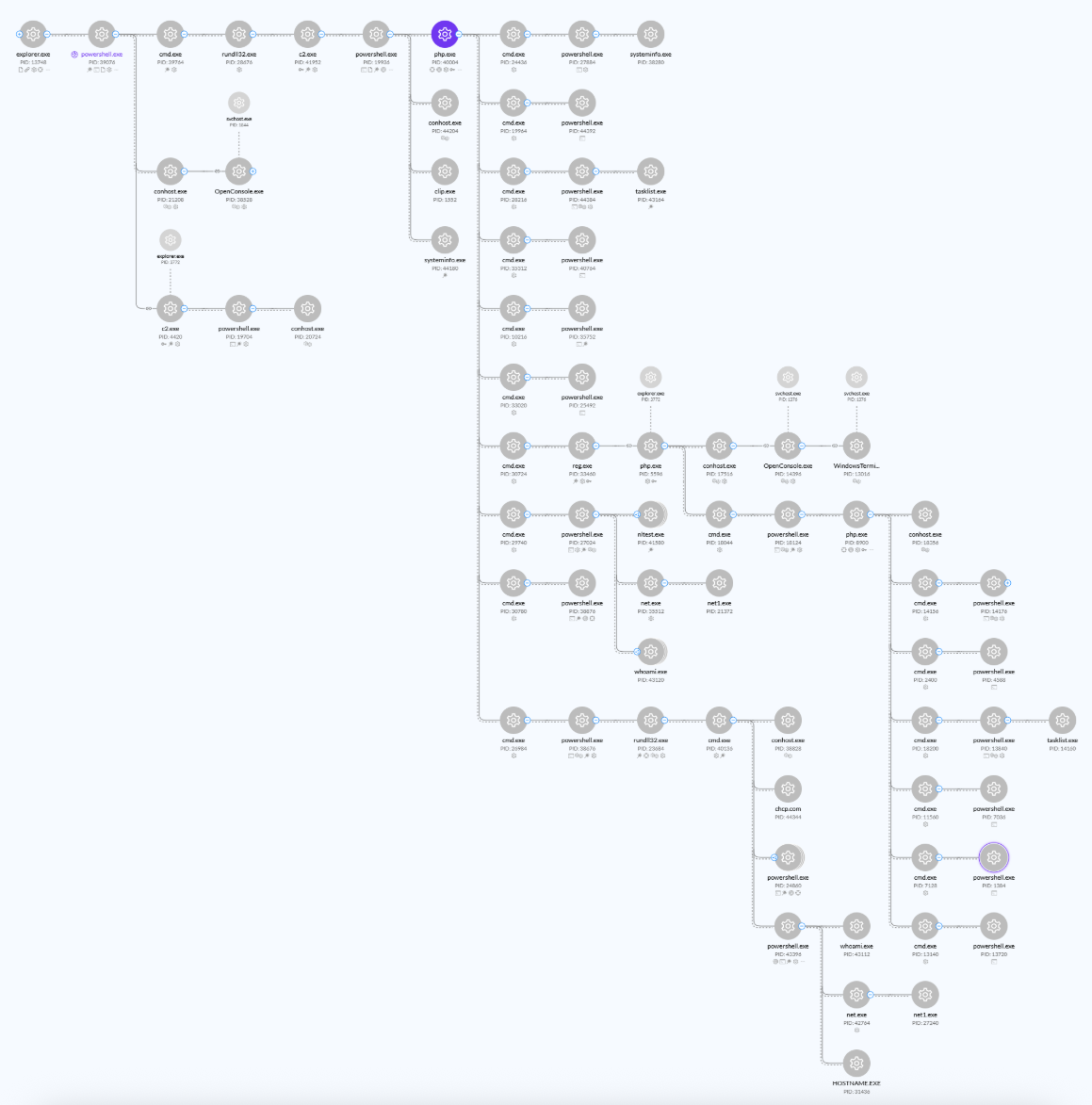
The eSentire Threat Response Unit (TRU) uncovered a sophisticated multi-stage attack by the Interlock Group ransomware gang using PHP backdoors, PowerShell, and LOLBins for system reconnaissance and payload deployment. They provided detailed analysis, Python scripts for detection, and guidance to enhance threat hunting and incident response efforts. #InterlockGroup #InterlockRAT #ClickFix
Keypoints
- The Interlock Group ransomware gang has targeted organizations across North America and Europe since September 2024 using complex multi-stage attacks involving social engineering and compromised websites.
- Initial access was achieved via compromised Kongtuke sites redirecting victims to ClickFix social engineering pages that execute malicious PowerShell commands.
- The attackers deployed a highly obfuscated PHP backdoor (“config.cfg”) that supports multiple commands for persistence, reconnaissance, downloading payloads like Interlock RAT and NodeSnake, and data exfiltration.
- Interlock RAT uses DLL files disguised as PNGs, communicates over TCP port 443, and employs XOR-based encryption for communication with multiple hardcoded C2 servers and backup servers stored on disk.
- The attack chain leverages LOLBins such as rundll32.exe with ShellExec_RunDLL for executing malicious shortcuts and payloads, enabling stealthy command execution and persistence.
- The backdoor supports reverse shell capabilities, self-deletion via embedded DLLs, and maintains persistence through Windows registry autorun keys and startup folder shortcuts.
- eSentire provided Python scripts for decrypting C2 communications and simulating Interlock backdoor activity, as well as a Yara rule to detect the Interlock Backdoor in memory.
MITRE Techniques
- [T1059.001] PowerShell – Used to execute obfuscated commands for downloading further stages and executing backdoors (‘”$gt=’dng-m,i,crosoftds,com’.Split(‘,’);… iex $sc”‘).
- [T1105] Ingress Tool Transfer – Backdoor downloads additional components such as PHP backdoor and NodeJS payloads from C2 infrastructure (‘Download NodeJS and JavaScript payload’).
- [T1543.003] Windows Service – Persistence via Windows shortcut in startup folder pointing to c2.exe and registry autorun keys (‘Set up persistence via registry “Run” key’).
- [T1204.002] User Execution: Malicious File – Victims are socially engineered to run malicious PowerShell commands via ClickFix and compromised websites (‘redirected and social engineered to run a malicious PowerShell command via ClickFix’).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Used by backdoor to establish persistence (‘Creates Windows shortcut in startup folder for persistence’).
- [T1569.002] System Services: Service Execution – Backdoor utilizes rundll32.exe to load malicious DLLs (‘rundll32.exe “.png”, start’).
- [T1053.005] Scheduled Task/Job: Scheduled Task – Indirectly implied for persistence and execution scheduling within the attack chain.
- [T1027] Obfuscated Files or Information – Use of obfuscated PHP backdoor and Powershell commands (‘config.cfg is highly obfuscated PHP-based backdoor’).
- [T1041] Exfiltration Over C2 Channel – Data exfiltration using encoded base64 files staged in public directories (‘Victim files harvested by encoding sensitive files in base64… C:UsersPublic’).
- [T1071] Application Layer Protocol: Web Protocols – C2 communication over HTTP/HTTPS and TCP 443 (‘C2 communication in the backdoor is facilitated over sockets – TCP port 443’).
- [T1574.001] Hijack Execution Flow: DLL Search Order Hijacking – Use of self-injection and packed DLL backdoor employing tail jump to entry point (‘backdoor is packed, and uses self-injection to overwrite itself’).
- [T1056] Input Capture – Clipboard manipulation to inject obfuscated commands (‘an example obfuscated command copied to a victim’s clipboard’).
Indicators of Compromise
- [Domain] Malicious C2 and download domains – dng-microsoftds[.]com, dnsg-microsoftds-data[.]life
- [File Hashes] Obfuscated backdoor and payload files – config.cfg (PHP backdoor), c2.exe (Simple Process Launcher), several random 8-char named executables and PNG DLL files
- [IP Addresses] Hardcoded C2 Servers in C backdoor – 167.235.235[.]151, 128.140.120[.]188, 177.136.225[.]135, and backup servers 206.72.199[.]225, 65.109.162[.]8
- [File Names] Staged exfiltration files – C:UsersPublic*.log
- [Commands] Malicious PowerShell commands and rundll32 execution lines – e.g. rundll32 shell32.dll,ShellExec_RunDLL “.lnk” and rundll32.exe “.png”, start
Read more: https://www.esentire.com/blog/unmasking-interlock-groups-evolving-malware-arsenal