Laundry Bear, also known as Void Blizzard, is a Russian state-sponsored APT active since April 2024 targeting NATO countries and Ukraine using spear phishing and credential theft. Using Validin’s advanced pivoting techniques, multiple additional malicious domains and infrastructure linked to Laundry Bear have been uncovered, expanding beyond initial Microsoft-reported indicators. #LaundryBear #VoidBlizzard #Validin
Keypoints
- Laundry Bear (Void Blizzard) is a Russian APT active since April 2024 targeting NATO countries, Ukraine, and NGOs via spear phishing and stolen credentials.
- Initial indicators include spear-phishing domains such as micsrosoftonline[.]com and malicious sender domain ebsumrnit[.]eu.
- Validin’s wildcard DNS and lookalike domain searches uncovered multiple related domains registered with similar patterns, many using Cloudflare and Mailgun services.
- Host response history and HTTP body hash pivots identified numerous additional domains impersonating login portals with JavaScript redirects to Microsoft services.
- Domains such as enticator-secure[.]com and maidservant[.]shop showed continuous malicious activity with phishing themes and redirects.
- Infrastructure pivoting revealed shared IPs (e.g., 104.36.83[.]170, 34.204.123[.]157) and reused self-signed certificates linking multiple domains.
- Many of the discovered domains employed lookalike registrations, use of privacy-preserving emails, and timeframes aligning with public reporting dates.
MITRE Techniques
- [T1566] Phishing – Laundry Bear used spear phishing with lookalike domains such as micsrosoftonline[.]com to gain initial access (“spear phishing with domain typosquats”).
- [T1078] Valid Accounts – The group leveraged stolen credentials or session cookies for initial access (“using stolen credentials or session cookies for initial access”).
- [T1598] Phishing: Spearphishing Link – Use of spear phishing URLs that mimic legitimate services and redirect victims (“JavaScript redirects to Microsoft login pages”).
- [T1583] Acquire Infrastructure – Registration and use of multiple lookalike malicious domains with privacy-protected WHOIS and use of cloud services to support operations (“Registered with onionmail email addresses and Cloudflare name servers”).
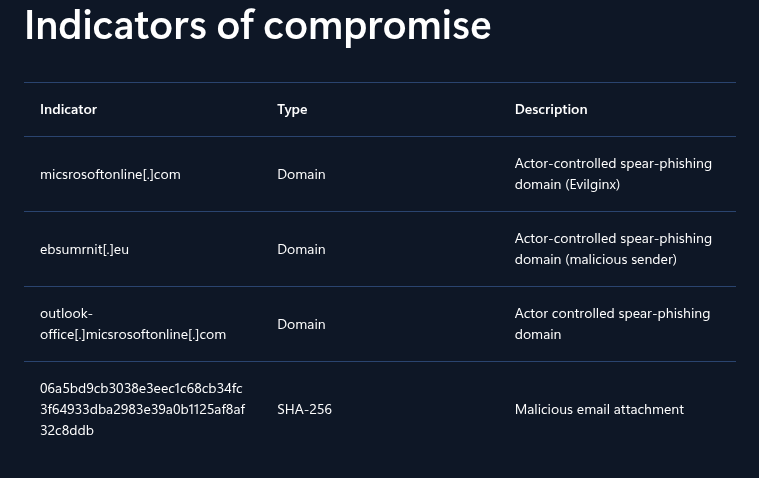
Indicators of Compromise
- [Domain] Spear phishing and malicious sender domains – micsrosoftonline[.]com, ebsumrnit[.]eu, enticator-secure[.]com, maidservant[.]shop, and 20+ related lookalike domains.
- [IP Address] Associated infrastructure IPs – 104.36.83[.]170 (used by multiple domains for phishing), 34.204.123[.]157 (hosting numerous related subdomains), 54.144.139[.]77 (served self-signed certificates linked to domains).
- [Email Address] Registrant contacts for lookalike domains – danhutton@onionmail[.]org, carriehuff@onionmail[.]org, saryman@aficors[.]com.
- [File Hash] HTML body SHA1 hashes indicating phishing redirects – 38c47d338a9c5ab7ccef7413edb7b2112bdfc56f (redirect to outlook.live.com), 2c0fa608bd243fce6f69ece34addf32571e8368f (redirect to login.live.com).
Read more: https://www.validin.com/blog/laundry_bear_infrastructure_analysis/