Homograph attacks exploit visually similar non-Latin characters to evade email security filters and impersonate trusted entities, leading to potential credential theft and malware infection. Three real-world case studies demonstrate how threat actors use homographs in email fields to bypass detection and deliver malicious content. #HomographAttack #PaloAltoNetworks #Unit42
Keypoints
- Homograph attacks use visually similar Unicode characters from different scripts to manipulate email content, making malicious emails appear legitimate to humans but evade automated detection.
- Threat actors employ homographs in email display names, subject lines, and domains to impersonate well-known brands and services, increasing victim trust and engagement.
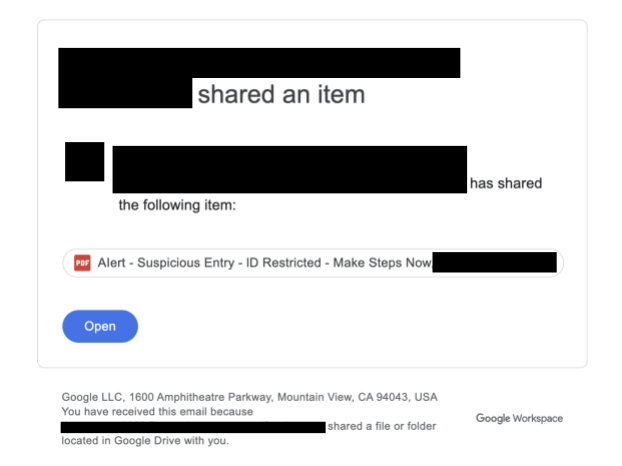
- Three case studies illustrate various uses of homograph attacks: Google Drive file sharing with suspicious links, e-document sharing platforms prompting fraudulent signatures, and Spotify payment update impersonation.
- Malicious links in these emails redirect victims through legitimate-looking domains and multiple redirects to attacker-controlled sites, often protected by bot-filtering CAPTCHAs and personalized targeting.
- Detection of homograph characters relies on analyzing Unicode values since visual inspection alone is insufficient due to their similarity with Latin characters.
- Palo Alto Networks Cortex Advanced Email Security combined with Cortex XSOAR and Cortex XSIAM Digital Risk Protection provides comprehensive detection, quarantine, and mitigation of homograph-based attacks.
- User vigilance, including verifying sender addresses and avoiding engagement with suspicious links or attachments, remains critical to preventing exploitation via homograph attacks.
MITRE Techniques
- [T1566] Phishing – Threat actors used homograph characters in emails to craft convincing phishing messages that impersonate legitimate brands and services (“…homograph characters in display names and subjects to impersonate well-known entities…”).
- [T1586] Compromise Accounts – Attackers abused compromised or spoofed email accounts with homograph manipulations to gain initial access (“…used homograph substitutions in sender addresses to deliver malicious content…”).
- [T1204.002] User Execution: Malicious File – Recipients were encouraged to click links or buttons in phishing emails leading to credential theft or malware delivery (“…VERIFY button redirects to attacker-controlled sites aiming to steal credentials…”).
- [T1090] Proxy – Attackers used legitimate domains like URL shortening services and multiple redirects to mask final malicious destinations (“…used redirects[.]ca URL shortening and redirect chains to attacker domains…”).
Indicators of Compromise
- [Email Addresses] Used to share malicious files or send phishing emails – [email protected][.]com, cfa@agroparistechl[.]fr
- [URLs] Malicious redirect or landing pages – messageconnection.blob.core[.]windows[.]net, bestseoservices[.]com, kig[.]skyvaulyt[.]ru
- [Domains] Impersonation or command and control infrastructure – ha01s003[.]org-dns[.]com, approaches.it[.]com
- [File Path] Used in phishing payload – guvenbisiklet[.]com/wp-content/bin/Verify/Code/index.htm
Read more: https://unit42.paloaltonetworks.com/homograph-attacks/