Threat actors continue to exploit Google Accelerated Mobile Pages (AMP) and Google redirect methods to bypass security defenses, using tactics such as URL path variations, country-specific TLDs, and CAPTCHA challenges. The evolution of these techniques includes double Google redirects and abuse of Google Maps and Google Translate subdomains, making phishing campaigns increasingly effective against Secure Email Gateways (SEGs). #GoogleAMP #GoogleRedirectAbuse
Keypoints
- Google redirect abuse remains a prevalent tactic to mask malicious content and evade Secure Email Gateway detection.
- The volume of Google AMP abuse stayed consistently high throughout 2023 and into 2024, with new variations emerging.
- Threat actors use different Google URL paths and country code TLDs (e.g., .br, .fr, .sg) to obfuscate malicious redirects.
- CAPTCHA challenges are commonly employed in phishing emails using Google AMP redirects to block automated security scans.
- Evolved tactics include double Google redirects, leveraging Google Maps and Google Translate subdomains for additional layers of redirection.
- Google Translate is abused both to redirect users and directly host phishing content, making detection more difficult.
- Phishing campaigns are increasingly shifting from Google AMP to new Google redirect URLs to adapt to security defenses.
MITRE Techniques
- [T1204] User Execution – Threat actors use CAPTCHA challenges in phishing emails to ensure victim interaction and bypass automated security checks (‘usage of CAPTCHA challenges … counted for 63.3% of all phishing emails utilizing a Google AMP redirect URL’).
- [T1090] Proxy – Use of double Google redirects and various Google domains to disguise final destination URLs and evade detection (‘double Google redirect method … allowing both users and SEGs to trust and open dangerous links’).
- [T1110] Brute Force – Abuse of CAPTCHA to prevent automated detection and force manual verification before proceeding (‘CAPTCHA challenges can act as a barrier that can prevent web crawlers from reaching the phishing page due to the manual input that CAPTCHA requires’).
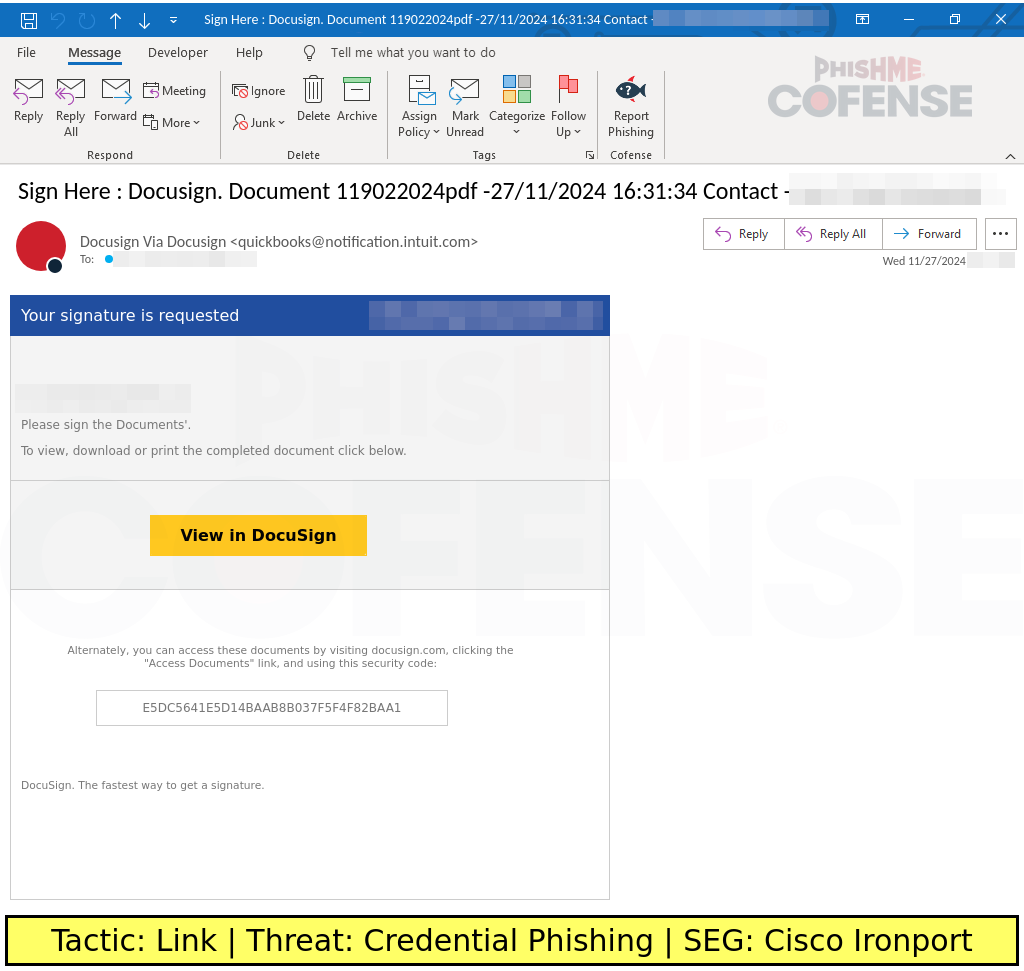
- [T1203] Exploitation for Client Execution – Use of embedded clickable images within HTML emails exploiting Google AMP to deliver phishing payloads (‘image-based phishing emails, which is an HTML image that contains a clickable embedded link’).
- [T1566] Phishing – Overall use of Google AMP and Google redirects in phishing campaigns targeting users with malicious links masked by trusted domains (‘Threat actors utilize Google redirects to mask malicious content from Secure Email Gateway (SEG) detection’).
Indicators of Compromise
- [Domains] Malicious redirect domains abusing Google services – google[.]co[.]za, google[.]fr, google[.]kz, google[.]me, maps[.]google[.]com, translate[.]google[.]com[.]sg
- [URLs] Examples of Google redirect URLs used in phishing – hxxps://google[.]com/amp/s/, hxxps://www.google[.]com/url?sa, hxxps://maps[.]google[.]com/url?q=, hxxps://translate[.]google[.]com[.]sg/translate
- [File Names] Phishing page hosted via Google Translate subdomain – projectile186-sofug-com[.]translate[.]goog
- [Active Threat Report Sample IDs] 384014, 371392, 364875, 382338, 363396 (used in conjunction with corresponding Google AMP TLD variants)
Read more: https://cofense.com/blog/google-redirect-abuse-in-2024-key-trends-tactics