Socket’s Threat Research Team uncovered a long-running supply chain attack in the RubyGems ecosystem where a threat actor using aliases such as zon, nowon, kwonsoonje, and soonje published 60 malicious gems that deliver advertised automation functions while covertly exfiltrating credentials to attacker-controlled infrastructure. The campaign, targeting primarily South Korean users and grey-hat marketers with Korean-language GUIs and C2 domains like programzon[.]com and marketingduo[.]co[.]kr, remains active with dozens of gems still available and over 275,000 downloads reported. #zon #marketingduo
Keypoints
- Since at least March 2023, the threat actor published 60 malicious RubyGems across four aliases (zon, nowon, kwonsoonje, soonje), with 16 gems still live at the time of reporting.
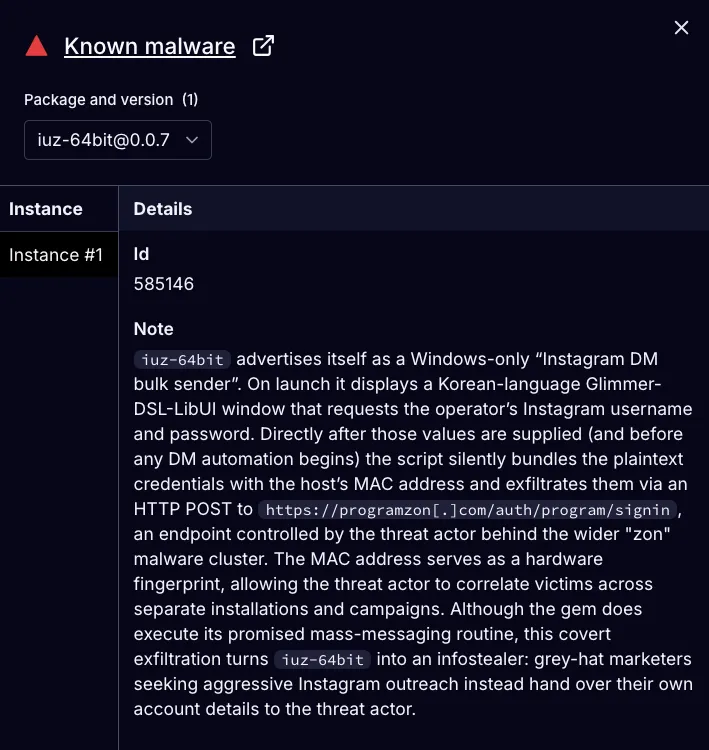
- Each gem provides advertised automation functionality (Instagram, TikTok, Twitter/X, WordPress, Telegram, Naver, etc.) while covertly exfiltrating plaintext credentials and MAC addresses to attacker-controlled servers.
- Exfiltration occurs via HTTP POST to C2 endpoints such as programzon[.]com, appspace[.]kr, and marketingduo[.]co[.]kr, which host simple PHP bulletin-board endpoints for credential collection.
- The campaign is tailored to South Korean users (Korean-language UIs, variable names, and region-specific infrastructure) but lacks geofencing and can be globally exploited.
- Victims are primarily grey-hat marketers using disposable accounts and automation tooling, enabling the malware to operate in plain sight and limiting incident reporting by victims.
- The actor cycles aliases and infrastructure, yanking packages from RubyGems while relying on mirrored archives and cached installations to maintain persistent distribution and evade attribution.
- Notable dual-use gems target financial forums to enable bulk posting for stock manipulation (e.g., njongto_duo), while simultaneously harvesting credentials for persistent access.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Malicious packages were published to the RubyGems ecosystem to deliver credential-stealing functionality (‘long-running supply chain attack in the RubyGems ecosystem’)
- [T1608.001 ] Stage Capabilities: Upload Malware – The actor uploaded and published 60 malicious gems across multiple aliases to stage and distribute the infostealer (‘published 60 malicious gems posing as automation tools’)
- [T1204.002 ] User Execution: Malicious File – Victims install and run Ruby gems with embedded GUIs that prompt for credentials, triggering the malicious behavior (‘Each gem includes a lightweight graphical interface… prompting the operator to enter credentials’)
- [T1056.002 ] Input Capture: GUI Input Capture – The bundled Korean-language GUIs capture user credentials and immediately exfiltrate them via HTTP POST (‘credentials are immediately exfiltrated via HTTP POST requests to threat actor-controlled servers’)
- [T1016 ] System Network Configuration Discovery – The malware collects host identifiers such as MAC addresses to fingerprint victims and correlate infections (‘mac = get_mac_address’)
- [T1041 ] Exfiltration Over C2 Channel – Collected credentials and host data are sent to attacker-controlled C2 endpoints over HTTP(S) channels (‘credentials and MAC addresses are silently sent to one of several threat actor-controlled servers’)
Indicators of Compromise
- [Malicious Gems ] RubyGems package names used to distribute the infostealer – iuz-64bit, njongto_duo, and 58 more malicious gems (total 60 packages)
- [Domains / C2 Endpoints ] Attacker-controlled servers used for credential collection and control – programzon[.]com, appspace[.]kr, and 3 more endpoints including marketingduo[.]co[.]kr and seven1.iwinv[.]net
- [Email Addresses ] Email accounts embedded in gems or contact metadata – mymin26@naver[.]com, marketingduo@marketingduo[.]com
- [Chat / Redirects ] Messaging and recruitment channels linked to the actor – open[.]kakao[.]com/o/sCxh7vCd (Kakao OpenChat room)
- [Third-party Services Observed ] Services and panels observed in infostealer logs tied to victim activity – smmdoge[.]com, accs-market[.]com (and other SMM/backlink/automation platforms)
Read more: https://socket.dev/blog/60-malicious-ruby-gems-used-in-targeted-credential-theft-campaign