Lumma Stealer malware has resurfaced soon after a major law enforcement takedown, utilizing stealthier tactics and diversified delivery methods to regain its reach. The threat actors behind it, including the group known as Water Kurita, continue to innovate their infrastructure and campaigns, posing ongoing risks to users and organizations. #LummaStealer #WaterKurita #TrendVisionOne
Keypoints
- Lumma Stealer re-emerged shortly after a May 2025 takedown that seized 2,300 malicious domains and disrupted its command-and-control infrastructure.
- The operators, identified internally as Water Kurita, adapted by employing more covert delivery channels such as fake cracks, ClickFix campaigns, GitHub repositories, and social media links.
- The malware-as-a-service model enables even low-skilled cybercriminals to distribute Lumma Stealer, increasing its infection potential.
- Recent campaigns use advanced evasion techniques like in-memory execution of payloads to avoid detection by traditional security tools.
- Lumma Stealer domains have shifted from heavy Cloudflare use to alternative providers, including Russian-based Selectel, to complicate law enforcement tracking.
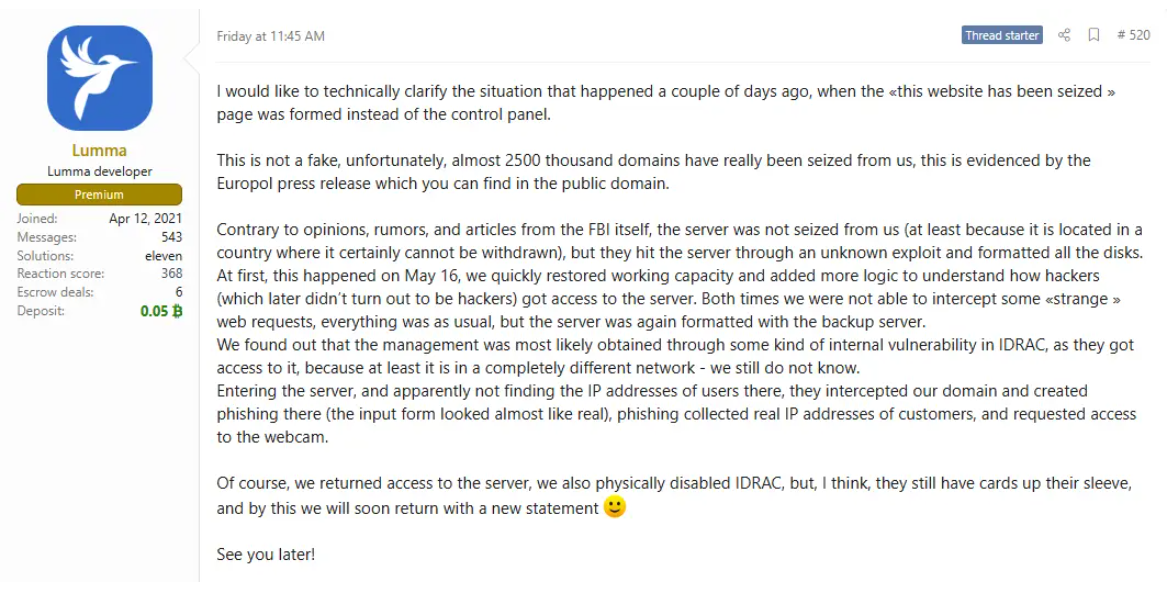
- The operators issued a detailed statement after the takedown, revealing law enforcement exploited a vulnerability in their server’s remote management interface to format disks and replace control panels.
- Trend Vision One detects and blocks Lumma Stealer IOCs and offers threat hunting queries and intelligence reports to assist defenders.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Attackers used PowerShell commands via fake CAPTCHA pages to execute Lumma Stealer payloads. (‘…causing them to display a fake CAPTCHA page… designed to deceive users into executing a malicious PowerShell command…’)
- [T1047] Windows Management Instrumentation – The operator exploited the Integrated Dell Remote Access Controller (IDRAC) vulnerability to gain control and wipe servers. (‘…law enforcement did not physically confiscate their server… authorities allegedly exploited a previously unknown vulnerability, suspected in the server’s IDRAC… to format all disks.’)
- [T1129] Execution through API – The ClickFix campaign decrypted and executed a .NET assembly binary directly in memory using an XOR operation, avoiding disk writes. (‘…load the decrypted program directly into memory, and then execute it, allowing Lumma to run without saving any files to disk…’)
- [T1090] Proxy – Prior use of Cloudflare to conceal true server origin, later reduced to avoid popular infrastructure for better evasion. (‘…leveraged Cloudflare’s infrastructure to obfuscate their malicious domains… operators might be intentionally reducing their reliance on more popular companies…’)
- [T1218] Signed Binary Proxy Execution – Delivery through trusted platforms like GitHub and sites.google.com to obscure direct malware downloads. (‘…repositories promote downloads… and abusing the legitimate sites.google.com platform…’)
Indicators of Compromise
- [Domains] Malicious C&C infrastructure – Over 2,300 domains seized or blocked, including those used as Lumma Stealer login panels; examples include domains hosted on Selectel and former Cloudflare domains.
- [File Hashes] Lumma Stealer binaries – Examples include “TempSpoofer.exe” and password-protected Lumma Downloader files used in campaigns.
- [URLs] Delivery sites – Fake crack websites, GitHub repository URLs hosting Lumma Stealer executables, and social media links directing to malicious download pages.
- [Scripts] PowerShell commands – Examples used in ClickFix campaigns to decrypt and run payloads in memory.
Read more: https://www.trendmicro.com/en_us/research/25/g/lumma-stealer-returns.html