The recent campaign involving the VIP keylogger malware uses spear-phishing emails with malicious ZIP attachments and an AutoIt-based injector to deploy the payload. This malware performs keystroke logging, credential theft from major web browsers, and ensures persistence through a VBScript. #VIPKeylogger #AutoIt #RegSvcsInjection
Keypoints
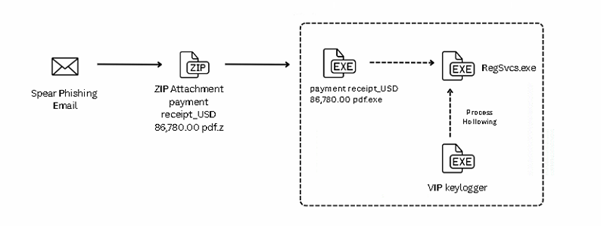
- The campaign delivers VIP keylogger via spear-phishing emails containing a ZIP file with a malicious executable disguised as a payment receipt.
- The executable runs an embedded AutoIt script that decrypts and loads the payload in memory, leveraging custom XOR decryption functions.
- Two encrypted files, leucoryx and aveness, are dropped into the Temp directory and decrypted at runtime.
- The final payload is injected into RegSvcs.exe using process hollowing, enabling stealthy execution.
- A VBScript dropped in the Startup folder ensures persistence by launching the payload on user login from the AppDataLocal directory.
- The VIP keylogger captures keystrokes, steals credentials from browsers like Chrome, MS Edge, and Mozilla, and monitors clipboard activity.
- Indicators of compromise include specific MD5 hashes, malicious filenames, and a command and control IP address.
MITRE Techniques
- [T1027] Obfuscated Files or Information – The malware uses AutoIt scripts and custom XOR functions for decrypting payload data, evading detection (‘…decrypts it using a custom XOR function…’).
- [T1204.002] User Execution: Malicious File – The infection starts with user execution of a malicious executable disguised as a PDF (‘…executable disguised as “payment receipt_USD 86,780.00 pdf.exe”’).
- [T1059.006] Command and Scripting Interpreter: Python – AutoIt script runs to decrypt and execute payload in memory (‘…the embedded AutoIt script runs…’).
- [T1113] Screen Capture – VIP keylogger collects information including keystrokes and clipboard data (implied by monitoring clipboard activity).
- [T1592] Gather Victim Host Information – The malware collects system information as part of its data theft functions.
- [T1056] Input Capture – The VIP keylogger records keystrokes and credentials from multiple browsers (‘…logging keystrokes, capturing credentials from…’).
- [T1055.002] Process Injection: Portable Executable Injection – The malware injects decrypted payload into RegSvcs.exe via process hollowing (‘…inject the final payload VIP keylogger into RegSvcs.exe’).
- [T1659] Content Injection – Injecting malicious code into a legitimate process to evade defenses (‘…decrypted payload is mapped into the address space of regsvc.exe’).
- [T1071.001] Application Layer Protocol: Web Protocols – Exfiltration of captured data likely uses SMTP and web protocols (‘Exfiltrate data through SMTP…Exfiltrate data to c2’).
Indicators of Compromise
- [MD5 Hash] Malicious payload files – F0AD3189FE9076DDD632D304E6BEE9E8 (payment receipt_USD 86,780.00 pdf.exe), 0B0AE173FABFCE0C5FBA521D71895726 (VIP Keylogger)
- [Filename] Malicious executable and payload – “payment receipt_USD 86,780.00 pdf.exe”, “definitiveness.exe” in AppDataLocalDunlop directory
- [Domain/IP] Command and control server – hxxp://51.38.247.67:8081
Read more: https://www.seqrite.com/blog/spear-phishing-campaign-delivers-vip-keylogger-via-email-attachment/