Darktrace detected and contained an Auto-Color backdoor intrusion against a US chemical company that exploited CVE-2025-31324 in SAP NetWeaver to deliver a Linux ELF RAT and attempt C2 communication. The investigation revealed Auto-Color uses ld.so.preload persistence, suppresses activity if C2 is unreachable, and this is the first observed pairing of SAP NetWeaver exploitation with Auto-Color. #CVE-2025-31324 #Auto-Color
Keypoints
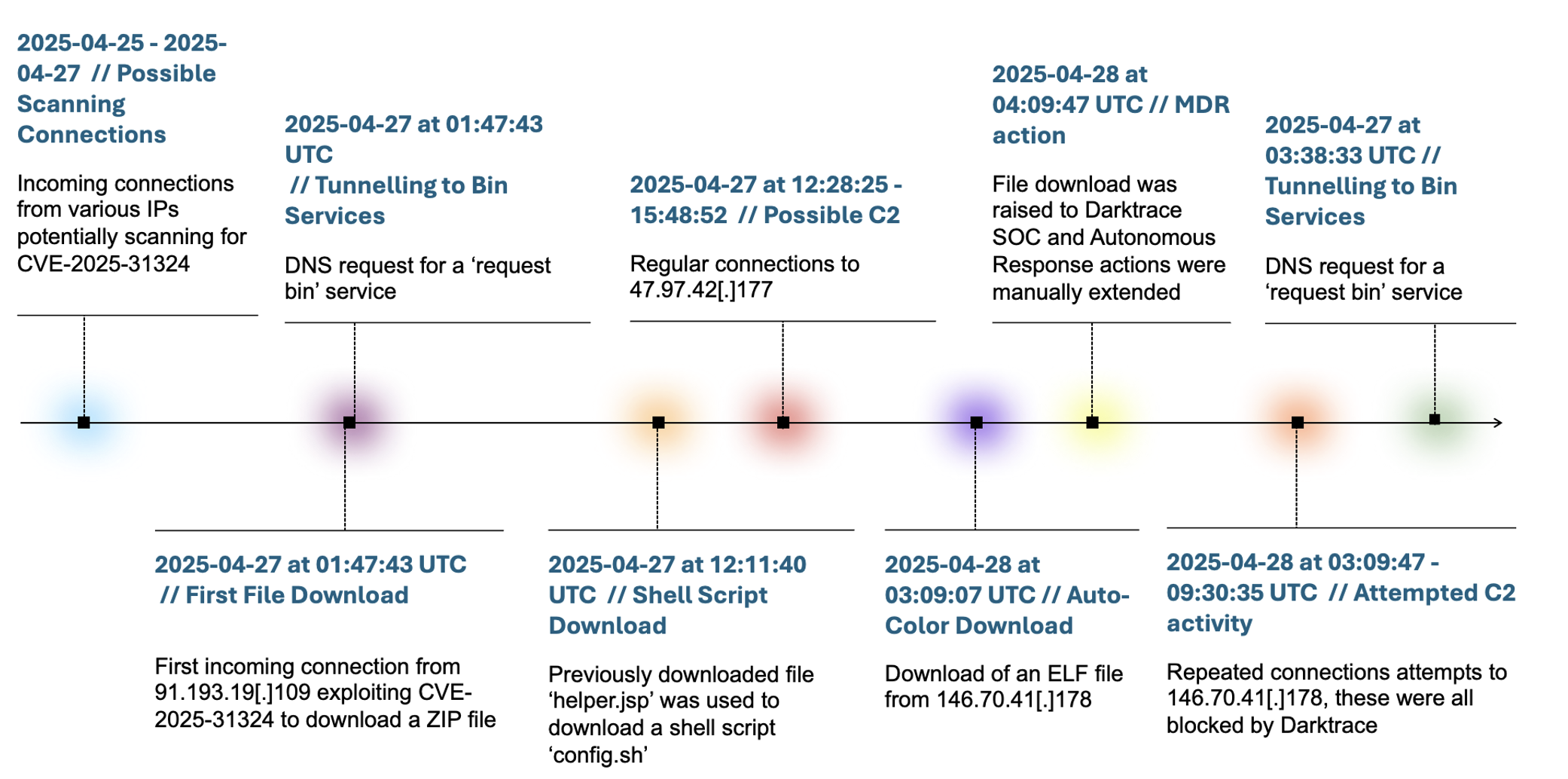
- Darktrace identified an Auto-Color backdoor attack on a US chemicals company that unfolded over three days and was blocked by Autonomous Response.
- The threat actor exploited CVE-2025-31324 in SAP NetWeaver to upload files and deliver an ELF representing Auto-Color.
- Auto-Color targets Linux, leverages ld.so.preload for persistence (writing libcext.so.2), and renames itself to /var/log/cross/auto-color.
- The malware adapts to privilege level: limited behavior without root, full shared-object implant and preload modification with root.
- Auto-Color attempts outbound TLS C2 to hardcoded IPs (e.g., 146.70.41.178) and suppresses malicious actions if C2 is unreachable, evading analysis.
- Darktrace observed DNS tunnelling, ZIP downloads, helper.jsp execution, connections to Supershell-associated endpoints, and multiple file downloads.
- Darktrace’s SOC extended Autonomous Response and MDR actions, preventing C2 establishment and giving the customer time to remediate.
MITRE Techniques
- [T1588.001] Resource Development – Initial malware/utility acquisition and staging to support the attack: “the download of Auto-Color malware”
- [T1189] Drive-by Compromise – Initial access via exploitation of internet-facing SAP NetWeaver and ZIP/file download: “incoming connections using URIs containing /developmentserver/metadatauploader”
- [T1001] Data Obfuscation – Command and control used DNS tunnelling/out-of-band testing domains to hide activity: “made a DNS request for the Out-of-Band Application Security Testing (OAST) domain”
- [T1571] Non-Standard Port – Use of uncommon ports for C2 communications: “connections to 47.97.42[.]177 over port 3232”
- [T1048.003] Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol – DNS-based tunnelling and request-bin-style OAST usage for potential data exfiltration: “OAST … can also be leveraged to tunnel data out of a network via DNS requests”
- [T1036] Masquerading – Malware names and locations to blend in with system files: “renam[e] itself to ‘/var/log/cross/auto-color’ … masquerading as a legitimate C utility library”
- [T1071] Application Layer Protocol – Use of HTTPS/TLS for C2 communications and API-style requests: “attempts to establish an outbound TLS connection to a hardcoded IP over port 443”
- [T1059.004] Unix Shell – Execution of downloaded shell scripts via helper.jsp: “downloaded a shell script named config.sh. Execution: This script was executed via the helper.jsp file”
- [T1546.006] LC_LOAD_DYLIB Addition – Persistence by adding malicious shared object to preload configuration: “modifies or creates /etc/ld.so.preload, inserting a reference to the malicious library”
- [T1036.005] Match Legitimate Resource Name or Location – Placing implants in log-like directories to appear legitimate: “copies and renames itself to ‘/var/log/cross/auto-color’”
- [T1071.001] Web Protocols – C2 using web protocols for command and control: “receive commands or payloads from its operator via API requests”
Indicators of Compromise
- [File Hash] Auto-Color sample – 270fc72074c697ba5921f7b61a6128b968ca6ccbf8906645e796cfc3072d4c43 (sha256)
- [Filenames] Downloaded files observed – exploit.properties, helper.jsp, cmd.js, config.sh, and other downloaded filenames (e.g., uid.jsp, vregrewfsf.jsp)
- [IP Address] C2 / malicious hosts – 146.70.41[.]178 (Auto-Color delivery/C2), 91.193.19[.]109 (initial exploit source)
- [Domain] OAST / tunnel domains – aaaaaaaaaaaa[.]d06oojugfd4n58p4tj201hmy54tnq4rak[.]oast[.]me and ocr-freespace.oss-cn-beijing.aliyuncs[.]com (used to host config.sh)
Read more: https://darktrace.com/blog/auto-color-backdoor-how-darktrace-thwarted-a-stealthy-linux-intrusion