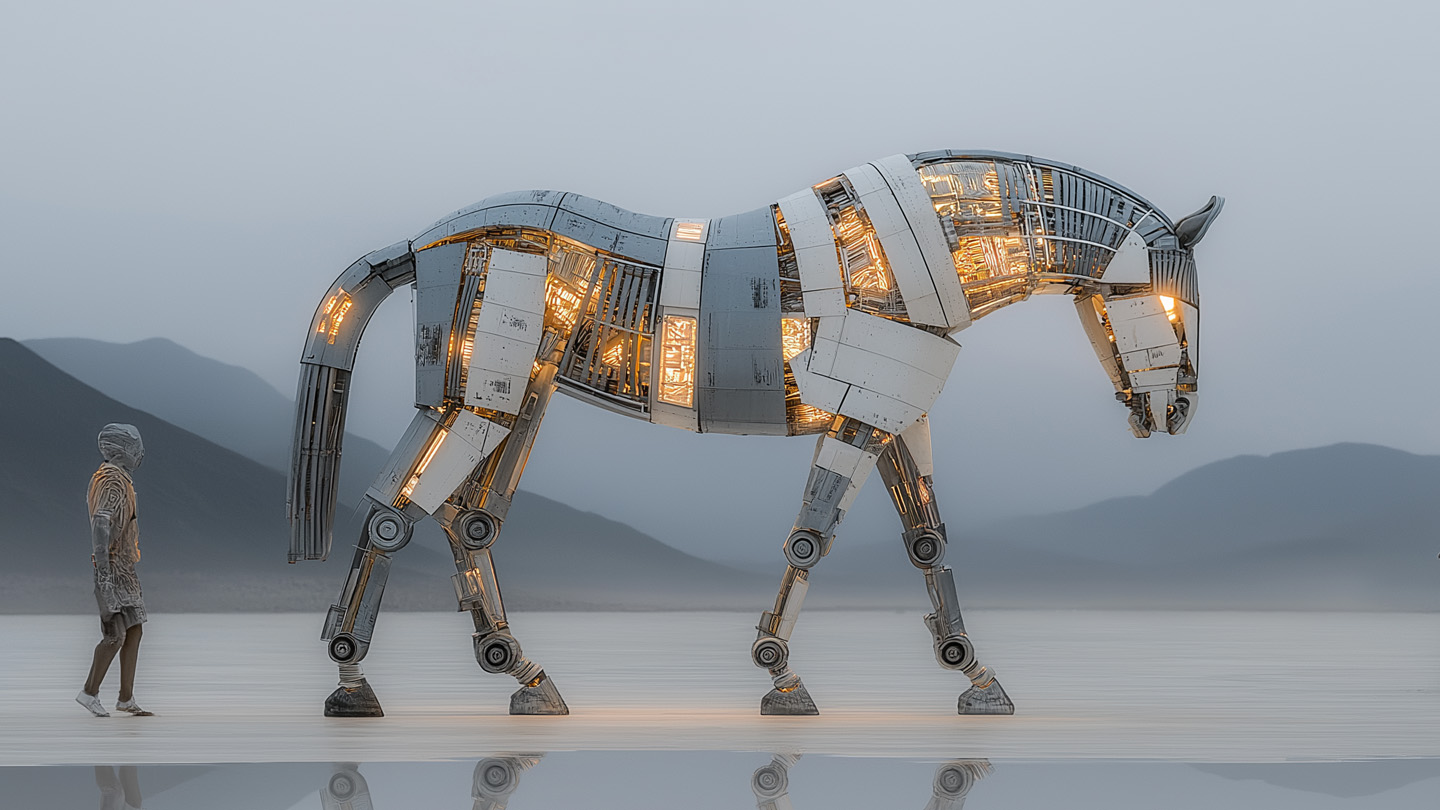
Trojan-style backdoors are resurging because AI/LLMs let threat actors cheaply generate convincing decoy apps, websites, and novel code that evade static multiscanner detection. Examples include JustAskJacky and TamperedChef, which use scheduled tasks, remote command execution, and steganographic command delivery. #JustAskJacky #TamperedChef
Keypoints
- AI and LLMs enable threat actors to generate convincing websites, content, and application code that make trojanized software appear legitimate.
- JustAskJacky schedules tasks and executes arbitrary code fetched from its C2 using eval, allowing remote command execution.
- TamperedChef hides backdoor commands in whitespace within recipe content and remained undetected on VirusTotal for six weeks.
- Multiscanner services like VirusTotal rely mainly on static detection, so novel, well-structured LLM-generated code can evade them without packing.
- Readable, well-commented code structures can indicate LLM assistance, as threat actors may not obfuscate generated outputs.
- Defenses should emphasize context-, behavior-, and dynamic-analysis rather than solely static signatures to detect these trojan horses.
- Users’ traditional heuristics (site appearance, grammar) are less reliable because LLMs can produce high-quality deceptive content.
MITRE Techniques
- [T1053] Scheduled Task/Job – JustAskJacky “schedules a task behind your back that autoruns her code at random times several times a day”
- [T1059] Command and Scripting Interpreter – JustAskJacky executes arbitrary code from its C2 using eval; “JustAskJacky executes arbitrary code from its C2 server using eval”
- [T1105] Ingress Tool Transfer – Malware fetches commands/code from a remote C2 server: “the very same server that she uses to obtain answers … also sends Jacky evil commands behind your back”
- [T1005] Data from Local System (steganography use) – TamperedChef decodes commands hidden in recipes’ whitespace: “any tab, space, or other white space characters … are interpreted as commands to execute” (translated quote)
- [T1566] Phishing (Decoy/Deception) – Use of convincing websites and decoy applications to trick users into installing trojanized software: “These websites look professional … they do not ‘feel’ shady”
Indicators of Compromise
- [File Hash ] JustAskJacky sample – 8ecd3c8c126be7128bf654456d171284f03e4f212c27e1b33f875b8907a7bc65
- [File Hash ] TamperedChef sample – 1619bcad3785be31ac2fdee0ab91392d08d9392032246e42673c3cb8964d4cb7
- [Domain ] Malicious decoy sites used to distribute trojans – images-searcher(dot)com, recipelister(dot)com, and justaskjacky(dot)com
Read more: https://www.gdatasoftware.com/blog/2025/08/38247-justaskjacky-ai-trojan-horse-comeback