North Korea operates a covert cyber-espionage scheme by embedding operatives as remote IT workers in U.S. and international tech firms using stolen identities, laundering the illicitly earned salaries through a complex global network. This operation, orchestrated by the Reconnaissance General Bureau, leverages shell companies, fake domains, and cryptocurrency to funnel millions into DPRK’s economy while gaining access to critical infrastructure and intellectual property. #ReconnaissanceGeneralBureau #KejiaWang #JoshuaPalmer #HopanaTechLLC
Keypoints
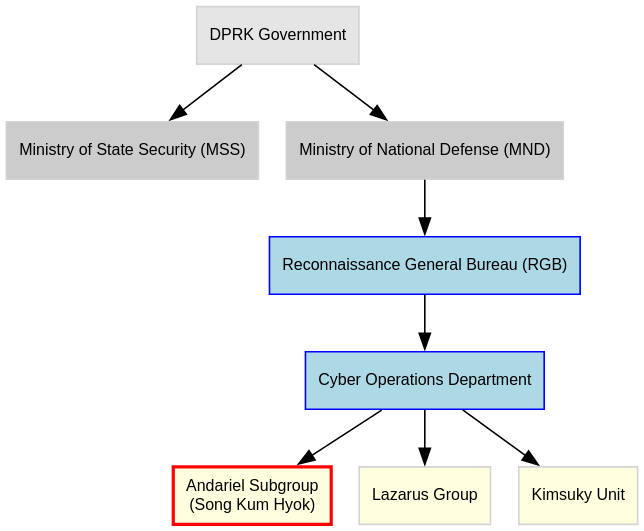
- North Korea’s Reconnaissance General Bureau directs a global scheme employing operatives posing as remote IT workers using forged or stolen U.S. identities.
- Operatives gain access to internal corporate systems including GitHub repositories, Slack channels, CI/CD pipelines, and cloud infrastructure, enabling espionage and intellectual property theft.
- Kejia Wang, operating from New Jersey, coordinated a laundering network through multiple shell companies like Hopana-Tech LLC and Tony WKJ LLC, facilitating salary payments and device handling.
- Payments to DPRK operatives are laundered using cryptocurrency wallets, smart contracts for fund fragmentation, and over-the-counter brokers across Russia, UAE, China, and Hong Kong.
- The operation utilizes stolen identities and AI-generated profiles to infiltrate freelancing platforms worldwide, expanding to less-regulated gig platforms in the MENA region.
- Several fake identities, such as “Joshua Palmer” and “devmad119,” are linked to cryptocurrency wallets and laundering flows supporting DPRK’s economic espionage.
- Corporate failures in asset management and vetting processes allowed this insider threat to embed, highlighting the need for zero-trust security and stringent identity verification.
MITRE Techniques
- [T1078] Valid Accounts – DPRK operatives used stolen and forged U.S. identities to gain legitimate remote employment providing persistent access to internal systems (‘stolen and curated identities—complete with names like Joshua Palmer, Sandy Nguyen…’).
- [T1098] Account Manipulation – Creation and use of synthetic profiles, resumes, and identity documents to bypass hiring and platform verification (‘Operatives use these identity packages to craft professional-grade resumes and LinkedIn profiles, frequently enhanced with AI-generated content’).
- [T1021] Remote Services – Use of KVM switches and remote desktop setups to operate laptops physically located in the U.S. but controlled by DPRK operatives abroad (‘He physically received laptops… and connected them to internet-facing KVM switches’).
- [T1113] Screen Capture – Implantation of backdoors and monitoring tools allowing DPRK actors to surveil company operations (‘installed unauthorized software, managed credentials, and monitored access on behalf of the regime’).
- [T1003] Credential Dumping – Theft of Social Security numbers, KYC data, and Green Card scans for identity fabrication and employment fraud (‘These identities often include verified Know Your Customer (KYC) data: Social Security numbers, clean background checks…’).
- [T1082] System Information Discovery – Access to cloud configurations and CI/CD pipelines to understand and exploit target environments (‘Once embedded, they gain access… financial dashboards, CI/CD pipelines, and privileged cloud infrastructure’).
- [T1486] Data Encrypted for Impact – Use of cryptocurrency smart contracts to fragment and obfuscate salary funds (‘Smart contracts were employed to automatically split the incoming funds…’).
- [T1091] Replication Through Removable Media – Handling and distribution of company laptops to operatives via intermediaries (‘He physically received laptops sent by U.S. companies hiring remote workers and connected them to internet-facing KVM switches’).
Indicators of Compromise
- [File Hash] Cryptocurrency wallet addresses – Examples include Ethereum wallet addresses linked to aliases such as bbshark[.]eth, gsofter[.]eth used for salary laundering flows.
- [Domain] Shell company domains – hopanatech[.]com, tonywangtech.com, wkjllc[.]com, and inditechlab[.]com used for laundering and employer deception.
- [IP Address/Location] Physical addresses – 65 Idlewild Road, Edison, NJ linked to Kejia Wang’s shell companies and laundering operations; 12607 W Vista Paseo Dr, Litchfield Park, AZ linked to laptop farm facilitator Christina Chapman.
- [Alias] Fake identities – Joshua Palmer, devmad119, Sandy Nguyen, Andy Bell, Benjamin Nguyen, Muhammad Abdullah used for employment fraud and linked GitHub handles.
- [Organization Name] Shell companies – Hopana-Tech LLC, Tony WKJ LLC, Independent Lab LLC, Highland Park 215 Spa LLC used for processing payments and laundering funds.