Microsoft Threat Intelligence revealed that the Russian state actor Secret Blizzard is conducting a cyberespionage campaign using an adversary-in-the-middle (AiTM) position at ISPs in Moscow to deploy ApolloShadow malware targeting foreign embassies. The malware installs root certificates to intercept encrypted traffic, allowing persistent access for intelligence gathering. #SecretBlizzard #ApolloShadow
Keypoints
- Secret Blizzard, linked to the Russian Federal Security Service, operates an AiTM campaign at ISP level targeting foreign embassies in Moscow since at least 2024.
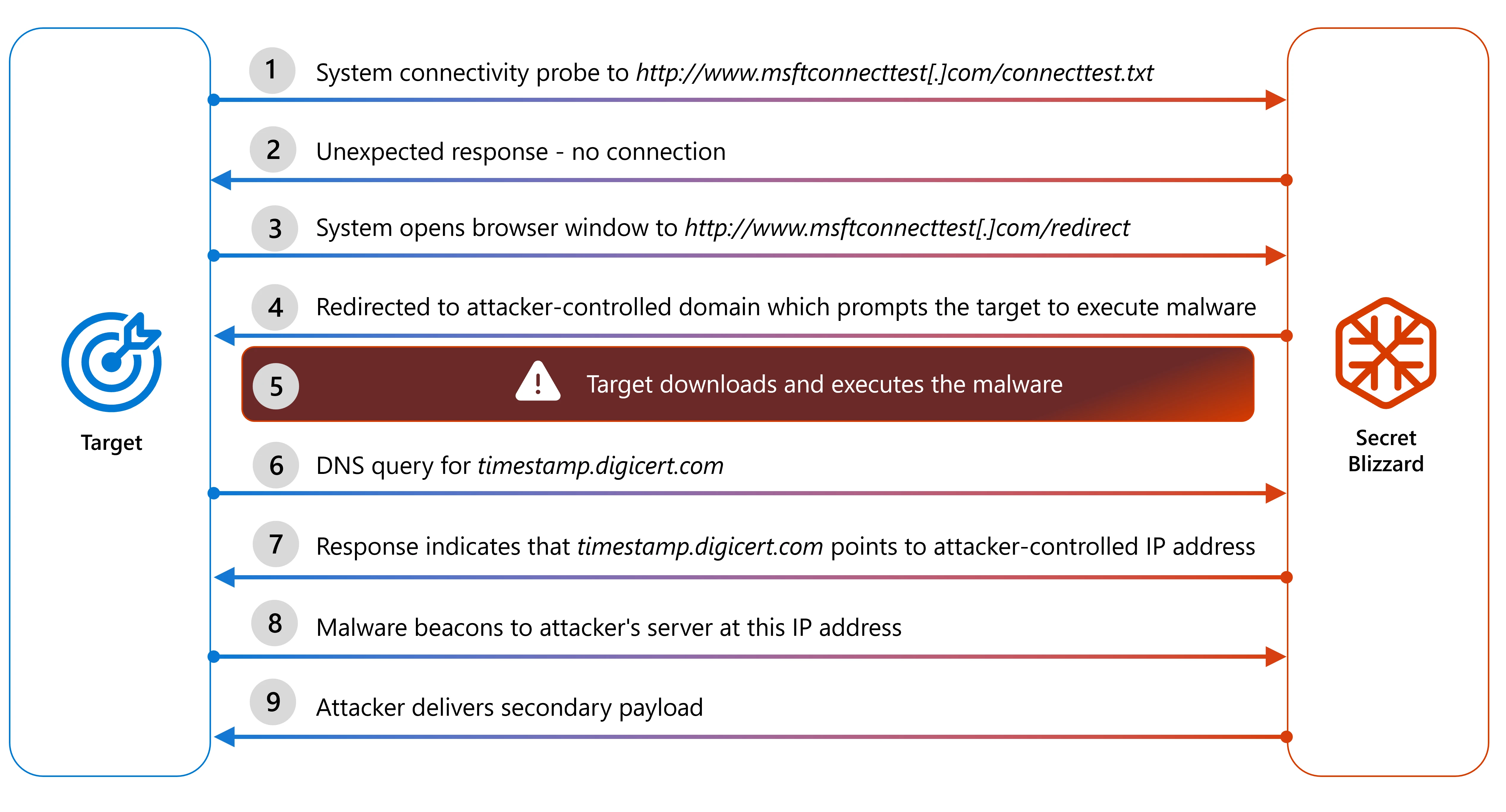
- The actor deploys ApolloShadow malware via captive portal redirection, tricking users into installing malicious root certificates masked as Kaspersky AV installers.
- ApolloShadow operates in low and elevated privilege modes, collects network information, modifies firewall and network profile settings, and creates persistent local administrator accounts.
- The malware uses DNS manipulation and string obfuscation techniques to evade detection and maintain control over victim systems.
- Microsoft recommends encrypted tunnels, use of VPNs outside Russian control, least privilege policies, multifactor authentication, and enabling Microsoft Defender protections to mitigate the threat.
- Several Microsoft Defender and Security Copilot detection capabilities and hunting queries are available to identify and respond to related activity.
- Indicators of compromise include the domain kav-certificates.info, IP 45.61.149.109, ApolloShadow file hashes, and the certificate installer file name CertificateDB.exe.
MITRE Techniques
- [T1557] Adversary-in-the-Middle – Secret Blizzard positions themselves at the ISP level to intercept and manipulate network traffic (“Adversary-in-the-middle (AiTM) position”).
- [T1204] User Execution – The malware prompts users to install root certificates through a UAC pop-up masquerading as Kaspersky installer (“displays the user access control (UAC) pop-up window… masquerades as a Kaspersky installer”).
- [T1036] Masquerading – ApolloShadow uses a file named CertificateDB.exe to disguise malicious activity as legitimate software (“masquerades as a Kaspersky installer”).
- [T1071] Application Layer Protocol – The malware uses HTTP GET requests with encoded query parameters to communicate with command and control servers (“GET request with the destination URL hxxp://timestamp.digicert[.]com/registered”).
- [T1110] Brute Force / Account Manipulation – Creates a local administrator account “UpdatusUser” with a hardcoded password and sets it to never expire (“create an administrative user … with the username UpdatusUser and a hardcoded password”).
- [T1070] Indicator Removal on Host – Malware deletes temporary certificate files after installation using certutil (“temporary files are deleted following the execution of the commands”).
- [T1083] File and Directory Discovery – Collects host IP address information using system APIs to exfiltrate to C2 (“host’s IP information is collected using the API GetIpAddrTable”).
- [T1562] Impair Defenses – Alters network profiles to Private and modifies firewall rules to enable network discovery and file sharing (“ApolloShadow alters the host by setting all networks to Private” and “turn on network discovery”).
Indicators of Compromise
- [Domain] Actor-controlled domain used for malware download – kav-certificates.info
- [IP Address] Command and control infrastructure – 45.61.149.109
- [File Hash] ApolloShadow malware sample – 13fafb1ae2d5de024e68f2e2fc820bc79ef0690c40dbfd70246bcc394c52ea20
- [File Name] Certificate installer associated with malware – CertificateDB.exe