A compromised NPM package, eslint-config-prettier, was used to distribute the Scavenger Loader malware, which includes sophisticated anti-analysis features and delivers stealer payloads. The loader communicates with a hard-coded C2 infrastructure to download and execute additional modules, including theft of npmrc files that could lead to further compromise. #ScavengerLoader #eslint-config-prettier #SupplyChainAttack
Keypoints
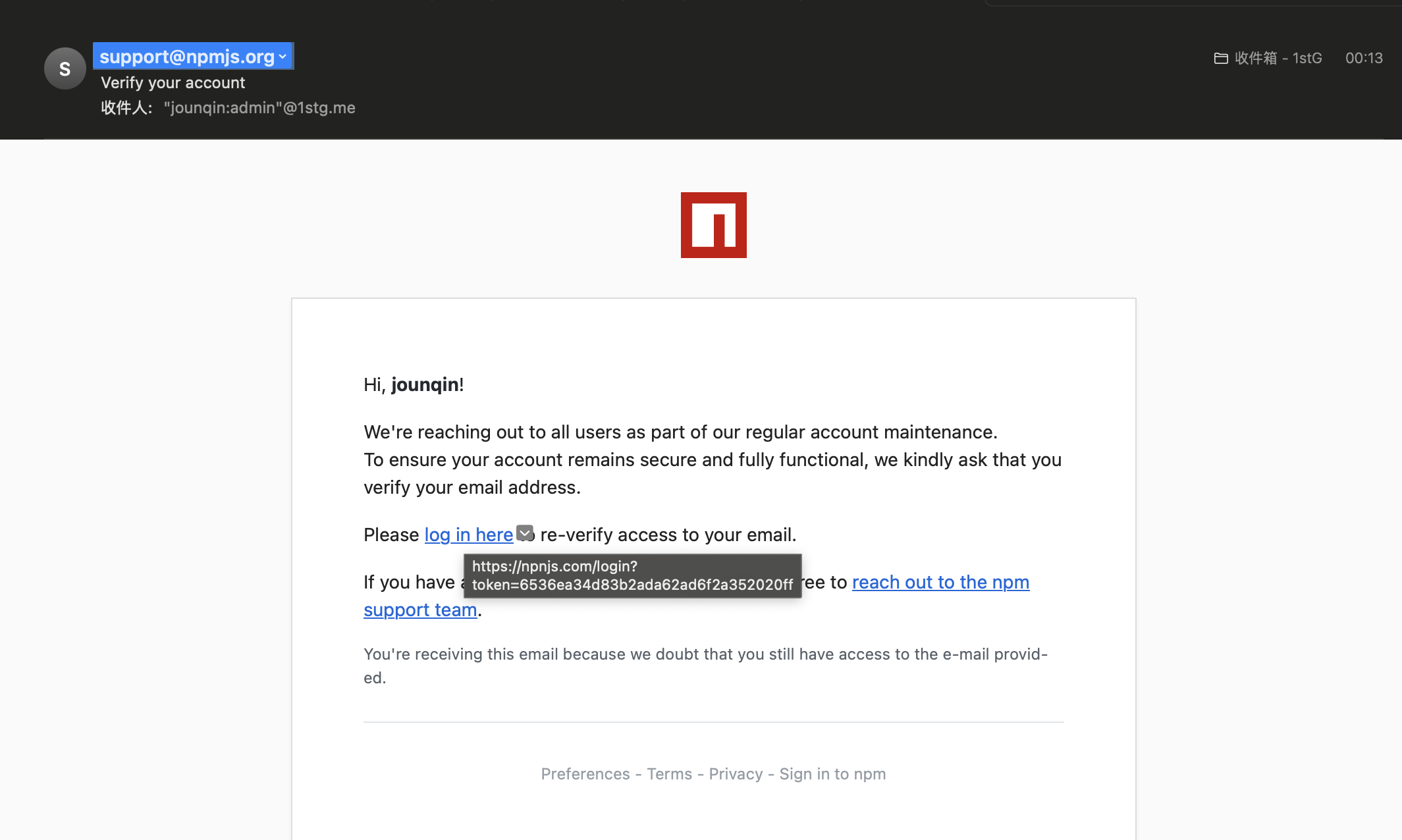
- The NPM package eslint-config-prettier was compromised via phishing, affecting multiple versions and other related packages.
- The malicious package executed the Scavenger Loader, a DLL loader with advanced anti-analysis techniques such as anti-VM, antivirus detection, and anti-debugging.
- The loader dynamically resolves required Windows API functions with CRC32 hashing and uses indirect syscalls to evade detection.
- After passing checks, the loader connects to a hard-coded C2 server, performs encrypted communications, and retrieves stealer payload configurations.
- The payloads are DLL modules deployed using XOR encryption for side-loading or execution, designed to steal sensitive data based on system environment.
- The loader also exfiltrates the user’s npmrc file, containing authentication tokens, increasing risk of further system compromise.
- This supply chain attack mirrors similar tactics found in game mod malware campaigns, highlighting evolving threat actor strategies.
MITRE Techniques
- [T1055] Process Injection – The loader uses rundll32.exe to execute the malicious DLL (node-gyp.dll) loaded by the post-install script.
- [T1560] Archive Collected Data – The npmrc file is collected and encoded before exfiltration to the C2.
- [T1027] Obfuscated Files or Information – String literals are XOR encrypted using compile-time XOR string obfuscation to hinder analysis.
- [T1218] Signed Binary Proxy Execution – Uses rundll32.exe to load and execute the DLL loader.
- [T1190] Exploit Public-Facing Application – The supply chain attack vector via compromised npm package used as infection vector.
- [T1046] Network Service Scanning – The loader enumerates environment details and uses HTTP GET requests to communicate with multiple C2 domains.
- [T1071] Application Layer Protocol – Uses HTTPS to communicate with C2 servers using custom encrypted requests and responses.
- [T1497] Virtualization/Sandbox Evasion – Loader checks firmware tables and BIOS strings for signs of VM environments.
- [T1057] Process Discovery – Scans for processes and injected DLLs related to security products to avoid detection.
Indicators of Compromise
- [File Hash] Malicious package versions – eslint-config-prettier 8.10.1, 9.1.1, 10.1.6, 10.1.7; eslint-plugin-prettier 4.2.2, 4.2.3
- [File Names] Loader DLL and modules – node-gyp.dll (loader), version.dll, umpdc.dll, profapi.dll
- [Domain] C2 infrastructure – Multiple HTTPS domains hosting C2 endpoints for command and payload delivery (specific domains listed in linked IOC repository)
- [File Path] Temporary files – Payload modules written to %TEMP% with randomized filenames for execution