CISA added CVE-2025-32433 and CVE-2024-42009 to its Known Exploited Vulnerabilities Catalog after APT28 exploited them to breach government webmail servers in Operation RoundPress. ESET and WhoisXML API uncovered numerous related domains and IPs, revealing extensive malicious infrastructure tied to this campaign. #APT28 #RoundPress #CVE202532433 #CVE202442009
Keypoints
- CISA listed vulnerabilities CVE-2025-32433 and CVE-2024-42009 in the KEV Catalog due to exploitation by APT28 targeting government webmail servers.
- ESET researchers identified 19 IoCs related to Operation RoundPress, including 10 domains and 9 IP addresses.
- WhoisXML API discovered 8,222 email-connected domains, 102 IP-connected domains, and multiple malicious IPs and domains linked to these IoCs.
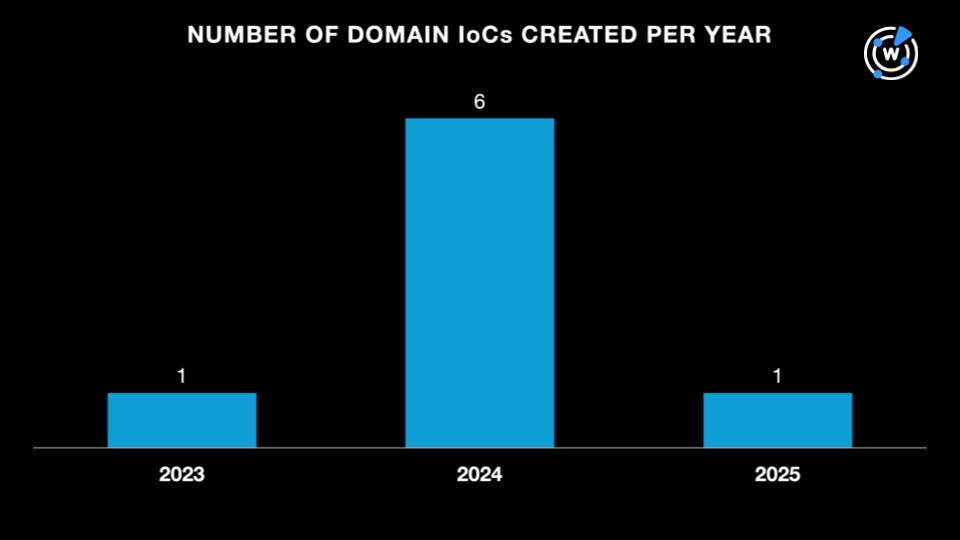
- Most IoC domains were created between 2023 and 2025, with Hosting Concepts as the top registrar.
- IoC IP addresses were geolocated across six countries, with France having the highest count.
- Historical DNS and WHOIS queries uncovered over 350 domain-to-IP resolutions and thousands of connected domains, indicating a broad threat infrastructure.
- The domain lsjb.digital was detected as potentially malicious almost a year before being officially classified as an IoC by ESET.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – APT28 exploited CVE-2025-32433 and CVE-2024-42009 vulnerabilities in government webmail servers (“…they were reportedly abused by APT28 to hack government webmail servers…”).
- [T1598] Phishing for Information – Use of email-connected domains to orchestrate attacks (“…8,222 email-connected domains, seven of which were malicious…”).
- [T1588] Obtain Capabilities – Registration and use of multiple domains and IP addresses for malicious infrastructure (“…identified 19 indicators of compromise… 10 domains and nine IP addresses related to Operation RoundPress.”).
Indicators of Compromise
- [Domains] Operation RoundPress-related IoCs – hfuu.de, lsjb.digital, rnl.world, and 7 more domains identified as malicious or connected to the operation.
- [IP Addresses] Malicious IPs geolocated in Europe and Asia – examples include IPs located in France, the U.K., and Malaysia related to the operation.
- [Email Addresses] Historical WHOIS email addresses linked to IoC domains – five unique emails uncovered that connect to thousands of related domains.
Read more: https://circleid.com/posts/rounding-up-dns-facts-about-operation-roundpress