FIDO-based passkeys greatly reduce credential phishing and ATO risks, but Proofpoint researchers show attackers can force a downgrade from FIDO to weaker authentication using a tailored AiTM phishlet. While not observed in the wild yet, this technique could enable session cookie theft and account takeover, particularly via Evilginx-style frameworks. #FIDO #Evilginx #MicrosoftEntraID
Keypoints
- Proofpoint researchers demonstrated a FIDO authentication downgrade attack that forces users to fallback to less secure auth methods via a dedicated phishlet.
- The attack leverages AiTM frameworks (e.g., Evilginx) and user-agent spoofing to present an unsupported browser profile and trigger alternative sign-in flows.
- Successful downgrades allow interception of credentials, MFA tokens, and session cookies, enabling session hijack and account takeover.
- The technique exploits environments where alternative MFA/recovery methods are configured alongside FIDO (common for account recovery).
- Researchers have not observed this downgrade attack in the wild; attackers currently favor simpler targets with weak or no MFA.
- Implementations like Microsoft Entra ID and Windows Hello for Business have been highlighted as susceptible to downgrade strategies in certain contexts.
- Despite low observed usage, Proofpoint considers FIDO downgrade a meaningful emerging threat for sophisticated actors and APTs.
MITRE Techniques
- [T1556] Modify Authentication Process – Attackers spoof the user agent and modify the authentication flow to force fallback to less secure methods: ‘…they can adjust the AiTM to spoof an unsupported user agent, which is not recognized by a FIDO implementation. Subsequently, the user would be forced to authenticate through a less secure method.’
- [T1185] Man-in-the-Middle – Use of AiTM phishing frameworks (Evilginx/EvilProxy/Tycoon) to intercept credentials and session tokens: ‘…a reverse proxy server, which relays traffic between the victim and the actual service… enabling a complete session hijacking.’
- [T1110] Brute Force / Credential Access (credential harvesting) – Phishlets configured to harvest credentials and session cookies from victims during the downgraded authentication flow: ‘…the threat actor is able to intercept and view the login credentials and session cookie, as they would in a standard AiTM phishing attack.’
- [T1539] Steal Web Session Cookie – Importing stolen session cookies into attacker browser to hijack sessions: ‘…the attacker can hijack the authenticated session by importing the stolen session cookie into their own browser, thus granting them access to the victim’s account.’
Indicators of Compromise
- [Phishing framework] Evilginx context – dedicated FIDO Downgrade phishlet used to force authentication fallback; example: Evilginx phishlet for Microsoft Entra ID.
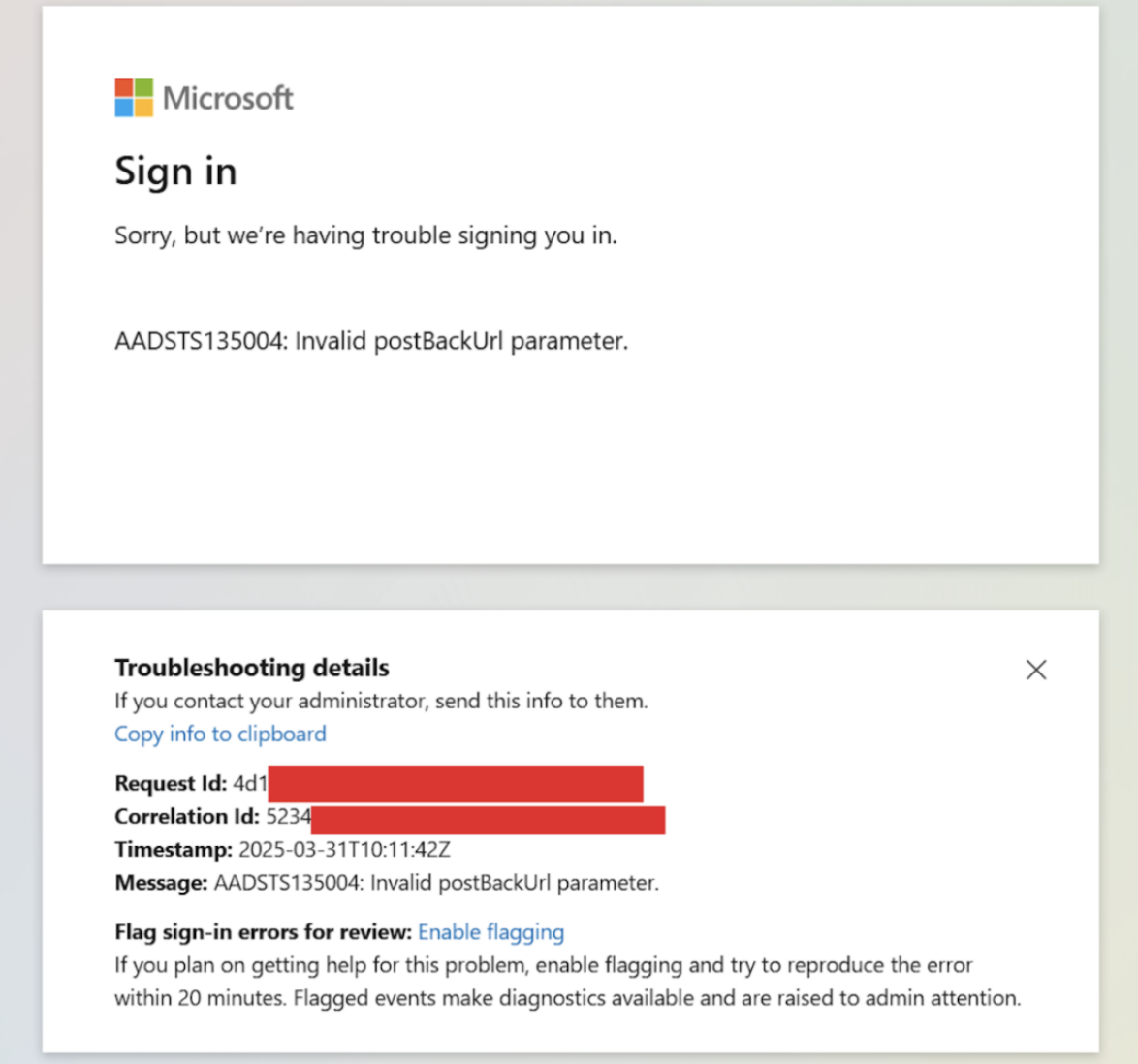
- [Authentication error pages] UI artifacts context – error and alternative sign-in prompts shown to victims during downgrade flow; example: sign-in error and method selection pages as captured in screenshots.
- [Session artifacts] session cookies context – intercepted session cookies shown in Evilginx console; example: captured session entries and cookie details (and other session cookies).
- [Credentials] harvested usernames/passwords context – captured credentials displayed in Evilginx console; example: victim credentials shown alongside cookies (and 2 more credential instances).