BloodHound OpenGraph simplifies adding nodes and edges but requires a well-designed attack graph model for effective functionality. The article explains attack graph design principles, including graph components, edge directionality, node identifiers, and complex examples like ADCS and Golden Certificate attacks. #BloodHoundOpenGraph #AttackGraphModel #ADCS #GoldenCertificate
Keypoints
- BloodHound OpenGraph provides an easy-to-use interface for adding nodes and edges but does not create the data model for users.
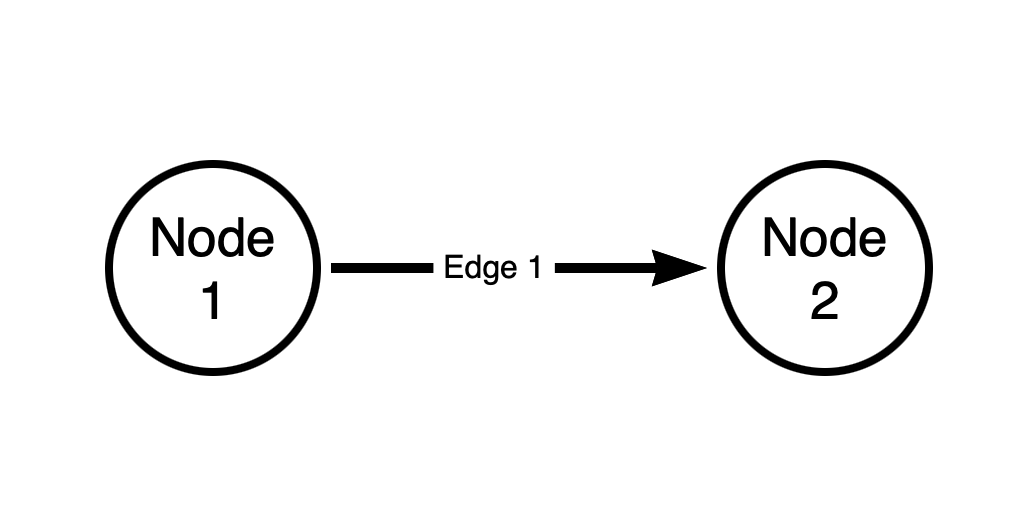
- Attack graphs consist of vertices (nodes) and edges (relationships); all BloodHound edges are directed and serve to reveal attack paths.
- Proper attack graph models require universally unique node identifiers such as SIDs or GUIDs and distinct node and edge classes.
- Connectedness in a graph is essential to discover attack paths by linking non-adjacent nodes through paths.
- Modeling authorization systems like discretionary access control and role-based access control involves representing permissions and scopes via traversable and non-traversable edges.
- ADCS attack paths such as ESC1 are complex and modeled using multiple node types, post-processing edges, and assumptions based on accessible LDAP data.
- The Golden Certificate attack path models the host computer of the ADCS service to connect the private certificate compromise to domain control.
Read more: https://specterops.io/blog/2025/08/01/attack-graph-model-design-requirements-and-examples/