In late 2024, a sophisticated cyberattack targeted Russian IT companies and other international entities using spear phishing and DLL hijacking to deploy Cobalt Strike Beacon malware. Attackers concealed their command and control (C2) communications via profiles on legitimate social media and content-sharing platforms such as GitHub, Microsoft Learn Challenge, and Quora. #CobaltStrike #DLLHijacking #BugSplat #EastWindCampaign
Keypoints
- The cyberattack campaign was active from November 2024 to April 2025, targeting mainly Russian companies but also affecting entities in China, Japan, Malaysia, and Peru.
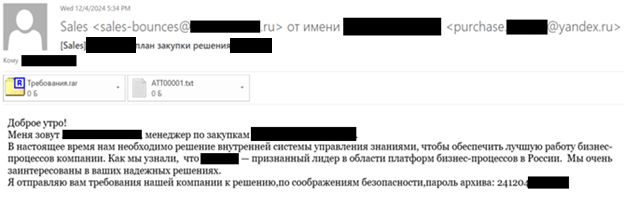
- The initial infection vector was spear phishing emails impersonating major state-owned oil and gas companies, delivering malicious RAR attachments containing decoy PDFs and executables.
- Attackers used DLL Hijacking (T1574.001) by exploiting BugSplat’s Crash reporting Send Utility (BsSndRpt.exe) renamed as nau.exe along with a malicious BugSplatRc64.dll to load malicious code.
- The malicious DLL employed Dynamic API Resolution (T1027.007) with a custom hashing algorithm to obscure API calls, notably hooking MessageBoxW to execute a multi-stage shellcode.
- Payload retrieval involved downloading encrypted payloads hidden within profile pages on legitimate websites such as Microsoft Tech Community, Quora, and GitHub, ensuring stealth and complexity of the execution chain.
- The final payload was a reflective loader injecting Cobalt Strike Beacon into memory, communicating with the C2 server at moeodincovo[.]com.
- The attack shares similarities with the EastWind campaign regarding target profile and use of encrypted C2 URLs hosted on legitimate platforms, suggesting possible attribution links or shared tactics.
MITRE Techniques
- [T1566.001] Spearphishing Attachment – Initial attack vector using spear phishing emails with malicious RAR attachments disguised as legitimate documents.
- [T1574.001] DLL Hijacking – Exploiting BugSplat’s Send Utility by substituting BugSplatRc64.dll with a malicious DLL loaded by the legitimate executable (“The adversary leveraged a common technique: DLL Hijacking … forcing the utility to load it instead of the legitimate file”).
- [T1027.007] Obfuscated Files or Information: Dynamic API Resolution – The malicious DLL obfuscated API functions using a custom hashing algorithm, resolving them dynamically at runtime (“The malicious BugSplatRc64.dll library employs Dynamic API Resolution… functions were obfuscated via a custom hashing algorithm”).
- [T1176] Browser Bookmark Discovery / Social Media Accounts – Using legitimate social media and content-sharing profiles to host encrypted command and control data (“malicious information hidden inside profiles on GitHub, Microsoft Learn Challenge, Q&A websites, and even Russian social media platforms”).
- [T1543.003] Create or Modify System Process: DLL Injection – The shellcode loads Cobalt Strike Beacon reflectively into process memory (“reflective loader that injects Cobalt Strike Beacon into the process memory”).
Indicators of Compromise
- [File Hashes] Malicious and legitimate file samples – LNK file hash: LNK30D11958BFD72FB63751E8F8113A9B0492481228C18C336233D242DA5F73E2D5; Legitimate BugSplat.exe hash: 633F88B60C96F579AF1A71F2D59B4566; and multiple DLL hashes including 2FF63CACF26ADC536CD177017EA7A36908FB7BD0BB1785B67166590AD7F99FD and others.
- [URLs] Malicious C2 and payload download locations – https://moeodincovo[.]com/divide/mail/SUVVJRQO8QRC, https://raw[.]githubusercontent[.]com/Mariew14/kong/master/spec/fixtures/verify-prs, https://techcommunity.microsoft[.]com/users/mariefast14/2631452, https://www[.]quora[.]com/profile/Marieformach, and others utilized to hide encrypted payload data.
Read more: https://securelist.com/cobalt-strike-attacks-using-quora-github-social-media/117085/