Research reveals that default AWS service roles often grant overly broad permissions, especially AmazonS3FullAccess, which can lead to privilege escalation and account compromise. These overly permissive roles affect multiple AWS services such as SageMaker, Glue, and EMR, as well as open-source projects like Ray, prompting AWS to issue mitigations and updated security guidelines. #AmazonS3FullAccess #AWSGlueServiceRole #SageMakerAI #RayProject
Keypoints
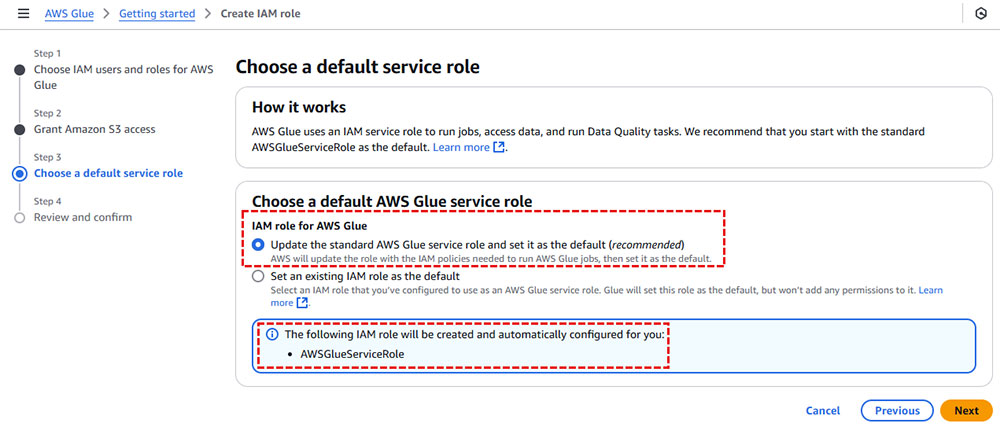
- Default AWS service roles, like AWSGlueServiceRole and SageMaker execution roles, often include the AmazonS3FullAccess policy granting wide S3 access across the account.
- Broad S3 permissions allow attackers to manipulate essential AWS service assets stored in S3, enabling lateral movement and privilege escalation within accounts.
- Attack scenarios demonstrated include importing malicious Hugging Face models in SageMaker to inject backdoors and modifying Glue jobs to inject privileged CloudFormation templates.
- Open-source projects, notably Ray, create default IAM roles with AmazonS3FullAccess, extending the risk beyond AWS managed services.
- AWS responded by scoping down default role permissions, updating documentation, and notifying affected users to remediate risks.
- Organizations are advised to audit and limit default roles to least privilege, avoiding broad policies like AmazonS3FullAccess on service roles.
- Aqua Security’s platform assists in detecting overly permissive IAM roles via their ‘IAM Role Policies’ plugin to enhance cloud security posture.
MITRE Techniques
- [T1078] Valid Accounts – Attackers exploit default AWS roles such as SageMaker execution roles to execute code with AmazonS3FullAccess, enabling access to multiple services (‘an attacker could upload a malicious model to Hugging Face to target AWS SageMaker AI users’).
- [T1210] Exploitation of Remote Services – Malicious Hugging Face models loaded into SageMaker trigger remote code execution during model deployment (‘SageMaker will still automatically run the inference.py file during model deployment’).
- [T1071] Application Layer Protocol – Attackers modify Glue jobs to scan and alter CloudFormation templates stored in S3, escalating privileges (‘Glue job modifies it before the stack creation process completes, injecting a malicious resource’).
- [T1136] Create Account – The injection of new IAM roles with administrative privileges through tampered CloudFormation templates enables attacker privilege escalation (‘the attacker can exploit this opportunity to inject a new IAM role with administrative permissions’).
- [T1550] Use of Trusted Credentials – Abuse of overly permissive default roles (e.g., AWSGlueServiceRole) to perform unauthorized actions in the AWS environment (‘default service roles with overly broad permissions, often including the AmazonS3FullAccess policy’).
Indicators of Compromise
- [IAM Role] Default AWS service roles granting AmazonS3FullAccess – AWSGlueServiceRole, AmazonSageMaker-ExecutionRole-, AmazonEMRStudio_RuntimeRole_
- [File Name] Malicious Hugging Face model files – inference.py containing malicious model_fn and predict_fn functions
- [S3 Bucket] Service-specific buckets targeted for manipulation – cf-templates-*, cdk-*-assets-*, sagemaker-*, aws-emr-studio-*, aws-glue-assets-*
Read more: https://www.aquasec.com/blog/shadow-roles-aws-defaults-lead-to-service-takeover/