The UNG0901 threat actor targeted the Russian aerospace industry using spear-phishing emails delivering a malicious EAGLET DLL implant disguised as logistics consignment documents. The implant enables remote command execution, data exfiltration, and uses a decoy XLS file linked to a sanctioned Russian entity for evasion. #EAGLET #UNG0901 #VoronezhAircraftProductionAssociation #HeadMare
Keypoints
- UNG0901 targeted Voronezh Aircraft Production Association (VASO) employees via spear-phishing emails impersonating logistics centers with malicious DLL implants disguised as ZIP files.
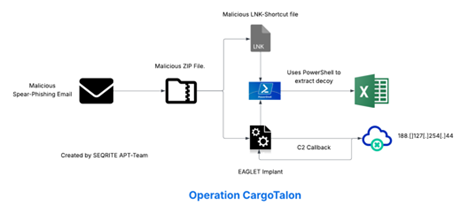
- The infection chain involves a malicious email (.EML), a shortcut (.LNK) file executing the DLL implant, and a decoy XLS file simulating Russian logistics inspection documents.
- The EAGLET implant enumerates system information, generates unique GUIDs, connects to a command-and-control server (185.225.17.104), and supports shell command execution, file download, and data exfiltration.
- Infrastructure analysis links the campaign to known threat clusters, sharing similarities with the Head Mare group targeting Russian governmental and non-governmental entities.
- Multiple campaigns using similar EAGLET implants targeted Russian military recruitment and aerospace sectors, showing overlapping tactics and tooling with Head Mare.
- The decoy XLS file references Obltransterminal LLC, a sanctioned Russian military-logistics entity, aiding defense evasion through realistic document simulation.
- The campaign employs advanced evasion techniques using masquerading files and PowerShell scripts to locate and execute implants from multiple fallback directories.
MITRE Techniques
- [T1566.001] Spearphishing Attachment – Malicious .EML file was sent to a VASO employee impersonating a logistics center delivering a TTN document. (‘Malicious .EML file sent to VASO employee, impersonating a logistics center with TTN document lure.’)
- [T1218.011] System Binary Proxy Execution: Rundll32 – The DLL implant was executed via trusted rundll32.exe called from a malicious .LNK file. (‘DLL implant executed via trusted rundll32.exe LOLBIN, called from the .LNK file.’)
- [T1059.001] PowerShell – Used to locate and launch the DLL implant from fallback directories invisibly. (‘Uses powershell.exe binary to run background scripts to locate and execute DLL implant.’)
- [T1036] Masquerading – DLL implant masquerades as a ZIP file and uses a decoy XLS file imitating sanctioned logistics paperwork. (‘Implant disguised as ZIP, decoy XLS used to simulate sanctioned logistics paperwork.’)
- [T1082] System Information Discovery – Enumerates hostname, computer name, and domain, and generates a unique GUID for victim identification. (‘Gathers hostname, computer name, domain; creates victim GUID to identify target.’)
- [T1482] Domain Trust Discovery – The implant enumerates the victim’s DNS domain for network profiling. (‘Enumerates victim’s DNS domain for network profiling.’)
- [T1071.001] Application Layer Protocol: HTTP – Communicates with C2 via HTTP using a disguised user-agent string MicrosoftAppStore/2001.0. (‘Communicates with C2 via HTTP; uses MicrosoftAppStore/2001.0 User-Agent.’)
- [T1005] Data from Local System – Exfiltrates system details and files as instructed by the C2 operator. (‘Exfiltrates system details and file contents as per threat actor’s command triggers.’)
- [T1041] Exfiltration Over C2 Channel – Sends POST requests with encoded command results or exfiltrated data to C2 server. (‘POST requests to /result endpoint on C2 with encoded command results or exfiltrated data.’)
- [T1537] Data Exfiltration – Targeted data theft from the Russian aerospace sector. (‘Targeted data theft from Russian aerospace sector.’)
Indicators of Compromise
- [File Hashes] Malicious LNK and DLL files – 4d4304d7ad1a8d0dacb300739d4dcaade299b28f8be3f171628a7358720ca6c5 (.LNK), 01f12bb3f4359fae1138a194237914f4fcdbf9e472804e428a765ad820f399be (.DLL)
- [File Names] Spear-phishing files – Транспортная_накладная_ТТН_№391-44_от_26.06.2025.xls.lnk, Договор_РН83_изменения.pdf.lnk
- [Email File] Malicious email file – backup-message-10.2.2.20_9045-800282.eml originating from Russian Federation targeting VASO employee
- [IP Address] Command-and-control server – 185.225.17.104 located in Romania under ASN 39798 MivoCloud SRL
- [Decoy Files] Embedded XLS decoy – sample_extracted.xls and temp.pdf mimicking Russian logistics documentation