A sophisticated WordPress backdoor plugin named “wp-compat” was discovered creating and hiding a persistent administrator account to maintain attacker control. The malware uses multiple evasion techniques including hiding from plugin listings and blocking account edits or deletions. #wp-compat #adminbackup
Keypoints
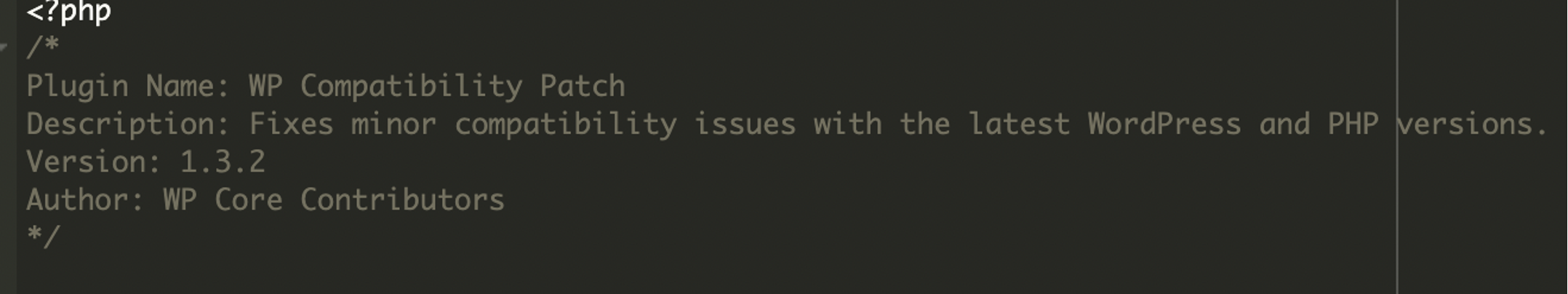
- The malware was found in the WordPress plugins directory as a fake plugin named “wp-compat” claiming to fix compatibility issues.
- It creates a hidden administrator user called “adminbackup” with a suspicious email address and persistently maintains this user.
- The plugin hides the malicious admin user from user listings and modifies admin role counts to avoid detection.
- The malware prevents deletion or editing of the malicious account to maintain persistent access.
- It conceals itself from the WordPress “Plugins” menu and uses a kill switch activated by a specific cookie.
- The backdoor allows attackers full control over the compromised site and can be used to install further payloads or exfiltrate data.
- Recommended remediation steps include removing unused plugins, deleting unknown admin users, changing passwords, deploying a firewall, and updating WordPress and plugins.
MITRE Techniques
- [T1078] Valid Accounts – The malware creates and maintains a persistent administrator account named “adminbackup” to ensure continued access. (‘On every page load, it checks if a user named “adminbackup” exists. If the user doesn’t exist, the code creates them.’)
- [T1566] Phishing – The fake plugin uses legitimate-looking metadata and a plausible name (“WP Compatibility Patch”) to evade superficial security reviews and trick administrators. (‘Because it used a legitimate-looking name and metadata (WP Compatibility Patch), it could easily evade detection during a superficial plugin review.’)
- [T1547] Boot or Logon Autostart Execution – The plugin maintains persistence by automatically recreating the admin user and hiding itself on page loads. (‘On every page load, it checks if a user named “adminbackup” exists… It hides itself so that even though the plugin is active, it doesn’t show up under the “Plugins” menu.’)
- [T1564] Hide Artifacts – The malware hides the malicious admin user from user listings and modifies admin role counts to conceal its presence. (‘It filters out the malicious admin from user listings in the admin dashboard. Then it modifies the user role counts to make the hidden user less obvious.’)
- [T1565] Data Manipulation – It blocks edits and deletion attempts on the malicious user to maintain stealth and persistence. (‘The malware prevents the malicious account from being deleted or edited and kills any attempt to delete the user from the admin panel.’)
Indicators of Compromise
- [File/Folder Names] Fake plugin folder detection – wp-compat
- [Usernames] Suspicious administrator user – adminbackup
- [Email Addresses] Associated with malicious user – [email protected]
- [Database Options] Malicious option stored – _pre_user_id
Read more: https://blog.sucuri.net/2025/07/unauthorized-admin-user-created-via-disguised-wordpress-plugin.html