The BlueNoroff attack involved a malicious Zoom extension disguised as a Calendly invite, leading to the download of malware via a fake Zoom domain. Investigations uncovered multiple domains, IP addresses, and email-connected domains linked to the attack, with some domains identified as likely malicious well before the attack was discovered. #BlueNoroff #ZoomExtension #Huntress
Keypoints
- The BlueNoroff attack was triggered by a malicious AppleScript downloaded from a fake Zoom domain disguised as a Calendly invite.
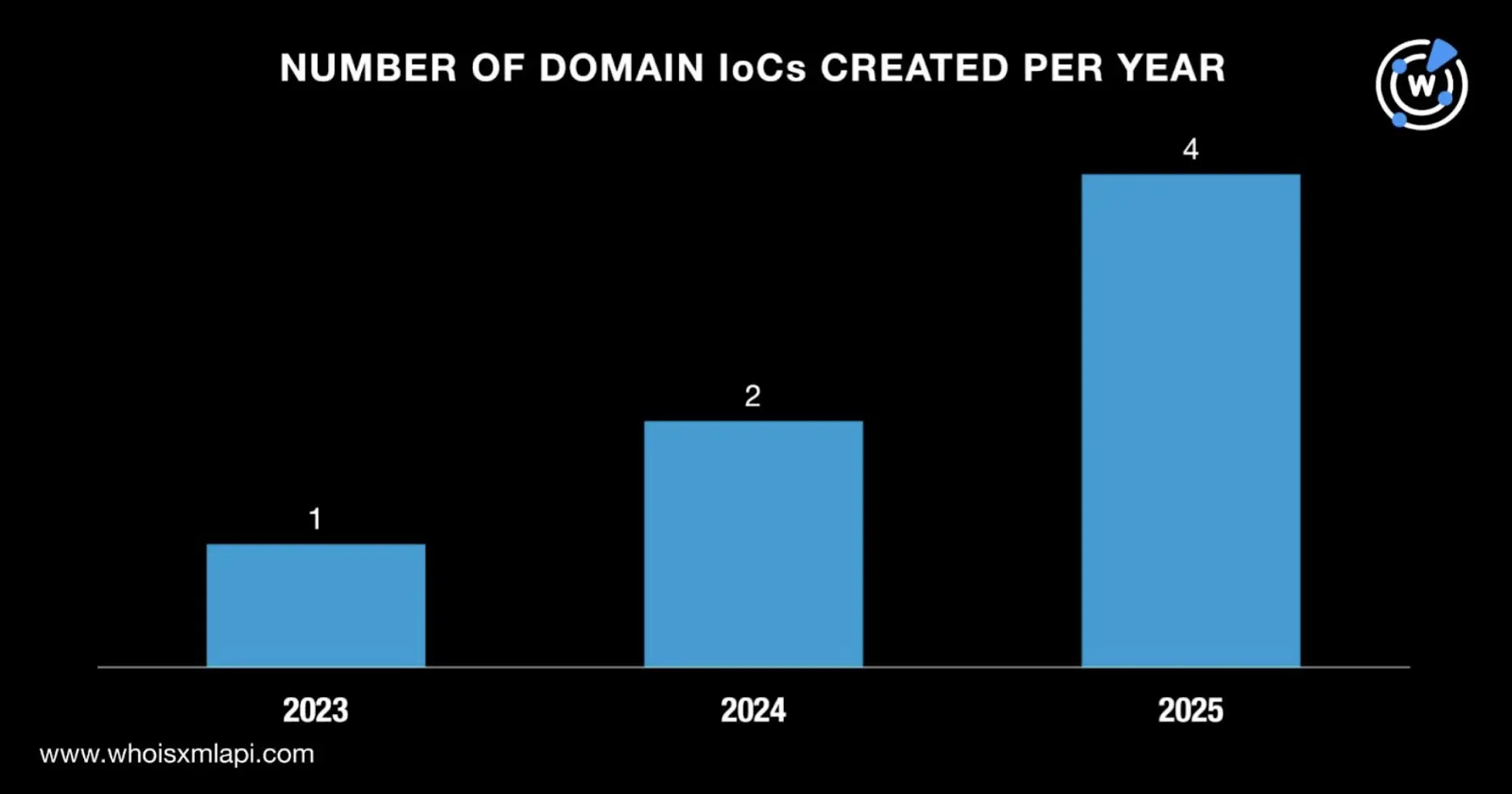
- Seven initial domains were identified as indicators of compromise (IoCs), all registered via Namecheap in Iceland between August 2023 and March 2025.
- Three of these domains were flagged by First Watch as likely to turn malicious 72 to 281 days before the attack date of June 11, 2025.
- Investigation revealed 16 email-connected domains, six malicious IP addresses, and 13 additional IP-connected domains linked to the IoCs.
- All six malicious IP addresses were geolocated in the U.S. and administered by Hostwinds, acting as dedicated hosts.
- The domains exhibited patterns such as including the strings “safe” or “zoom” in their names and using gTLDs like .xyz, .online, and .biz.
- Researchers caution that some entities identified as malicious may require additional investigation for confirmation.
MITRE Techniques
- [T1204] User Execution – The attack relied on user interaction to click a link from a fake invite that downloaded a malicious AppleScript (“that triggered the download of a malicious AppleScript…”).
- [T1587] Develop Capabilities – The attackers registered and used newly created domains and IP addresses to host the malicious payloads (“They were created between 2 August 2023 and 31 March 2025…”).
- [T1071] Application Layer Protocol – The threat actor used Telegram to send the malicious Calendly invite disguised message (“…sent via Telegram…”).
- [T1566] Phishing – The attack employed a social engineering technique by disguising the malware as a Calendly meeting invite and fake Zoom domain (“…malware came disguised as a Calendly meeting invite… instead of a Google Meet page… user ended up on a threat actor-controlled fake Zoom domain…”).
Indicators of Compromise
- [Domain] Initial and connected domains related to BlueNoroff attack – firstfromsep.online, readysafe.xyz, safeupload.online, us05web-zoom.biz, and 16 email-connected domains.
- [IP Address] Malicious IPs used in the attack hosted by Hostwinds in the U.S. – 104.168.136.231, 142.11.196.220, 192.119.116.231, and 3 more IPs.
- [URL] Initial URL indicators involving fake Zoom domains and suspicious URLs tied to the extension download (specific URLs not listed but included in the investigation).
Read more: https://circleid.com/posts/beneath-the-belly-of-the-latest-bluenoroff-attack-a-dns-investigation