SentinelLABS uncovered over 10 patents for advanced forensic and data collection tools linked to companies associated with the Hafnium threat actor group, revealing new offensive capabilities including encrypted data acquisition and mobile forensics. The research highlights complex relationships between indicted hackers, their affiliated companies, and Chinese government entities conducting cyber operations. #Hafnium #ShanghaiFiretech
Keypoints
- SentinelLABS identified previously unreported offensive tooling patented by companies linked to Hafnium, including software for remote data recovery from Apple devices.
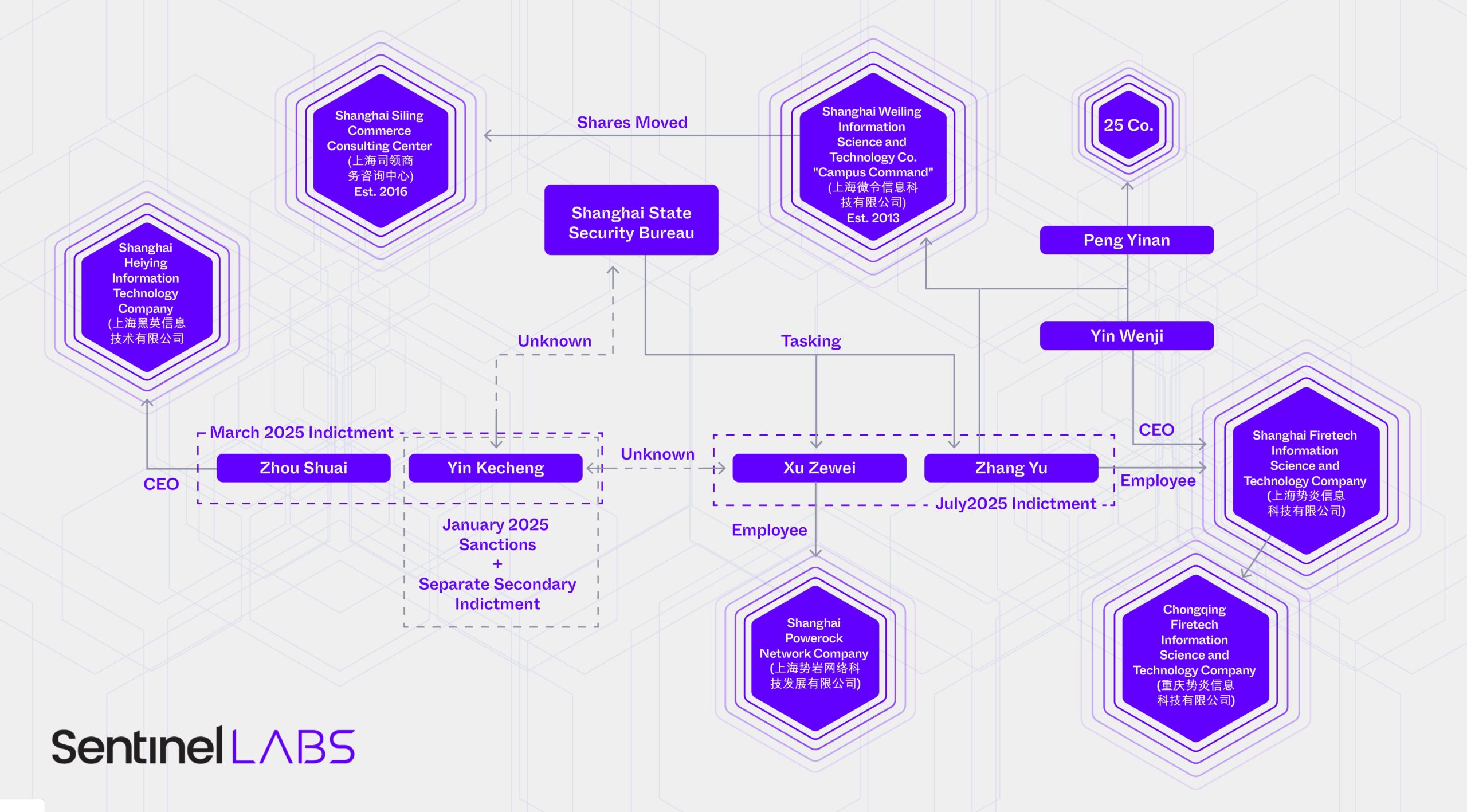
- The U.S. Department of Justice indicted multiple hackers including Xu Zewei and Zhang Yu for working under the direction of Chinese government agencies such as the Shanghai State Security Bureau (SSSB).
- Hafnium’s association with multiple companies forms a tiered contracting ecosystem supporting China’s Ministry of State Security (MSS) offensive cyber operations.
- Exploitations of Microsoft Exchange Server vulnerabilities by Hafnium triggered unprecedented international condemnation and influenced China’s cyber policy and propaganda strategies.
- Shanghai Firetech holds patents for various offensive cyber tools beyond publicly known Hafnium tradecraft, including intelligent home appliance analysis and mobile forensic software.
- The complexity of attribution is increased by the overlapping activities of individuals, multiple companies, and government bureaus within China’s offensive cyber ecosystem.
- Leaked internal communications and indictments reveal a layered structure of contractors, with firms like iSoon and Chengdu404 occupying different tiers under MSS direction.
MITRE Techniques
- [T1213] Data from Information Repositories – Usage of patented software to remotely recover files, including from Apple computers (“remote automated evidence collection software”).
- [T1082] System Information Discovery – Collection of evidence and data from network devices and intelligent home appliances as indicated by patents like “router intelligent evidence collection software” and “intelligent home appliances analysis platform”.
- [T1560] Archive Collected Data – Capabilities related to acquiring encrypted endpoint data and decrypting hard drive contents (“specially designed computer hard drive decryption software”).
- [T1059] Command and Scripting Interpreter – Use of remote automated control software for evidence collection suggests command execution on targeted devices.
- [T1071] Application Layer Protocol – Network-based evidence collection and control software (e.g., “long-range household computer network intelligentized control software”) for interfacing over network protocols.
Indicators of Compromise
- [File Hashes] Associated with toolkits and malware used by Hafnium-linked companies – examples include hashes referenced in DOJ indictments (specific hashes not publicly disclosed).
- [Company Names] Entities connected to Hafnium operations – Shanghai Firetech Information Science and Technology Company, Shanghai Powerock Network Company, iSoon, Chengdu404.
- [Individual Names] Indicted hackers implicated in Hafnium operations – Xu Zewei, Zhang Yu, Yin Kecheng, Zhou Shuai.
- [Vulnerabilities] Microsoft Exchange Server ProxyLogon vulnerability – exploited by Hafnium and associated groups in 2021.
Read more: https://www.sentinelone.com/labs/chinas-covert-capabilities-silk-spun-from-hafnium/