Ransomware gangs have increasingly exploited legitimate Remote Monitoring and Management (RMM) tools to gain persistent access, conduct lateral movement, and exfiltrate data in enterprise networks. Real-world incidents demonstrate how these trusted tools are misused to bypass security controls, complicating threat detection and response. #HuntersInternational #Medusa #AnyDesk #ScreenConnect #SimpleHelp
Keypoints
- Ransomware gangs leverage commercial and open-source RMM tools for initial access, persistence, lateral movement, and data exfiltration in enterprise environments.
- RMM tools have capabilities similar to Remote Access Trojans but benefit from trusted status and legitimate presence, making malicious activity harder to detect.
- Analysis of multiple ransomware campaigns identified repeated misuse of RMM tools such as AnyDesk, ScreenConnect, PDQ Deploy, and SimpleHelp.
- Three real-world incidents involved the Hunters International, Medusa, and an unknown ransomware gang exploiting RMM tools to maintain access and move laterally across networks.
- Detection methods include monitoring network traffic patterns, anomaly detection of WAN-bound RMM connections, and behavioral analysis via tools like Cato XDR.
- Security best practices to mitigate RMM misuse include strict access controls, allowlisting approved tools, privilege limitation, anomaly monitoring, and regular audits.
- The boundary between authorized RMM usage and malicious exploitation depends on intent, requiring enhanced visibility and operational controls to defend effectively.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used native administrative features in RMM tools to run commands and deploy payloads remotely (‘Remote Execution and Script Deployment used to run commands, deploy payloads, and establish persistence’).
- [T1071] Application Layer Protocol – Utilized cloud and peer-to-peer communication models of RMM tools that complicate detection and attribution (‘Connection Models: Cloud and peer-to-peer configurations that complicate detection and attribution’).
- [T1543] Create or Modify System Process – Maintained stealth access through hidden terminal sessions and silent execution capabilities in RMM tools (‘Stealth Access enabled by support for hidden terminal sessions and silent execution’).
- [T1086] PowerShell – Exploited phishing-delivered LNK files to launch PowerShell commands initiating RMM tool connections for persistence (‘The phishing email contains an LNK file that launches a PowerShell command’).
- [T1021] Remote Services – Leveraged legitimate remote access services provided by RMM tools like AnyDesk and ScreenConnect for lateral movement and persistence (‘Multiple RMM tools were used simultaneously to diversify capabilities and maintain persistence’).
Indicators of Compromise
- [File Names] RMM tools used in attacks – AnyDesk, ScreenConnect, SimpleHelp, PDQ Deploy.
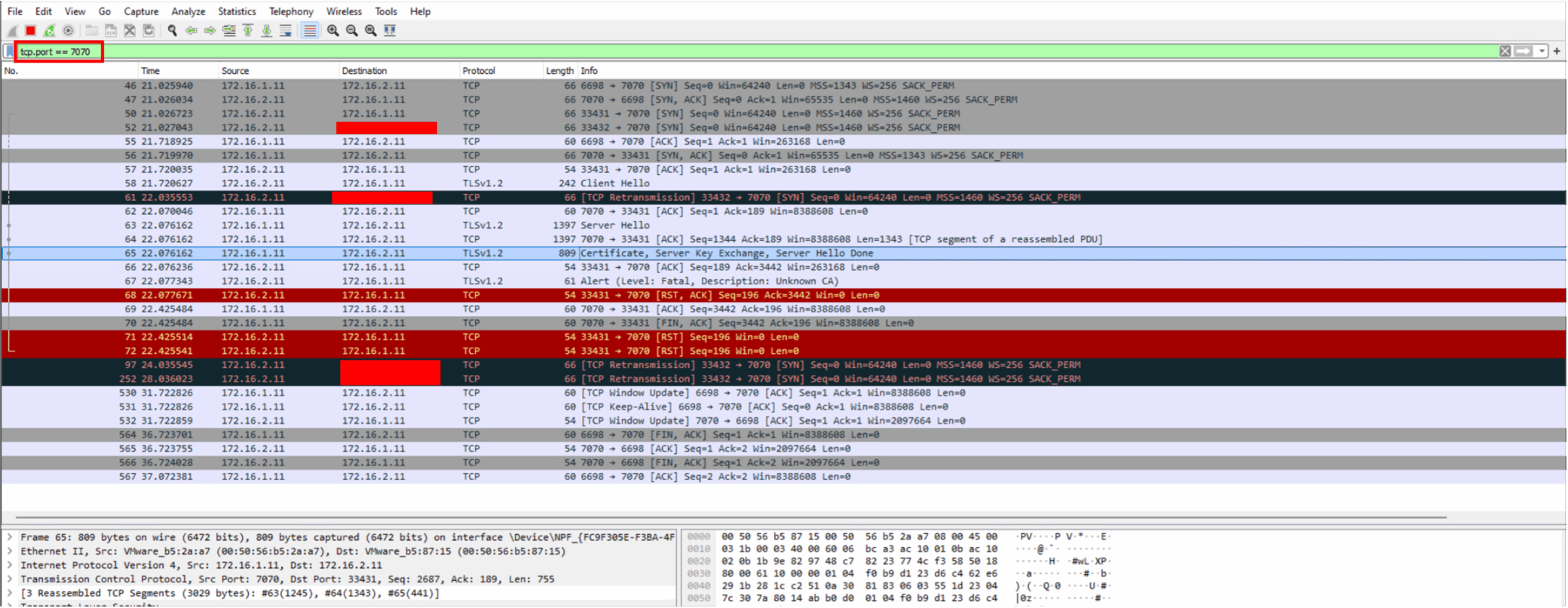
- [Network Traffic] Suspicious WAN-bound connections – AnyDesk traffic detected on port 7070 indicating remote control sessions.
- [Email Artifacts] Phishing LNK files – LNK files launching PowerShell commands used to initiate RMM sessions.
Read more: https://www.catonetworks.com/blog/cato-ctrl-investigation-of-rmm-tools/