Koske is a sophisticated AI-assisted Linux malware campaign that delivers modular cryptomining payloads via polyglot image files and employs evasive rootkits for stealth and persistence. The malware dynamically adapts its network configurations and mining targets using techniques suggestive of AI automation to maintain long-term covert operations. #Koske #ccminer #JupyterLab #hideproc.so
Keypoints
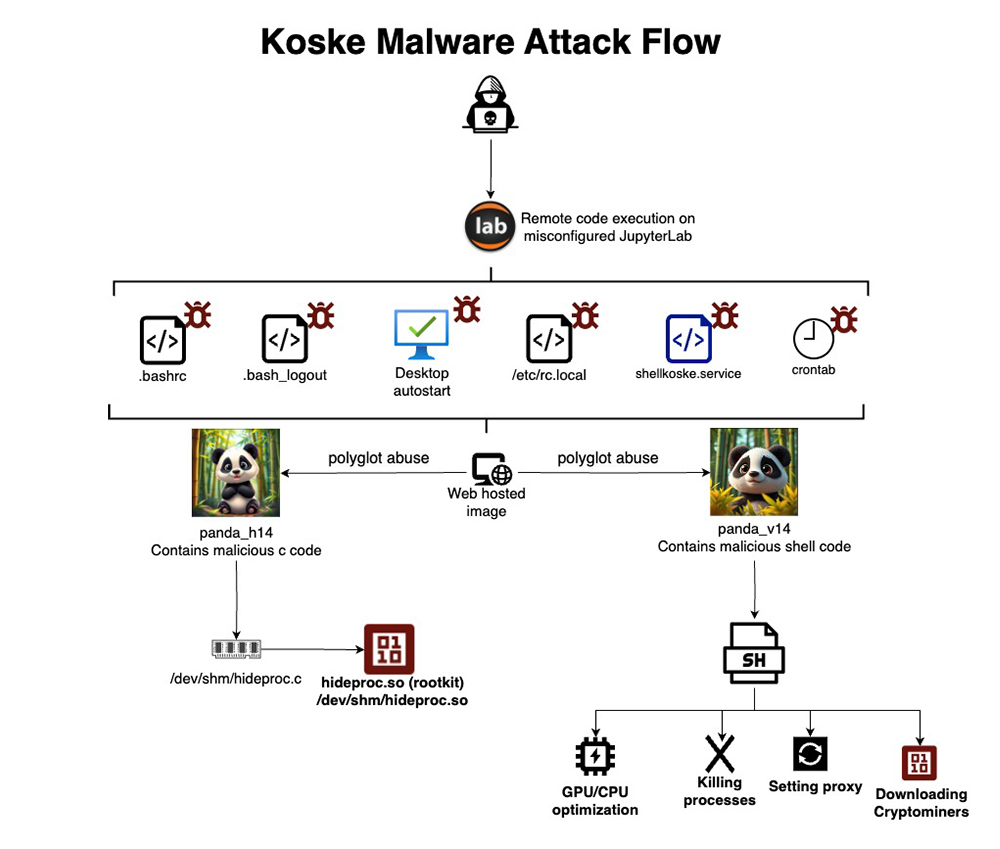
- Koske malware exploits a misconfigured JupyterLab server at IP 178.220.112.53 for initial access.
- It delivers dual payloads embedded in polyglot JPEG image files retrieved from free image hosting platforms, bypassing antivirus detection.
- Persistence is maintained through shell configuration hijacking, system boot manipulation, cron jobs, and dedicated systemd services.
- The rootkit payload hijacks the readdir() function using LD_PRELOAD to hide files, directories, and processes related to the malware.
- The malware aggressively modifies network settings, including resetting proxy variables, flushing iptables, and locking DNS resolution files to ensure C2 communication.
- Koske supports mining 18 cryptocurrencies with hardware detection and auto-switching capabilities for resilient cryptomining operations.
- Indicators suggest Koske’s code was created or assisted by large language models, showing well-structured, defensive scripting with obfuscated authorship.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Initial access via exploitation of a misconfigured JupyterLab instance. (‘exploitation of a misconfiguration JupyterLab instance from a Serbian IP address 178.220.112.53’)
- [T1041] Exfiltration Over C2 Channel – Malware maintains communication with C2 infrastructure using altered network configurations. (‘communicate with command-and-control (C2) infrastructure’)
- [T1547] Boot or Logon Autostart Execution – Persistence through modification of /etc/rc.local linked to a custom systemd service. (‘modifies /etc/rc.local and attaches it to a custom systemd service for privileged execution at boot’)
- [T1053] Scheduled Task/Job – Use of cron jobs scheduled every 30 minutes and at reboot. (‘Schedules tasks at 30-minute intervals and on reboot’)
- [T1035] Service Execution – Creation of shellkoske.service as a resilient execution manager. (‘Establishes shellkoske.service, a resilient self-restarting downloader and execution manager’)
- [T1564] Hide Artifacts – Rootkit uses LD_PRELOAD to hijack readdir() function and hide files/processes. (‘hijacks the standard readdir() function using the LD_PRELOAD mechanism’)
- [T1071] Application Layer Protocol – Network evasion by resetting proxies and rewriting /etc/resolv.conf to use Cloudflare and Google DNS. (‘Rewrites /etc/resolv.conf, setting Cloudflare and Google DNS and locking it with chattr +i’)
Indicators of Compromise
- [IP Address] Attacker origin – 178.220.112.53 (Serbian IP used to exploit JupyterLab)
- [URL] Image download sites – https://iili.io/FhFK3Eg.jpg, https://k0ske.short.gy/panda_v14, and other shortened URLs hosting polyglot payload images
- [File Hash – MD5] Rootkit and binaries – 63e613cab023c023d74e9dc8e0168e54 (hideproc.so rootkit), 6e9929b127afc5b4351ba3318e2178dc (ccminer), and 305264d95d5056bc5de3a0b683bcd7eb (cpuMinerTermux.koske)
Read more: https://www.aquasec.com/blog/ai-generated-malware-in-panda-image-hides-persistent-linux-threat/