Kaspersky MDR detected a sophisticated APT41 cyberespionage campaign targeting African government IT services, involving custom and publicly available tools such as Cobalt Strike, Pillager, and Mimikatz. The attackers leveraged internal infrastructure for command and control communication, performed credential dumping, lateral movement, and data exfiltration through a compromised SharePoint server. #APT41 #CobaltStrike #Pillager #SharePoint #Mimikatz
Keypoints
- APT41 targeted government IT infrastructure in Africa using malware with hardcoded internal service names and IP addresses, including a captive SharePoint server as a C2.
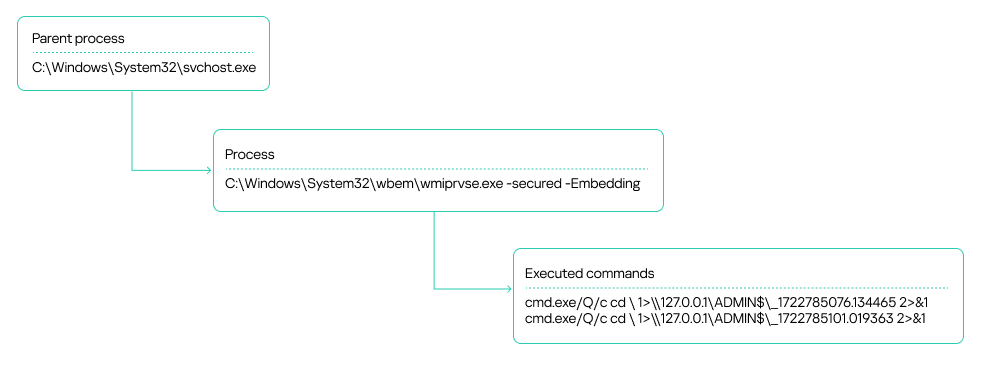
- Detection involved identifying Impacket toolkit modules (WmiExec and Atexec) executing suspicious commands from compromised hosts, some unmonitored, using service accounts.
- Attackers performed privilege escalation, dumping SYSTEM and SAM registry hives, and used domain accounts with elevated privileges for lateral movement and tool deployment.
- Cobalt Strike was deployed via DLL sideloading of legitimate applications, encrypted payloads were decrypted in-memory, and persistence was established using disguised Windows services.
- A custom C# agent communicated with a SharePoint web shell for reconnaissance and data exfiltration, including browser history, documents, and configuration files.
- Additional tools used included Pillager and Checkout stealers for harvesting credentials and sensitive data, RawCopy for raw registry file extraction, and a DLL-loaded version of Mimikatz for credential dumping.
- Attackers established a reverse shell via a malicious HTA file downloaded from a GitHub-impersonating domain to maintain command shell access.
- Retrospective analysis found Neo-reGeorg web shell tunnels enabling external network traffic proxying via compromised IIS servers within the victim’s infrastructure.
- Attack attribution to APT41 was based on tooling, TTPs, and C2 infrastructure similarities, emphasizing the need for comprehensive monitoring and strict privilege management to prevent such attacks.
MITRE Techniques
- [T1078.002] Valid Accounts: Domain Accounts – Used to move laterally with domain accounts holding local and domain admin privileges (“two domain accounts obtained from a registry dump were leveraged for lateral movement”).
- [T1190] Exploit Public-Facing Application – Utilized compromised SharePoint server as C2 and web shell CommandHandler.aspx for command execution.
- [T1059.001] Command and Scripting Interpreter: PowerShell – Usage implied by scripted commands and execution of tools.
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – cmd.exe invoked for command execution and file operations (“cmd.exe /c netstat -ano…”).
- [T1053.005] Scheduled Task/Job: Scheduled Task – Attackers created scheduled tasks to execute their tools persistently (“Scheduler tasks created by Atexec”).
- [T1047] Windows Management Instrumentation – Leveraged WMI for remote command execution and lateral movement (“executed remotely using the WMI toolkit”).
- [T1543.003] Create or Modify System Process: Windows Service – Established persistent services disguised with names like “server power” (“sc create ‘server power’ …”).
- [T1574.002] Hijack Execution Flow: DLL Side-Loading – Malicious DLLs loaded via legitimate executables to decrypt and launch payloads (“DLL sideloading used with legitimate apps”).
- [T1505.003] Web Shell – CommandHandler.aspx web shell used on SharePoint for executing attacker commands.
- [T1505.004] IIS Components – Compromised IIS server hosted Neo-reGeorg web shell tunnels.
- [T1055] Process Injection – Loading and executing malicious code in memory (“payload launched by allocating memory and creating a new thread”).
- [T1140] Deobfuscate/Decode Files or Information – Decryption of encrypted payload files in-memory (“payload decrypted by repeatedly executing instructions”).
- [T1036] Masquerading – Use of renamed legitimate executables and services for concealment (“cookie_exporter.exe renamed to Edge.exe”).
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – Harvested saved browser credentials using Pillager and Checkout tools.
- [T1003.002] OS Credential Dumping: Security Account Manager – Dumped SAM and SYSTEM registry hives using reg.exe and RawCopy.
- [T1570] Lateral Tool Transfer – Transferred tools over SMB to remote administrative shares (“used SMB protocol to transfer tools to administrative network share C$”).
- [T1021.002] Remote Services: SMB/Windows Admin Shares – Used for lateral movement and file transfer.
- [T1560.001] Archive Collected Data: Archive via Utility – Tools archived stolen data (e.g., Checkout archives data as CheckOutData.zip).
- [T1071.001] Application Layer Protocol: Web Protocols – Used web protocols for command and control communication and exfiltration.
- [T1090.001] Proxy: Internal Proxy – Used internal proxy servers for probing C2 availability.
- [T1572] Protocol Tunneling – Neo-ReGeorg web shell tunneled traffic from external network to internal.
- [T1048] Exfiltration Over Alternative Protocol – Data exfiltrated via SMB protocol to SharePoint server shares.
- [T1567] Exfiltration Over Web Service – Data exfiltrated using web upload handlers like upload.ashx.
Indicators of Compromise
- [File Hashes] Malware and tools – sample hashes include 2CD15977B72D5D74FADEDFDE2CE8934F and several others representing Cobalt Strike payloads and stealer DLLs.
- [Domains] C2 and malicious infrastructure – github[.]githubassets[.]net, s3-azure[.]com, *.ns1.s3-azure[.]com, *.ns2.s3-azure[.]com, upload-microsoft[.]com, msn-microsoft[.]org, chyedweeyaxkavyccenwjvqrsgvyj0o1y.oast[.]fun.
- [IP Addresses] Attack-related IPs – examples: 47.238.184[.], 938.175.195[.].
- [File Names] Malicious files – agents.exe, agentx.exe (C# Trojans), Pillager.zip, CheckOutData.zip, Cobalt Strike encrypted payload files with extensions like .ini, .txt, .log.
- [Paths] Common file and persistence locations – C:WindowsTasks, C:ProgramData, C:UsersPublicDownloads, C:WindowsTemp, C:WindowsMicrosoft.NETFramework64v4.0.30319Temporary ASP.NET Files.
- [Scripts] Malicious scripts and web shells – CommandHandler.aspx (SharePoint web shell), newfile.aspx (Neo-reGeorg web shell), 123.bat (Mimikatz launcher).